What Is CNAPP and How Does It Work?
Updated on March 3, 2026, by Xcitium
Cloud adoption is accelerating at a record pace. Yet, according to industry research, misconfigurations and identity-related issues remain the top causes of cloud breaches. If organizations are investing heavily in cloud security tools, why do gaps still exist?
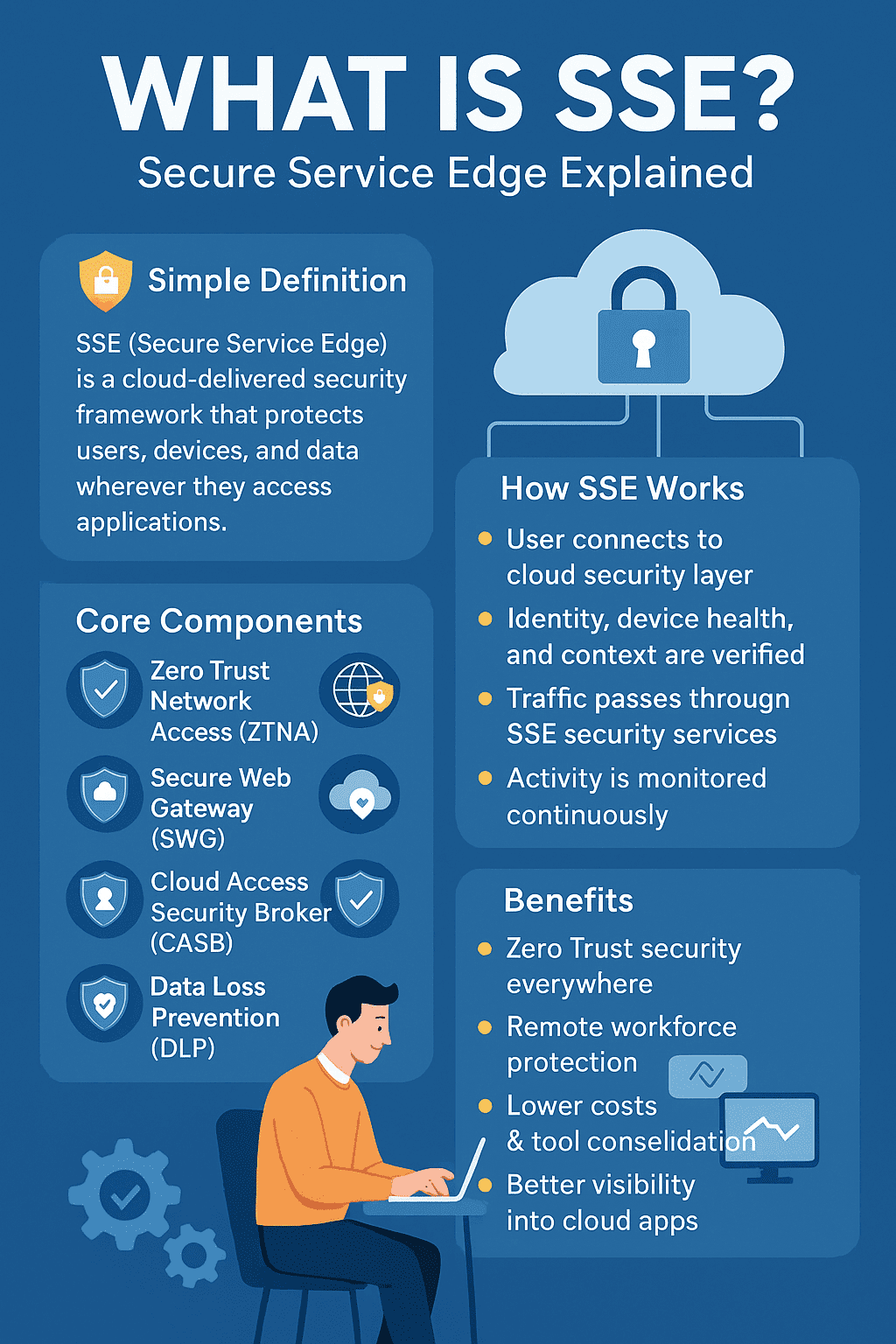
The answer often lies in fragmented security. Many businesses use separate tools for workload protection, posture management, compliance, and identity governance — creating blind spots attackers exploit.
This is where CNAPP (Cloud-Native Application Protection Platform) changes the game.
In this guide, you’ll learn what CNAPP is, how it works, why it matters, and how it strengthens cloud-native security across hybrid and multi-cloud environments.
What is CNAPP and How Does It Work?
A Cloud-Native Application Protection Platform (CNAPP) is a unified cloud security solution designed to protect cloud-native applications across their entire lifecycle — from development to production.
Instead of relying on disconnected tools, CNAPP integrates multiple security capabilities into a single platform, including:
-
Cloud Security Posture Management (CSPM)
-
Cloud Workload Protection Platform (CWPP)
-
Infrastructure as Code (IaC) security
-
Container and Kubernetes security
-
Identity and access management insights
-
Runtime protection
-
Compliance monitoring
In simple terms, CNAPP provides end-to-end visibility and protection for everything running in your cloud.
Why CNAPP Is Important for Modern Cloud Security
Cloud environments are dynamic. Containers spin up and down in seconds. Developers deploy updates multiple times a day. Traditional security tools struggle to keep up.
Key Cloud Security Challenges CNAPP Solves
-
Misconfigured storage buckets
-
Over-permissioned IAM roles
-
Vulnerable container images
-
Shadow IT workloads
-
Infrastructure drift
-
Compliance gaps
CNAPP consolidates security controls to reduce complexity and eliminate blind spots.
How Does CNAPP Work?
CNAPP works by combining posture management, workload protection, identity analytics, and runtime monitoring into a unified security framework.
Let’s break down how it functions.
Core Components of CNAPP
To understand how CNAPP works, you must first understand its foundational components.
Cloud Security Posture Management (CSPM)
CSPM continuously scans cloud configurations to detect misconfigurations and compliance violations.
What CSPM Identifies
-
Publicly exposed storage
-
Weak encryption policies
-
Open security groups (0.0.0.0/0 access)
-
Disabled logging
-
Non-compliant resources
CSPM helps enforce best practices and regulatory standards such as:
-
SOC 2
-
ISO 27001
-
HIPAA
-
PCI-DSS
Cloud Workload Protection Platform (CWPP)
CWPP secures workloads such as:
-
Virtual machines
-
Containers
-
Serverless functions
-
Kubernetes clusters
How CWPP Protects Workloads
-
Vulnerability scanning
-
Runtime threat detection
-
Malware detection
-
Behavioral monitoring
CWPP ensures that even if a misconfiguration slips through, workloads remain protected.
Infrastructure as Code (IaC) Security
Modern cloud deployments use tools like Terraform and CloudFormation.
CNAPP scans IaC templates before deployment to identify:
-
Open ports
-
Hardcoded secrets
-
Weak IAM policies
-
Non-compliant configurations
This “shift-left” security approach prevents risks before they reach production.
Kubernetes and Container Security
Containers introduce speed and agility — but also complexity.
CNAPP secures containerized environments by:
-
Scanning images for vulnerabilities
-
Enforcing Kubernetes policies
-
Monitoring runtime behavior
-
Detecting privilege escalation attempts
Cloud Infrastructure Entitlement Management (CIEM)
Identity mismanagement is a leading cause of cloud breaches.
CIEM analyzes:
-
Over-permissioned users
-
Excessive service account privileges
-
Unused permissions
-
Risky identity relationships
By enforcing least privilege, CNAPP reduces lateral movement opportunities for attackers.
The CNAPP Workflow: Step-by-Step
Here’s how CNAPP typically operates within an organization.
1. Continuous Discovery
CNAPP automatically discovers:
-
Cloud assets
-
Workloads
-
APIs
-
Identities
-
Network configurations
This creates a real-time inventory of your cloud environment.
2. Risk Assessment and Prioritization
Instead of overwhelming security teams with alerts, CNAPP correlates risks.
For example:
-
A public S3 bucket + sensitive data + over-permissioned role = high risk.
Context-based prioritization helps teams fix what matters most.
3. Threat Detection and Runtime Monitoring
CNAPP monitors workloads in real time for:
-
Suspicious processes
-
Unauthorized access
-
Crypto-mining activity
-
Exploitation attempts
Behavioral analytics reduce false positives while increasing detection accuracy.
4. Remediation and Automation
Many CNAPP solutions provide:
-
Automated remediation
-
Guided fix recommendations
-
Policy enforcement
-
Integration with DevOps pipelines
Automation reduces mean time to remediate (MTTR).
Benefits of CNAPP
Organizations adopting CNAPP experience measurable improvements in security posture.
Unified Visibility
One dashboard replaces multiple tools.
Reduced Alert Fatigue
Context-aware risk prioritization limits noise.
Improved Compliance
Continuous compliance monitoring simplifies audits.
Faster DevSecOps Integration
Security integrates seamlessly into CI/CD workflows.
Stronger Runtime Protection
Workloads stay protected even after deployment.
CNAPP vs Traditional Cloud Security Tools
| Traditional Approach | CNAPP Approach |
|---|---|
| Multiple point tools | Unified platform |
| Limited context | Correlated risk insights |
| Reactive detection | Proactive + runtime protection |
| Siloed teams | Integrated DevSecOps workflows |
CNAPP eliminates silos and strengthens cloud-native security architecture.
Who Needs CNAPP?
CNAPP is essential for:
-
Enterprises operating multi-cloud environments
-
Organizations using Kubernetes
-
Companies deploying Infrastructure as Code
-
Regulated industries requiring compliance
-
DevOps-driven businesses
If your cloud footprint is growing, CNAPP is no longer optional — it’s foundational.
Best Practices for Implementing CNAPP
Start with Asset Inventory
Understand what you have before applying controls.
Integrate with CI/CD
Embed security into development pipelines.
Enforce Least Privilege
Use CIEM insights to reduce over-permissioning.
Automate Remediation
Enable auto-fixes for common misconfigurations.
Continuously Monitor Runtime
Prevention alone is not enough. Runtime visibility is critical.
Common Misconceptions About CNAPP
“CNAPP Is Just CSPM Rebranded”
False. CNAPP integrates CSPM, CWPP, CIEM, IaC scanning, and runtime protection into one platform.
“It’s Only for Large Enterprises”
Cloud-native startups face the same risks. CNAPP scales for businesses of all sizes.
“More Tools Mean Better Security”
Fragmented tools increase complexity and blind spots. Consolidation improves effectiveness.
The Future of Cloud Security: Why CNAPP Is the Standard
As cloud environments become more complex, security must evolve.
CNAPP represents the next phase of cloud security by:
-
Breaking down silos
-
Providing context-aware risk analysis
-
Aligning security with DevOps
-
Offering end-to-end protection
Industry analysts increasingly recognize CNAPP as the future of cloud-native application protection.
Frequently Asked Questions (FAQ)
1. What does CNAPP stand for?
CNAPP stands for Cloud-Native Application Protection Platform. It combines multiple cloud security capabilities into a unified solution.
2. How is CNAPP different from CSPM?
CSPM focuses on configuration security. CNAPP includes CSPM but also adds workload protection, identity security, IaC scanning, and runtime threat detection.
3. Does CNAPP replace CWPP?
Yes, CNAPP includes CWPP functionality as part of its integrated platform.
4. Is CNAPP suitable for multi-cloud environments?
Absolutely. CNAPP is designed to provide visibility and protection across AWS, Azure, GCP, and hybrid infrastructures.
5. Can CNAPP improve compliance readiness?
Yes. Continuous compliance monitoring helps organizations align with standards like SOC 2, HIPAA, and ISO 27001.
Final Thoughts: Strengthen Your Cloud Security Strategy Today
Cloud environments are not static. They evolve daily. Without unified visibility and proactive protection, vulnerabilities accumulate silently until a breach occurs.
CNAPP delivers comprehensive cloud-native security by integrating posture management, workload protection, identity governance, and runtime defense into one intelligent platform.
If you’re ready to eliminate blind spots, simplify security operations, and protect your cloud infrastructure from modern threats, now is the time to act.
👉 Request a personalized demo today:
https://www.xcitium.com/request-demo/
Secure your cloud. Simplify protection. Stay ahead of threats.