Alert Fatigue in SOC Teams: Causes, Risks, and How to Fix It
Updated on March 24, 2026, by Xcitium
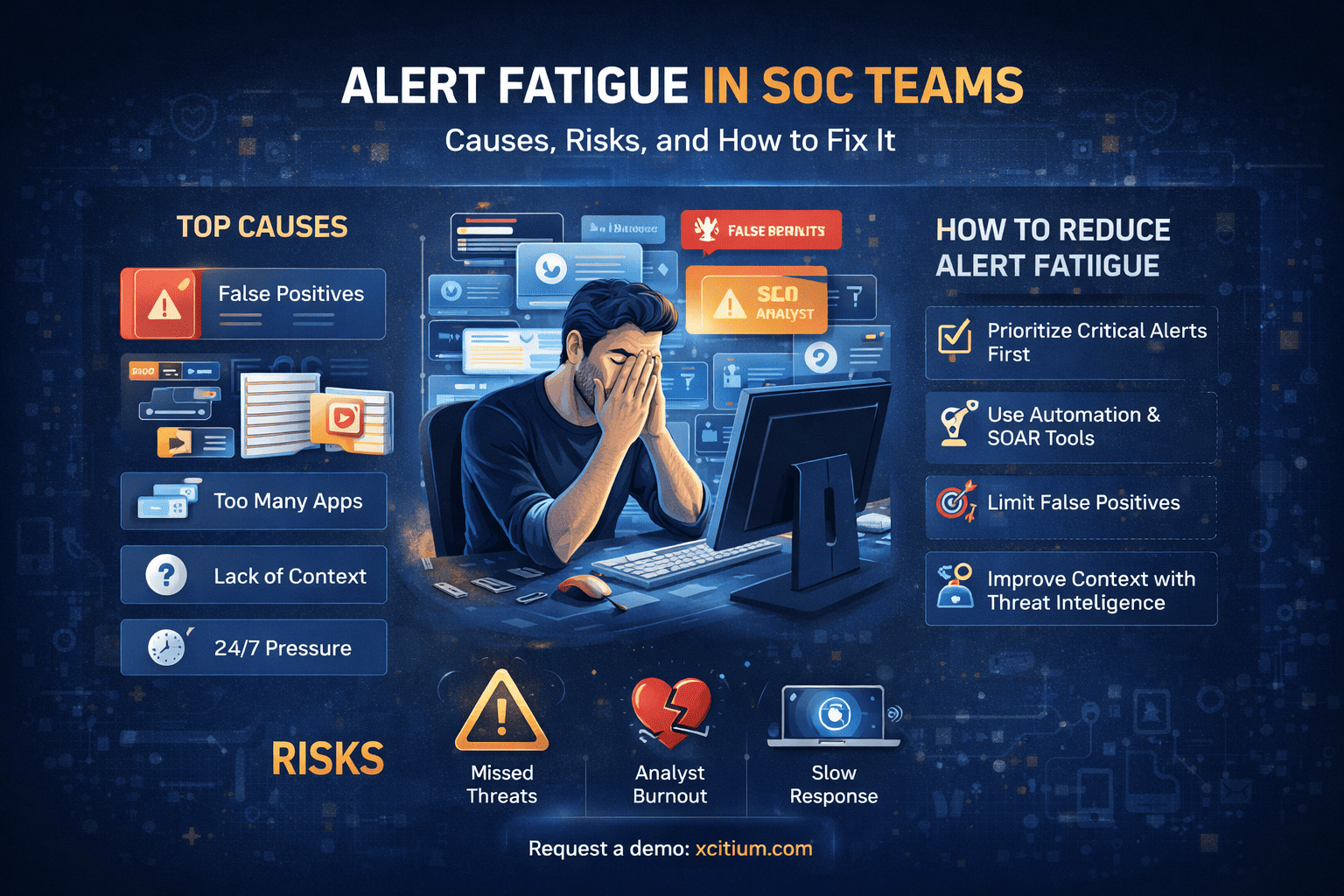
Security Operations Centers (SOCs) are the backbone of modern cybersecurity. But what happens when analysts are overwhelmed by too many alerts? Alert fatigue in SOC teams has become a serious challenge, affecting detection accuracy, response time, and overall security posture.
If your team is missing critical threats or struggling to keep up with alerts, you’re not alone. Many organizations face the same issue—and the consequences can be severe.
In this guide, we’ll break down what alert fatigue is, why it happens, and how you can fix it effectively.
What Is Alert Fatigue in SOC Teams?
Alert fatigue in SOC teams occurs when security analysts are overwhelmed by a high volume of alerts, many of which are false positives or low priority.
Over time, this constant stream of alerts leads to:
- Desensitization to warnings
- Slower response times
- Missed critical threats
Instead of improving security, excessive alerts can actually weaken your defenses.
Why Alert Fatigue Is a Growing Problem
Modern IT environments are more complex than ever. With cloud systems, remote work, and IoT devices, the number of security events has exploded.
Key Reasons Behind Alert Fatigue:
- Too Many Security Tools
Organizations often use multiple tools (SIEM, EDR, firewalls), each generating alerts independently. - High False Positive Rates
Many alerts do not represent real threats, wasting analysts’ time. - Lack of Context
Alerts without proper context force analysts to investigate unnecessarily. - 24/7 Monitoring Pressure
SOC teams work around the clock, leading to burnout and reduced efficiency.
Top Challenges Caused by Alert Fatigue in SOC Teams
When alert fatigue in SOC teams goes unmanaged, it creates serious operational and security risks.
🔹 1. Missed Critical Threats
Important alerts can get buried under thousands of low-priority notifications.
🔹 2. Analyst Burnout
Constant pressure leads to stress, fatigue, and high turnover rates.
🔹 3. Slower Incident Response
Delayed responses increase the risk of data breaches.
🔹 4. Reduced Productivity
Analysts spend more time filtering alerts than investigating real threats.
How to Reduce Alert Fatigue in SOC Teams
The good news? Alert fatigue in SOC teams can be managed with the right strategies and tools.
1. Implement Alert Prioritization
Not all alerts are equal. Use risk-based scoring to prioritize:
- Critical threats first
- High-risk vulnerabilities
- Known attack patterns
This helps analysts focus on what truly matters.
2. Reduce False Positives
False positives are a major contributor to alert fatigue.
To reduce them:
- Fine-tune detection rules
- Use machine learning-based filtering
- Continuously update threat intelligence
3. Use Automation and SOAR Tools
Security Orchestration, Automation, and Response (SOAR) tools can:
- Automatically triage alerts
- Execute predefined responses
- Reduce manual workload
This significantly lowers alert volume for analysts.
4. Consolidate Security Tools
Too many tools create noise. Instead:
- Integrate platforms into a unified system
- Use centralized dashboards
- Correlate alerts across tools
This improves visibility and reduces duplication.
5. Improve Context with Threat Intelligence
Context is key to faster decisions.
Enhance alerts with:
- Threat intelligence feeds
- Behavioral analytics
- Historical data
This helps analysts quickly identify real threats.
Best Practices for SOC Alert Management
To effectively combat alert fatigue in SOC teams, follow these best practices:
✅ Establish Clear Alert Policies
Define which alerts require immediate action.
✅ Continuous Rule Tuning
Regularly review and update detection rules.
✅ Train SOC Analysts
Provide ongoing training to improve efficiency.
✅ Monitor Analyst Workload
Avoid overloading team members.
✅ Use Metrics and KPIs
Track:
- Alert volume
- Response time
- False positive rate
The Role of AI and Advanced Security Solutions
Modern cybersecurity solutions use AI to address alert fatigue in SOC teams.
Benefits of AI-Driven Security:
- Intelligent alert correlation
- Automated threat detection
- Reduced manual intervention
- Faster incident response
Solutions like Xcitium’s Zero Trust platform help organizations:
- Minimize false positives
- Automate threat containment
- Improve SOC efficiency
Real-World Example of Alert Fatigue
Imagine a SOC receiving 10,000 alerts per day.
- 90% are false positives
- Analysts investigate hundreds daily
- A real ransomware alert gets ignored
This is exactly how breaches happen—not due to lack of tools, but due to overload.
Future of SOC: Moving Beyond Alert Overload
The future of SOC operations focuses on:
- Automation-first security models
- Zero Trust architecture
- AI-driven threat detection
Organizations that adopt these approaches can drastically reduce alert fatigue in SOC teams and improve security outcomes.
Conclusion
Alert fatigue in SOC teams is more than just an operational issue—it’s a serious cybersecurity risk.
By reducing false positives, automating processes, and prioritizing alerts, organizations can:
- Improve threat detection
- Enhance analyst productivity
- Strengthen overall security posture
Ignoring alert fatigue is no longer an option in today’s threat landscape.
🚀 Take Control of Your SOC Today
Struggling with alert overload? It’s time to modernize your security operations.
👉 Request a demo now: https://www.xcitium.com/request-demo/
FAQs: Alert Fatigue in SOC Teams
1. What causes alert fatigue in SOC teams?
Alert fatigue is caused by excessive alerts, high false positives, and lack of proper prioritization.
2. How can organizations reduce alert fatigue?
By using automation, improving alert prioritization, and reducing false positives through better rule tuning.
3. Why is alert fatigue dangerous?
It can lead to missed threats, slower response times, and increased risk of cyberattacks.
4. What tools help manage SOC alerts?
SIEM, SOAR, and AI-driven security platforms help manage and reduce alert overload.
5. How does AI help with alert fatigue?
AI filters noise, prioritizes threats, and automates responses, reducing manual workload.