Cybersecurity Budget Planning: A Strategic Guide for Modern Businesses
Updated on March 13, 2026, by Xcitium

Cyberattacks are no longer rare events—they are daily threats facing organizations of all sizes. From ransomware and phishing attacks to large-scale data breaches, businesses must constantly defend their digital infrastructure. Yet many organizations struggle with one key challenge: how to allocate resources effectively for cybersecurity. This is where cybersecurity budget planning becomes essential.
According to industry reports, the average cost of a data breach can reach millions of dollars. Despite this risk, many companies still underinvest in security or allocate budgets inefficiently. Effective cybersecurity budget planning helps organizations prioritize security initiatives, invest in the right technologies, and reduce overall risk exposure.
For IT managers, CISOs, and business leaders, cybersecurity spending should not be reactive—it must be strategic. Proper planning ensures that resources are directed toward the most critical vulnerabilities and security gaps.
In this guide, we will explore how organizations can approach cybersecurity budget planning, identify key investment areas, and build a sustainable security strategy that protects both data and business operations.
Why Cybersecurity Budget Planning Matters
Cybersecurity investments are no longer optional. As digital transformation accelerates, organizations rely heavily on interconnected systems, cloud services, and remote work environments.
Without proper cybersecurity budget planning, companies may face serious consequences.
Increasing Cyber Threats
Cybercriminals continuously develop new techniques to exploit system vulnerabilities.
Regulatory Compliance
Industries must comply with regulations such as:
-
HIPAA
-
GDPR
-
PCI DSS
-
ISO 27001
Compliance often requires specific security investments.
Protection of Critical Data
Organizations store valuable assets such as customer data, intellectual property, and financial records.
Business Continuity
Security incidents can cause operational disruptions that affect productivity and revenue.
Effective cybersecurity budget planning ensures that organizations can defend against these risks.
Key Factors Influencing Cybersecurity Budgets
When developing a cybersecurity budget, organizations must evaluate several factors.
Organizational Risk Profile
Every organization faces different types of cyber risks.
Risk factors may include:
-
Industry sector
-
Size of organization
-
Type of data stored
-
Regulatory obligations
Healthcare and financial organizations often require higher security investments due to sensitive data.
Existing Security Infrastructure
Organizations should assess their current cybersecurity tools before allocating new budget resources.
Key areas to review include:
-
Endpoint protection systems
-
Network security tools
-
Cloud security platforms
-
Identity and access management solutions
Understanding existing infrastructure helps identify gaps.
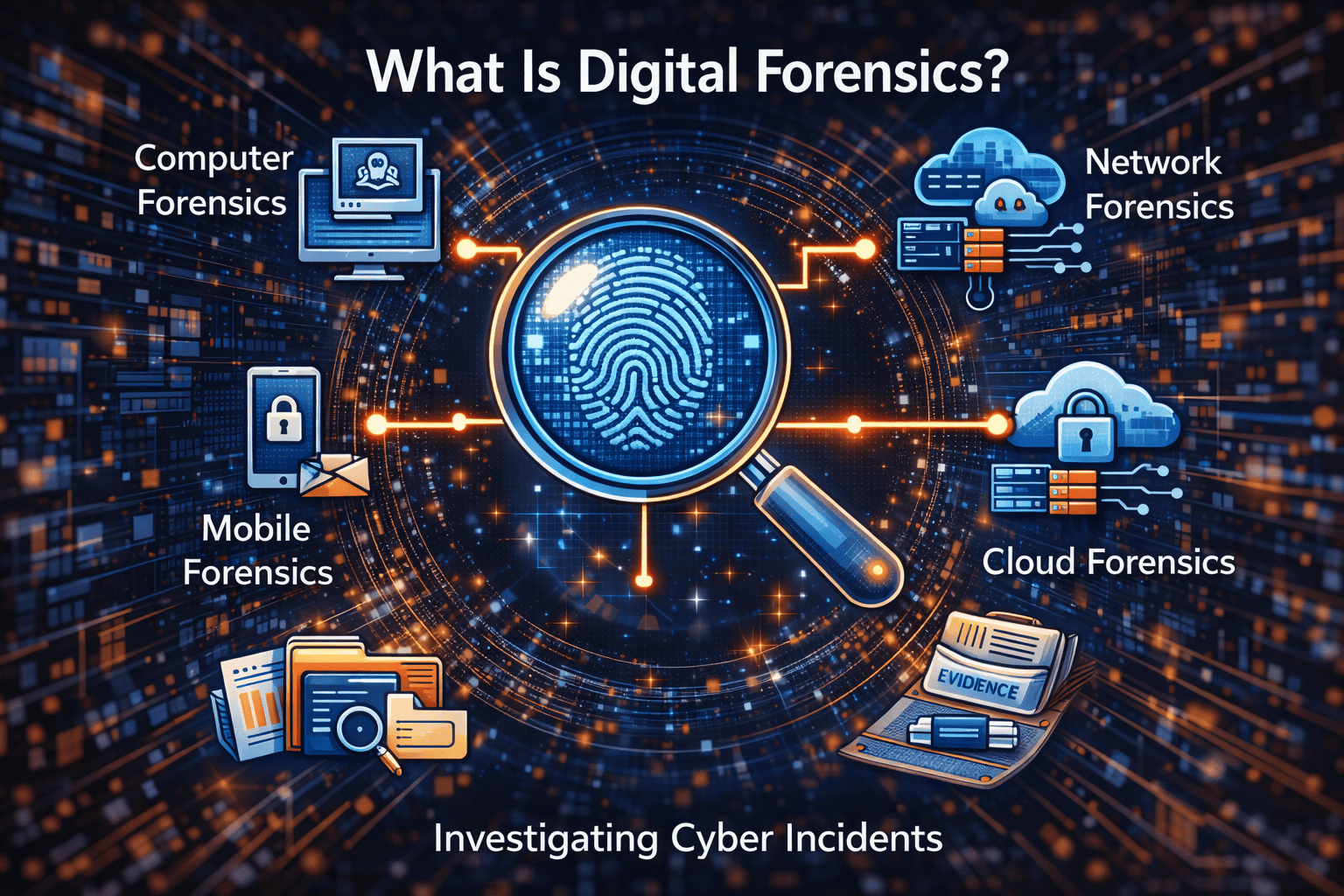
Threat Landscape
Cyber threats evolve constantly.
Organizations must analyze current attack trends such as:
-
Ransomware attacks
-
Supply chain attacks
-
Insider threats
-
Phishing campaigns
This analysis helps guide cybersecurity budget planning decisions.
Key Components of a Cybersecurity Budget
A strong cybersecurity strategy requires investment across multiple areas.
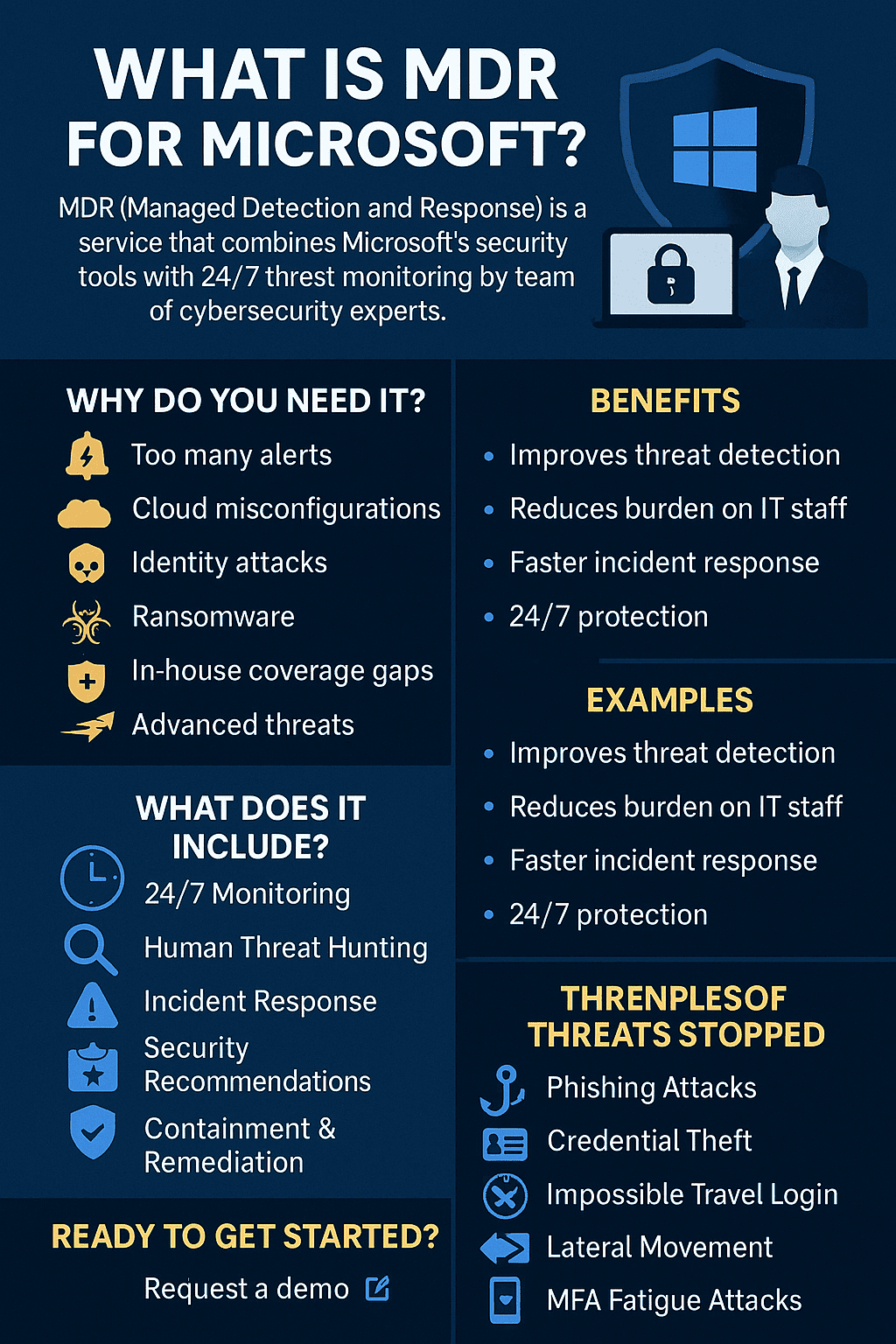
Security Technology Investments
Technology forms the foundation of modern cybersecurity programs.
Common security tools include:
-
Endpoint detection and response (EDR)
-
Firewalls
-
Network monitoring systems
-
Security information and event management (SIEM) platforms
Organizations must allocate funds for purchasing and maintaining these tools.
Security Personnel and Training
Technology alone cannot protect organizations from cyber threats.
Security teams play a critical role in monitoring systems and responding to incidents.
Hiring Cybersecurity Professionals
Organizations may require roles such as:
-
Security analysts
-
Incident responders
-
Security engineers
-
Compliance specialists
Employee Security Awareness Training
Employees must understand how to recognize cyber threats.
Training programs help reduce human-related security risks.
Incident Response and Recovery
Even the most secure organizations may experience security incidents.
Budget planning should include resources for:
-
Incident response teams
-
Backup and recovery systems
-
Disaster recovery solutions
Preparing for incidents helps minimize damage and downtime.
Compliance and Auditing
Regulatory compliance often requires periodic audits and security assessments.
Organizations must allocate resources for:
-
Compliance management
-
Security audits
-
Risk assessments
These activities ensure adherence to industry regulations.
Steps to Build an Effective Cybersecurity Budget
Organizations should follow a structured approach when performing cybersecurity budget planning.
Step 1: Conduct a Risk Assessment
Risk assessments identify vulnerabilities and potential threats.
Security teams analyze:
-
System weaknesses
-
Threat likelihood
-
Potential business impact
This information helps prioritize budget allocations.
Step 2: Identify Critical Assets
Not all systems require the same level of protection.
Organizations must identify critical assets such as:
-
Customer databases
-
Financial systems
-
Cloud infrastructure
-
Intellectual property
Protecting these assets should be a top priority.
Step 3: Prioritize Security Investments
Budget decisions should focus on reducing the most significant risks first.
Common priorities include:
-
Endpoint protection
-
Identity security
-
Network monitoring
-
Cloud security tools
Step 4: Allocate Budget for Ongoing Monitoring
Cybersecurity is not a one-time investment.
Organizations must continuously monitor systems and update security tools.
Ongoing monitoring ensures threats are detected early.
Best Practices for Cybersecurity Budget Planning
Organizations can improve their security spending efficiency by following proven strategies.
Align Security with Business Goals
Cybersecurity investments should support broader business objectives.
For example:
-
Protecting customer data
-
Maintaining regulatory compliance
-
Ensuring operational continuity
Adopt a Risk-Based Approach
Budget decisions should prioritize the most critical risks.
A risk-based approach helps maximize the effectiveness of security spending.
Invest in Automation
Security automation tools reduce manual workloads and improve detection speed.
Automation can also lower long-term operational costs.
Plan for Scalability
Organizations must ensure that security investments scale as the business grows.
Cloud-based security solutions often provide flexible scalability.
Common Cybersecurity Budget Mistakes
Even well-funded organizations sometimes mismanage cybersecurity budgets.
Underestimating Cyber Risks
Some organizations allocate minimal resources to security until a major incident occurs.
Overinvesting in Technology Without Strategy
Buying multiple security tools without proper integration may create inefficiencies.
Ignoring Employee Training
Human error remains one of the leading causes of security breaches.
Training programs must be included in cybersecurity budgets.
Failing to Update Security Tools
Outdated software can create vulnerabilities that attackers exploit.
Emerging Trends in Cybersecurity Spending
Cybersecurity budgets continue to evolve as technology and threats change.
Zero Trust Security Investments
Many organizations are adopting Zero Trust frameworks that require continuous authentication and monitoring.
Cloud Security Platforms
Cloud adoption is increasing demand for cloud-native security tools.
AI-Driven Security Tools
Artificial intelligence helps analyze security events and detect threats faster.
How Businesses Can Optimize Cybersecurity Spending
Organizations can maximize their security investments by following these strategies.
-
Conduct regular security assessments
-
Focus on protecting critical assets
-
Implement security automation
-
Invest in employee training
-
Monitor systems continuously
Effective cybersecurity budget planning ensures that organizations allocate resources efficiently and strengthen their defenses.
FAQ: Cybersecurity Budget Planning
What is cybersecurity budget planning?
Cybersecurity budget planning involves allocating financial resources to protect systems, networks, and data from cyber threats.
How much should companies spend on cybersecurity?
The appropriate budget depends on factors such as company size, industry risks, and regulatory requirements.
What are the key areas of cybersecurity spending?
Major investment areas include security technologies, personnel, training programs, and incident response capabilities.
Why is risk assessment important for cybersecurity budgeting?
Risk assessments help organizations identify vulnerabilities and prioritize security investments.
How often should cybersecurity budgets be reviewed?
Organizations should review cybersecurity budgets annually or whenever major changes occur in the threat landscape.
Final Thoughts
Cybersecurity is no longer just an IT concern—it is a business-critical priority. Organizations must proactively defend their digital infrastructure against evolving cyber threats. Without strategic planning, security investments may fail to address the most critical risks.
Effective cybersecurity budget planning enables organizations to allocate resources wisely, strengthen security defenses, and reduce the likelihood of costly data breaches.
By aligning cybersecurity investments with business objectives and risk priorities, organizations can build resilient security programs that support long-term growth.
👉 Request a demo today to see how Xcitium can help strengthen your cybersecurity strategy:
https://www.xcitium.com/request-demo/