IoT Security Challenges in 2026
Updated on March 20, 2026, by Xcitium
What happens when billions of connected devices become entry points for cyberattacks? As we move deeper into a hyper-connected world, IoT security challenges in 2026 are becoming more complex and harder to manage.
From smart homes and wearable devices to industrial systems and healthcare equipment, the Internet of Things (IoT) is transforming industries. However, this rapid growth also expands the attack surface, making IoT ecosystems highly vulnerable.
For IT managers, cybersecurity professionals, CEOs, and industry leaders, understanding IoT security challenges in 2026 is critical. Without proper safeguards, these devices can become gateways for data breaches, ransomware attacks, and operational disruptions.
In this guide, we’ll explore the biggest IoT security challenges in 2026, emerging threats, and actionable strategies to secure connected environments.
What is IoT Security?
IoT security refers to the technologies and practices used to protect connected devices and networks from cyber threats.
These devices include:
-
Smart home devices
-
Industrial sensors
-
Medical equipment
-
Connected vehicles
-
Wearables
The goal is to ensure data confidentiality, integrity, and availability across IoT ecosystems.
Why IoT Security Challenges Are Growing in 2026
The scale of IoT adoption is increasing rapidly.
Key Drivers of IoT Growth
-
Expansion of smart cities
-
Rise of industrial IoT (IIoT)
-
Increased use of connected healthcare devices
-
Growth in remote monitoring systems
As a result, IoT security challenges in 2026 are becoming more widespread and complex.
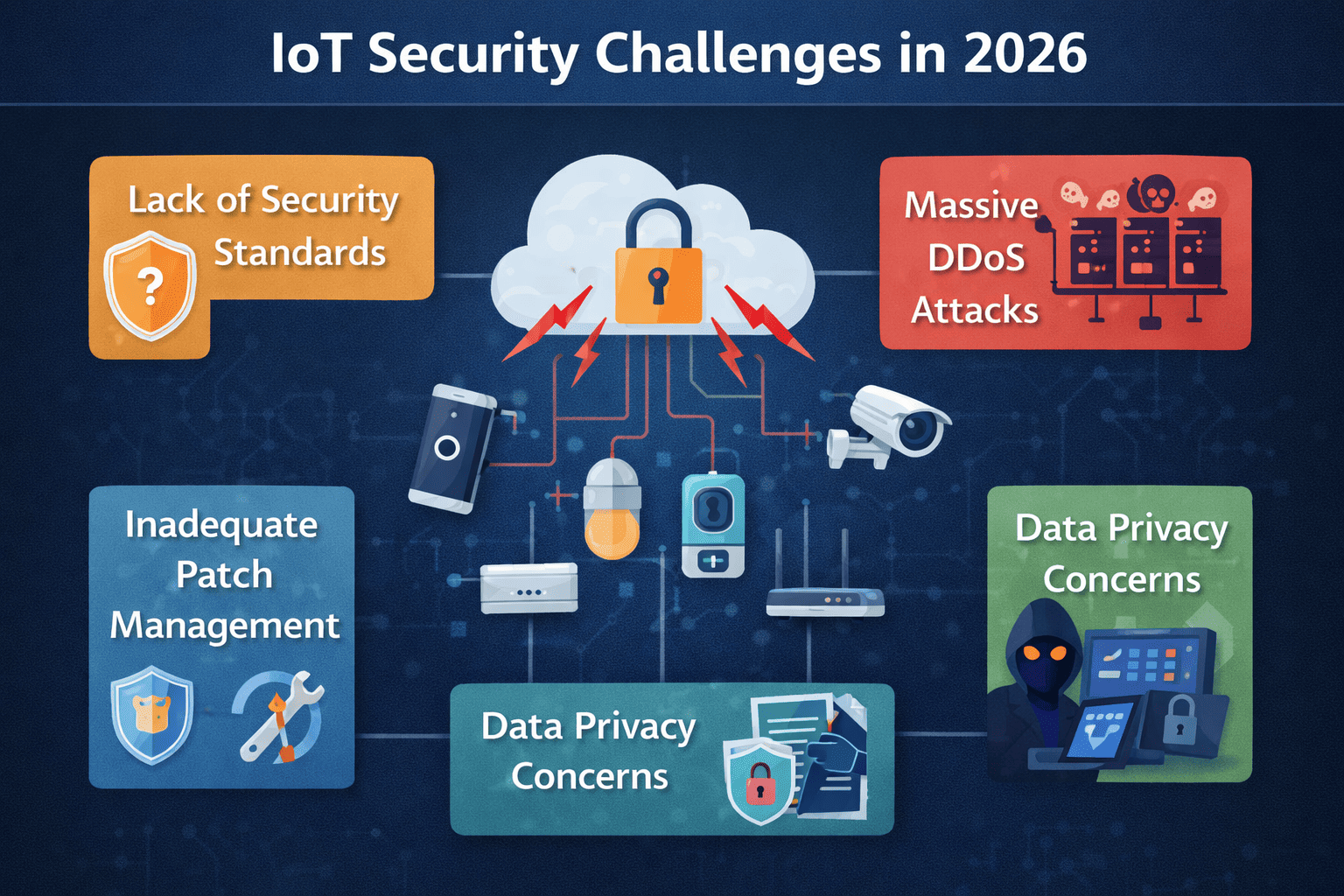
Top IoT Security Challenges in 2026
Organizations must address several critical challenges.
1. Massive Attack Surface Expansion
The number of IoT devices continues to grow exponentially.
Why This Is a Problem
Each connected device represents a potential entry point for attackers.
Risks Include:
-
Unauthorized access
-
Botnet attacks
-
Distributed Denial of Service (DDoS) attacks
Managing thousands of devices makes security more difficult.
2. Weak Device Security and Default Credentials
Many IoT devices are shipped with weak or default credentials.
Common Issues
-
Hardcoded passwords
-
Lack of authentication mechanisms
-
Insecure configurations
Attackers can easily exploit these vulnerabilities.
3. Lack of Regular Updates and Patch Management
Unlike traditional systems, many IoT devices do not receive regular updates.
Consequences
-
Known vulnerabilities remain unpatched
-
Devices become easy targets
-
Long-term security risks increase
This is one of the biggest IoT security challenges in 2026.
4. Limited Device Visibility and Management
Organizations often struggle to track all connected devices.
Challenges Include
-
Unknown devices on the network
-
Lack of centralized management
-
Difficulty monitoring device activity
Without visibility, detecting threats becomes harder.
5. Data Privacy Concerns
IoT devices collect large amounts of sensitive data.
Risks
-
Unauthorized data access
-
Data leaks
-
Privacy violations
Protecting data is a key part of IoT security.
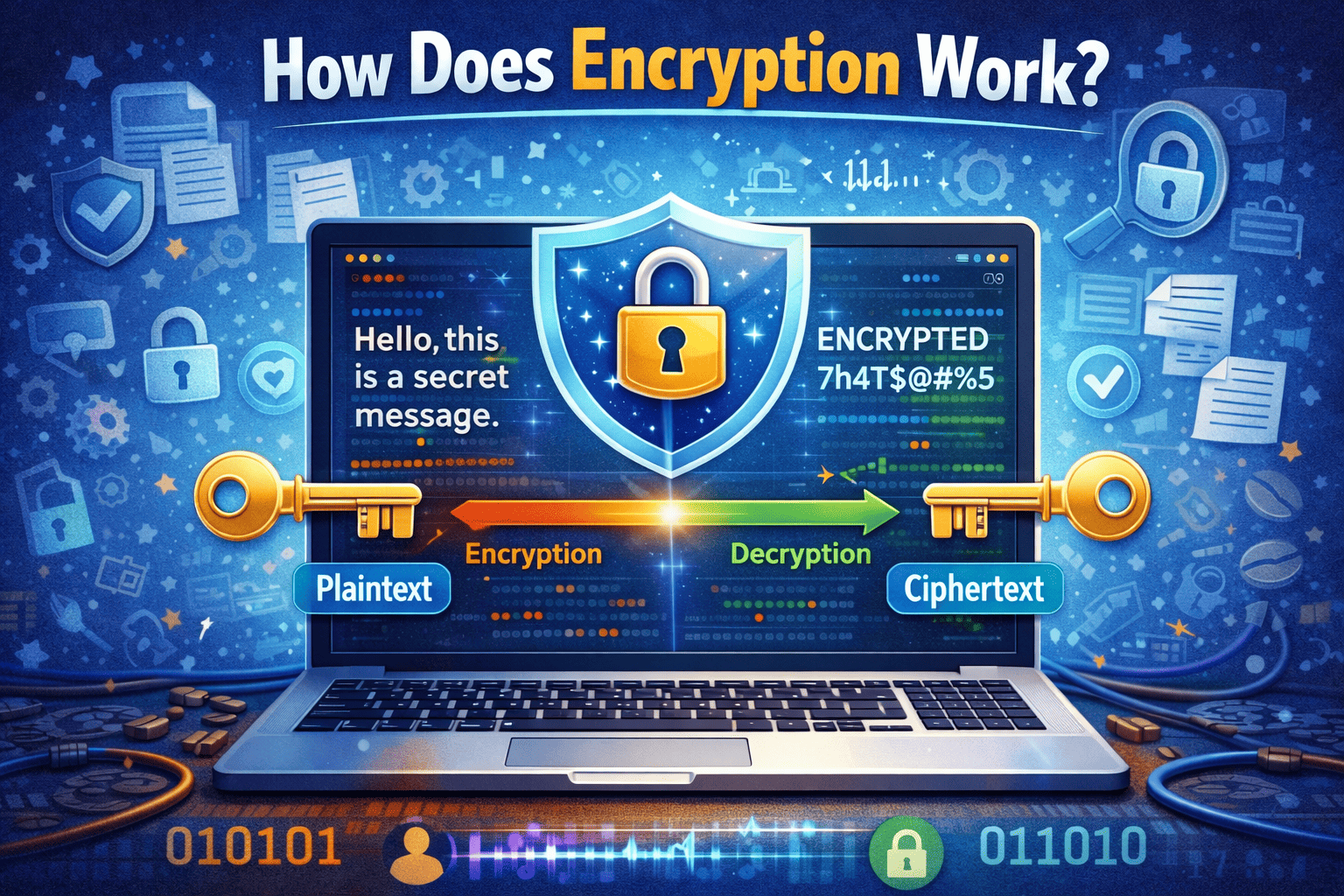
6. Insecure Communication Channels
Many IoT devices transmit data without proper encryption.
Potential Threats
-
Man-in-the-middle attacks
-
Data interception
-
Unauthorized data manipulation
Secure communication is essential.
7. Integration with Legacy Systems
Many IoT devices are connected to older systems.
Risks
-
Compatibility issues
-
Increased vulnerabilities
-
Difficulty implementing modern security measures
Legacy systems add complexity to IoT security.
8. Botnet and DDoS Attacks
IoT devices are often used in botnets.
Example
Compromised devices can be used to launch large-scale DDoS attacks.
9. Supply Chain Vulnerabilities
IoT devices often come from multiple vendors.
Risks Include
-
Insecure components
-
Lack of standardization
-
Hidden vulnerabilities
Supply chain security is a growing concern.
Emerging IoT Threats in 2026
Cybercriminals are evolving their tactics.
AI-Powered Attacks
Attackers use AI to automate and enhance attacks.
Ransomware Targeting IoT Devices
Ransomware can lock critical systems, including medical or industrial devices.
IoT-Based Espionage
Devices can be used to collect sensitive information.
Best Practices to Overcome IoT Security Challenges
Organizations must adopt proactive strategies.
1. Implement Strong Authentication
Replace default credentials with strong authentication methods.
Best Practices
-
Use unique passwords
-
Enable multi-factor authentication
-
Implement device identity management
2. Regularly Update and Patch Devices
Ensure devices receive updates.
3. Use Network Segmentation
Separate IoT devices from critical systems.
4. Encrypt Data and Communications
Use strong encryption protocols to protect data.
5. Monitor IoT Devices Continuously
Use monitoring tools to detect unusual activity.
6. Adopt Zero Trust Security
Verify every device and connection.
7. Conduct Regular Security Audits
Identify and fix vulnerabilities.
IoT Security in Different Industries
Different sectors face unique challenges.
Healthcare
Medical devices must be secured to protect patient safety.
Manufacturing
Industrial IoT systems must prevent operational disruptions.
Smart Cities
Infrastructure must be protected from large-scale attacks.
Retail
Connected systems must secure customer data.
A tailored approach is essential for addressing IoT security challenges in 2026.
The Future of IoT Security
IoT security is evolving rapidly.
Future trends include:
-
AI-driven threat detection
-
Automated security management
-
Blockchain for device authentication
-
Improved regulatory frameworks
Organizations must stay ahead of these changes.
Frequently Asked Questions (FAQ)
What are IoT security challenges in 2026?
They include device vulnerabilities, lack of updates, data privacy risks, and increased attack surfaces due to growing IoT adoption.
Why are IoT devices vulnerable?
Many devices lack strong security features, use default credentials, and do not receive regular updates.
How can organizations secure IoT devices?
By implementing strong authentication, encryption, monitoring, and network segmentation.
What industries are most affected by IoT security challenges?
Healthcare, manufacturing, smart cities, and retail are among the most impacted.
What is the biggest IoT security risk?
The rapid increase in connected devices, which expands the attack surface significantly.
Strengthen Your IoT Security Strategy Today
The rise of connected devices brings both opportunity and risk. Understanding IoT security challenges in 2026 is essential for protecting your organization from evolving threats.
By implementing strong security practices and staying informed, businesses can reduce risks and secure their IoT ecosystems.
👉 Request a demo today:
https://www.xcitium.com/request-demo/
Discover how advanced cybersecurity solutions can help you secure IoT environments and stay ahead of modern cyber threats.