Vulnerability Management Lifecycle
Updated on March 17, 2026, by Xcitium
Cyberattacks rarely happen without warning. In most cases, attackers exploit known security weaknesses that organizations failed to fix. According to cybersecurity reports, thousands of new vulnerabilities are discovered every year, and many remain unpatched for months. This is why understanding the vulnerability management lifecycle is critical for modern cybersecurity.
The vulnerability management lifecycle is a structured process used by organizations to identify, assess, prioritize, remediate, and monitor security vulnerabilities within their IT infrastructure. Instead of reacting to attacks after they occur, vulnerability management focuses on proactively reducing security risks before attackers exploit them.
For cybersecurity professionals, IT managers, and business leaders, implementing an effective vulnerability management program can significantly strengthen security posture and prevent costly breaches. In this guide, we’ll explore the stages of the vulnerability management lifecycle, why it matters, and how organizations can implement best practices to reduce cyber risk.
What is Vulnerability Management?
Vulnerability management is the continuous process of discovering and fixing security weaknesses across systems, networks, applications, and devices.
Unlike occasional security scans, vulnerability management is an ongoing strategy designed to improve security over time.
Why Vulnerability Management Matters
Modern IT environments are complex. Organizations often manage:
-
Cloud infrastructure
-
Endpoints and servers
-
Web applications
-
Mobile devices
-
Network systems
Each component may contain vulnerabilities that attackers can exploit.
The vulnerability management lifecycle helps security teams maintain visibility and control over these risks.
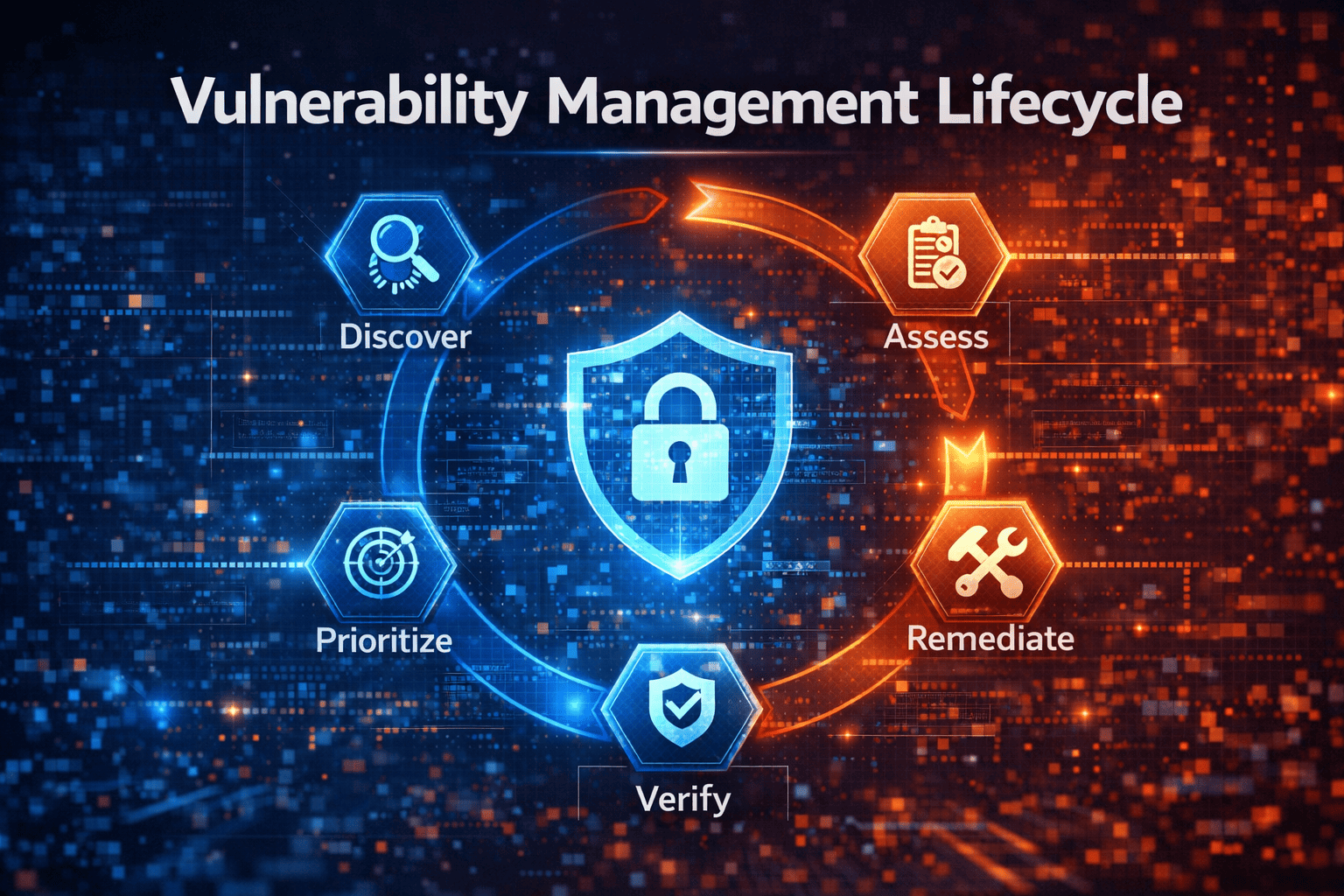
What is the Vulnerability Management Lifecycle?
The vulnerability management lifecycle refers to the structured stages organizations follow to identify and address vulnerabilities.
This lifecycle typically includes several continuous steps that repeat over time.
Core Stages of the Vulnerability Management Lifecycle
Most cybersecurity frameworks include the following stages:
-
Asset discovery
-
Vulnerability identification
-
Risk assessment and prioritization
-
Remediation and mitigation
-
Verification and reporting
-
Continuous monitoring
These stages form a cyclical process that ensures security improvements never stop.
Stage 1: Asset Discovery and Inventory
The first step in the vulnerability management lifecycle is identifying all assets within the organization’s IT environment.
Why Asset Visibility is Important
You cannot secure what you cannot see.
Security teams must identify all systems connected to the network, including:
-
Servers
-
Endpoints
-
IoT devices
-
Cloud workloads
-
Network equipment
-
Applications and databases
Without accurate asset inventory, vulnerabilities may remain hidden.
Tools Used for Asset Discovery
Organizations often use automated tools to detect connected assets, such as:
-
Network scanners
-
Endpoint management platforms
-
Asset discovery tools
These tools help create a complete picture of the attack surface.
Stage 2: Vulnerability Identification
Once assets are identified, the next stage in the vulnerability management lifecycle involves scanning systems to detect vulnerabilities.
What Are Security Vulnerabilities?
A vulnerability is a weakness in software, hardware, or configuration that attackers can exploit.
Common vulnerabilities include:
-
Outdated software versions
-
Misconfigured servers
-
Weak authentication settings
-
Unpatched operating systems
Vulnerability scanners analyze systems to identify these weaknesses.
Vulnerability Scanning Tools
Organizations use automated scanners to detect vulnerabilities, including:
-
Network vulnerability scanners
-
Web application scanners
-
Cloud security scanners
-
Endpoint vulnerability assessment tools
These tools compare systems against known vulnerability databases.
Stage 3: Risk Assessment and Prioritization
Not every vulnerability poses the same level of risk. Some may be critical, while others have minimal impact.
The vulnerability management lifecycle includes prioritization to ensure security teams address the most dangerous vulnerabilities first.
Factors Used in Risk Assessment
Security teams evaluate vulnerabilities based on:
-
Severity scores (CVSS ratings)
-
Exploit availability
-
Potential business impact
-
Exposure to the internet
-
System criticality
This process helps organizations focus resources on the most urgent threats.
Example of Vulnerability Prioritization
For example:
-
A vulnerability affecting a public-facing web server may be high priority
-
A vulnerability on an isolated internal system may be lower priority
Effective prioritization helps organizations respond faster to serious threats.
Stage 4: Remediation and Mitigation
After vulnerabilities are prioritized, organizations begin fixing them.
Remediation is a critical stage of the vulnerability management lifecycle.
Common Remediation Actions
Security teams may take several actions to resolve vulnerabilities:
-
Installing security patches
-
Updating software versions
-
Changing system configurations
-
Removing vulnerable applications
-
Strengthening authentication policies
The goal is to eliminate vulnerabilities before attackers exploit them.
When Immediate Fixes Are Not Possible
In some cases, systems cannot be patched immediately.
Organizations may implement temporary mitigation strategies, such as:
-
Network segmentation
-
Access restrictions
-
Intrusion detection monitoring
These controls reduce risk until permanent fixes are deployed.
Stage 5: Verification and Reporting
Once vulnerabilities are addressed, security teams must confirm that remediation efforts were successful.
Vulnerability Validation
This step involves rescanning systems to ensure vulnerabilities have been eliminated.
Verification prevents security teams from assuming a problem has been fixed when it still exists.
Security Reporting
Security teams generate reports to track progress and communicate results to stakeholders.
Reports typically include:
-
Number of vulnerabilities discovered
-
Remediation timelines
-
Risk reduction metrics
-
Compliance status
Clear reporting helps organizations maintain accountability and improve security processes.
Stage 6: Continuous Monitoring
The final stage of the vulnerability management lifecycle is ongoing monitoring.
Cyber threats evolve rapidly, and new vulnerabilities appear constantly.
Continuous monitoring ensures organizations remain protected.
Continuous Vulnerability Monitoring
Security teams should regularly perform:
-
Scheduled vulnerability scans
-
Threat intelligence monitoring
-
Patch management reviews
-
Security configuration audits
This continuous cycle ensures that vulnerabilities are detected early and addressed quickly.
Challenges in Vulnerability Management
Although vulnerability management is essential, organizations often face several challenges.
Large Attack Surfaces
Modern IT environments include cloud platforms, remote endpoints, and IoT devices.
Managing vulnerabilities across these systems can be difficult.
Alert Overload
Security teams may discover thousands of vulnerabilities during scans.
Prioritizing the most critical issues requires strong risk management strategies.
Limited Resources
Many organizations lack the personnel or tools required to maintain a comprehensive vulnerability management program.
Automation and security platforms can help address these challenges.
Best Practices for Effective Vulnerability Management
Organizations can improve their vulnerability management strategy by following proven best practices.
1. Automate Vulnerability Scanning
Automated tools help security teams detect vulnerabilities faster and more consistently.
2. Prioritize Based on Risk
Focus on vulnerabilities that pose the highest risk to business operations.
3. Integrate Threat Intelligence
Threat intelligence helps identify vulnerabilities actively exploited by attackers.
4. Maintain a Strong Patch Management Program
Prompt patching reduces the risk of exploitation.
5. Conduct Regular Security Audits
Periodic audits help verify that security controls remain effective.
Benefits of a Strong Vulnerability Management Program
Implementing a structured vulnerability management lifecycle provides several advantages.
Improved Cybersecurity Posture
Organizations reduce their exposure to cyber threats by addressing vulnerabilities proactively.
Reduced Risk of Data Breaches
Many cyberattacks exploit known vulnerabilities. Fixing these weaknesses prevents attackers from gaining access.
Better Compliance
Many regulatory frameworks require organizations to perform vulnerability assessments and remediation.
Increased Operational Stability
Patching vulnerabilities improves system reliability and reduces downtime.
Frequently Asked Questions (FAQ)
What is the vulnerability management lifecycle?
The vulnerability management lifecycle is a continuous process used to identify, assess, prioritize, and remediate security vulnerabilities within an organization’s systems.
Why is vulnerability management important?
Vulnerability management helps organizations detect security weaknesses before attackers exploit them, reducing the risk of cyberattacks and data breaches.
How often should vulnerability scans be performed?
Most organizations conduct vulnerability scans regularly—often weekly or monthly—depending on the size and complexity of their IT environment.
What tools are used in vulnerability management?
Common tools include vulnerability scanners, patch management systems, endpoint security platforms, and threat intelligence tools.
What is the difference between vulnerability assessment and vulnerability management?
Vulnerability assessment identifies security weaknesses, while vulnerability management is the continuous process of detecting, prioritizing, and fixing those vulnerabilities.
Strengthen Your Vulnerability Management Strategy
Cyber threats are constantly evolving, and organizations must stay ahead by identifying and fixing vulnerabilities before attackers exploit them. A well-implemented vulnerability management lifecycle helps security teams reduce risks, improve compliance, and protect critical systems.
Want to see how advanced cybersecurity solutions can help you detect and eliminate vulnerabilities faster?
👉 Request a demo today:
https://www.xcitium.com/request-demo/
Discover how modern threat detection and vulnerability management solutions can strengthen your cybersecurity defenses and protect your organization from emerging threats.