Managed Threat Hunting
Protect your organization from advanced cyber threats with Xcitium's Managed Threat Hunting. Our dedicated team of experts proactively hunts for hidden threats within your network, using state-of-the-art tools and techniques to detect, analyze, and neutralize malicious activities. Stay ahead of attackers with continuous monitoring and expert intervention, ensuring your business remains secure and resilient.
How It Works
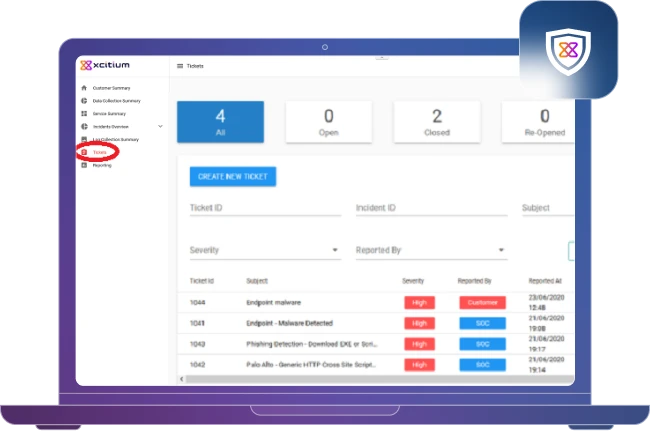
Xcitium's Managed Threat Hunting operates through a proactive and systematic approach designed to detect and neutralize advanced threats. Our process starts with continuous monitoring of your network using state-of-the-art tools to identify any signs of malicious activity. Our expert threat hunters actively seek out hidden threats that may have bypassed automated defenses, using advanced techniques and threat intelligence. Once a threat is detected, we conduct an in-depth analysis to understand its nature and potential impact, followed by implementing a targeted response plan to neutralize the threat. Post-hunt, we provide a detailed review and actionable recommendations to fortify your defenses and prevent future incidents.
Key Features

Continuous Monitoring
Our advanced monitoring tools operate around the clock, scrutinizing your network, endpoints, and cloud environments for any signs of suspicious activity. This 24/7 vigilance ensures that potential threats are detected the moment they arise.

Proactive Threat Hunting
We go beyond traditional security measures by actively seeking out hidden threats within your environment. Our experts use cutting-edge techniques and intelligence to identify and isolate threats that may have evaded automated defenses.

In-Depth Threat Analysis
Once a threat is detected, our team conducts a thorough analysis to understand its nature and impact. We leverage comprehensive threat intelligence and forensic data to develop a precise response strategy.
Targeted Threat Neutralization
We implement a tailored response plan to effectively neutralize the identified threat. Our approach minimizes disruption and ensures that your operations remain secure and uninterrupted.

Post-Hunt Review
After neutralizing the threat, we perform a detailed review to assess the incident and identify any vulnerabilities. We provide actionable recommendations to strengthen your defenses and prevent future threats.

Post-Hunt Review
We work with you to implement recommended security measures, ensuring continuous improvement and resilience against evolving threats. Our ongoing support helps you stay ahead in the ever-changing cyber threat landscape.
Benefits
Threat Detection
Analysis & Response
Improvement
Vigilance
Why Choose Xcitium Managed Threat Hunting?
Choosing Xcitium Managed Threat Hunting means opting for a proactive and expert-driven approach to cybersecurity. Our team of dedicated professionals continuously monitors your environment, actively hunting for hidden threats and ensuring swift and effective response. With our advanced tools and techniques, we provide comprehensive threat analysis and targeted neutralization, minimizing disruption and safeguarding your operations. Our commitment to continuous improvement and ongoing defense enhancement means your organization is always prepared to face the evolving threat landscape.





