Indicators of Attack (IOA) Explained
Updated on March 19, 2026, by Xcitium
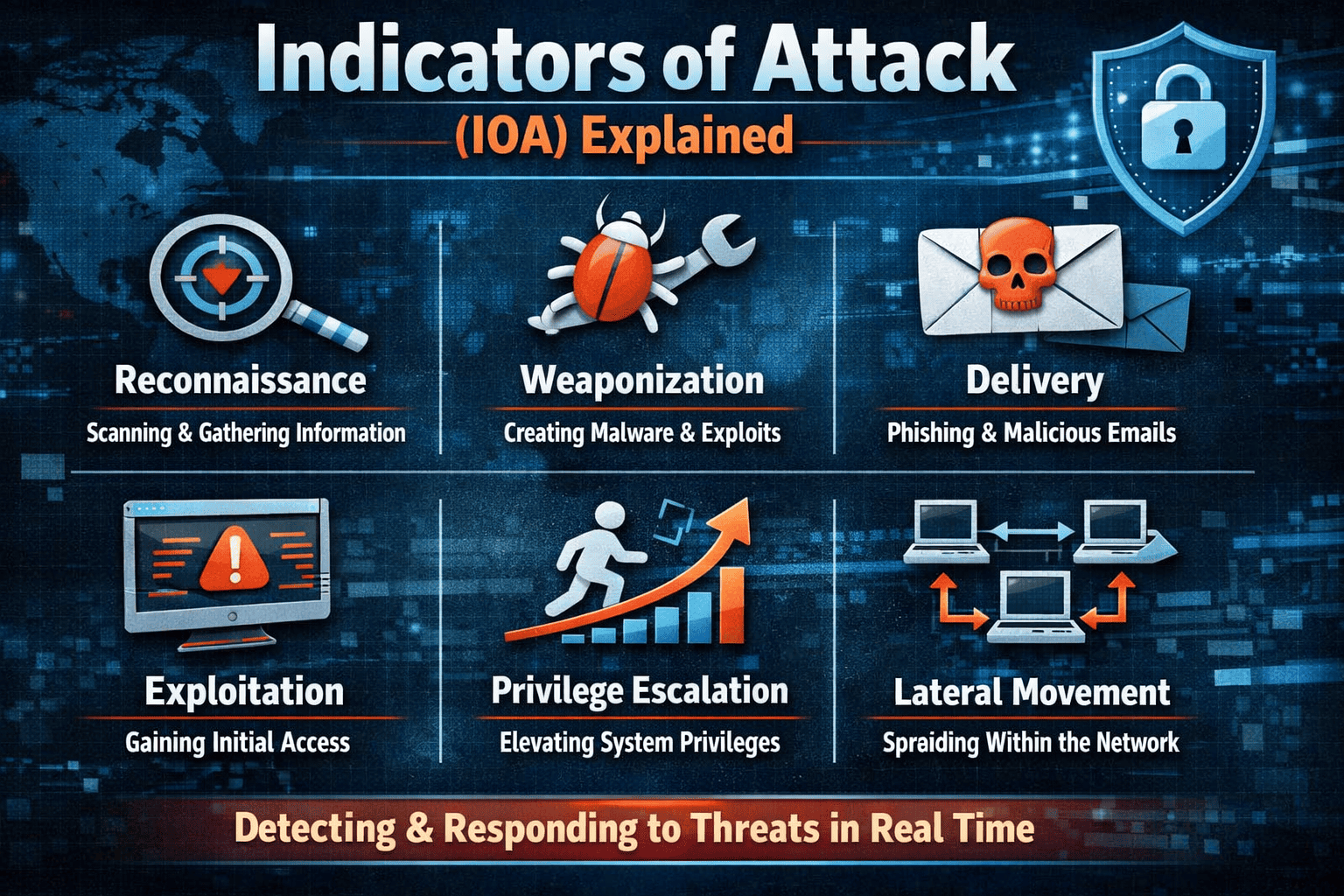
What if you could stop a cyberattack before it fully executes—instead of reacting after the damage is done? That’s exactly the advantage of using Indicators of Attack (IOA) in modern cybersecurity.
Traditional security methods often rely on known signatures or past attack data. However, attackers constantly evolve their techniques. This is where Indicators of Attack (IOA) become essential. IOAs focus on behavior and intent, helping organizations detect suspicious activity in real time—even if the threat is new.
For IT managers, cybersecurity professionals, and business leaders, understanding Indicators of Attack (IOA) is critical for building proactive defense strategies. In this guide, we’ll break down what IOAs are, how they work, how they differ from IOCs, and how organizations can use them to strengthen cybersecurity.
What Are Indicators of Attack (IOA)?
Indicators of Attack (IOA) are behavioral signs that suggest an attacker is actively attempting to compromise a system. Instead of identifying known malware, IOAs detect patterns of malicious activity.
Key Concept Behind IOA
IOAs focus on what an attacker is doing, not just what tools they are using.
This means security systems can detect:
-
Suspicious command execution
-
Unauthorized privilege escalation
-
Lateral movement within networks
-
Data exfiltration attempts
IOAs are particularly effective against zero-day attacks and unknown threats.
Why IOA-Based Detection Is Important
Cyber threats are becoming more advanced and harder to detect using traditional methods.
Limitations of Traditional Detection
Traditional systems rely on:
-
Signature-based detection
-
Known malware patterns
-
Historical threat data
These methods often fail to detect new or modified threats.
Advantages of Indicators of Attack
Using Indicators of Attack (IOA) provides several benefits:
-
Detects unknown threats
-
Identifies attacker behavior early
-
Reduces reliance on signatures
-
Improves real-time response
-
Enhances threat visibility
IOAs allow organizations to shift from reactive to proactive security.
IOA vs IOC: What’s the Difference?
Many people confuse IOAs with Indicators of Compromise (IOCs), but they serve different purposes.
Indicators of Compromise (IOC)
IOCs identify evidence that a system has already been compromised.
Examples of IOCs
-
Malicious file hashes
-
Known IP addresses
-
Suspicious domain names
-
Malware signatures
IOCs are reactive—they detect threats after infection.
Indicators of Attack (IOA)
IOAs focus on detecting attacker behavior during an attack.
Examples of IOAs
-
Abnormal login patterns
-
Unusual process execution
-
Unauthorized system access
-
Suspicious file activity
IOAs are proactive—they detect threats during execution.
Key Difference Summary
| Feature | IOA | IOC |
|---|---|---|
| Focus | Behavior | Evidence |
| Detection Timing | During attack | After compromise |
| Approach | Proactive | Reactive |
| Threat Type | Unknown & known | Mostly known |
How Indicators of Attack Work
IOA-based detection systems analyze system activity to identify suspicious behavior.
Step 1: Data Collection
Security tools collect data from:
-
Endpoints
-
Networks
-
Applications
-
User activity
Step 2: Behavior Analysis
The system analyzes behavior patterns to identify anomalies.
Examples include:
-
Unusual command execution
-
Unexpected file access
-
Rapid privilege changes
Step 3: Risk Evaluation
Each activity is assigned a risk level based on its severity.
Step 4: Alert or Response
If suspicious behavior is detected, the system may:
-
Generate alerts
-
Block activity
-
Isolate affected systems
Common Examples of Indicators of Attack
Understanding real-world IOA examples helps organizations recognize threats early.
Suspicious PowerShell Activity
Attackers often use PowerShell to execute malicious scripts.
Unusual PowerShell commands may indicate:
-
Malware execution
-
Data exfiltration
-
System manipulation
Privilege Escalation Attempts
If a user suddenly gains higher privileges, it may indicate an attack.
Lateral Movement
Attackers often move across systems after gaining initial access.
Signs include:
-
Accessing multiple systems quickly
-
Using shared credentials
-
Unusual login patterns
Data Exfiltration Behavior
Large or unusual data transfers may indicate data theft.
Tools That Use IOA-Based Detection
Several cybersecurity tools rely on IOA-based detection.
Endpoint Detection and Response (EDR)
EDR solutions monitor endpoint behavior and detect suspicious activity.
They provide:
-
Real-time monitoring
-
Threat detection
-
Incident response
Extended Detection and Response (XDR)
XDR expands detection across multiple environments.
It integrates data from:
-
Endpoints
-
Networks
-
Cloud systems
SIEM Platforms
Security Information and Event Management (SIEM) systems analyze logs and events.
They help detect patterns that match IOAs.
Best Practices for Implementing IOA Detection
Organizations should follow best practices to maximize the effectiveness of IOA-based security.
1. Deploy Advanced Endpoint Security
Use EDR or XDR solutions to monitor system behavior continuously.
2. Integrate Threat Intelligence
Combine IOA detection with threat intelligence to improve accuracy.
3. Monitor User Behavior
Track user activity to identify unusual patterns.
4. Automate Threat Response
Automated systems can respond quickly to detected threats.
5. Train Security Teams
Ensure teams understand how to interpret IOA alerts.
Challenges of IOA-Based Detection
While powerful, IOA detection comes with challenges.
False Positives
Some legitimate activities may appear suspicious.
Complexity
Behavioral analysis requires advanced tools and expertise.
Resource Requirements
Monitoring large environments can require significant resources.
The Future of IOA in Cybersecurity
As cyber threats evolve, IOA-based detection will become more important.
Future trends include:
-
AI-driven behavioral analysis
-
Automated threat hunting
-
Integration with zero trust security
-
Real-time adaptive security systems
These advancements will make cybersecurity more proactive and effective.
Frequently Asked Questions (FAQ)
What are Indicators of Attack (IOA)?
IOAs are behavioral signs that indicate a cyberattack is in progress, helping detect threats before they fully execute.
How are IOAs different from IOCs?
IOAs detect attacker behavior during an attack, while IOCs identify evidence after a system has been compromised.
Why are IOAs important?
They help detect unknown and advanced threats that traditional security methods may miss.
What tools use IOA detection?
EDR, XDR, and SIEM platforms commonly use IOA-based detection.
Can IOA detection prevent cyberattacks?
Yes. By identifying suspicious behavior early, IOA detection can stop attacks before they cause damage.
Strengthen Your Cybersecurity with IOA-Based Detection
Cyber threats are evolving rapidly, and traditional security methods are no longer enough. Indicators of Attack (IOA) provide a proactive approach to detecting and stopping threats in real time.
Organizations that adopt IOA-based detection can improve visibility, reduce risk, and respond faster to cyber incidents.
👉 Request a demo today:
https://www.xcitium.com/request-demo/
Discover how advanced threat detection solutions can help your organization stay ahead of modern cyber threats and protect critical systems.