Have your IT administrator whitelist the following domains:
- mailsupportsystems.com
- trackingsupportservices.com
- payrollsupportadmin.com
- emessageadmin.com
- messageservicesadmin.com
These domains are registered to IP addresses: 104.37.180.1
If your organization uses spam filtering software such as the ones listed below, you can have your IT administrator customize the settings per the associated links to prevent the phishing emails from being blocked:
- Barracuda: Setup email allow list. Click here for official Barracuda documentation.
- Cisco ESA: Create whitelisting policy for phishing simulations. Click here for official Cisco documentation.
- G Suite: Create and approve sender list. Click here for official G Suite documentation.
- Microsoft 365: Configure 3rd party phishing simulations. Click here for official Microsoft documentation.
Please note: Microsoft does not recommend using transport rules for phishing simulations.
- Microsoft Defender for Office 365: Configure anti-phishing policies in EOP. Click here for official Microsoft documentation.
The phishing simulations closely resemble emails received on a regular basis. They are created to look very similar to those sent by large, well-known corporations such as Google, Amazon, Chase, etc.
New email templates are carefully created and selected for each client and phishing period. Factors such as the time of year, client type (town vs. school), and location are all taken into consideration when designing simulations.
All URLs within phishing simulation emails link to Xcitium's own training domains. Upon clicking one of these links, the victim is sent to a landing page that provides education on how they could have identified the simulated phishing attempt and how to avoid clicking on potentially malicious URLs in the future.
Phishing simulations normally run for one to two weeks, Monday through Friday.
Users that receive the simulated phishing emails will not be negatively impacted in any way.
No. Xcitium can only use an email address provided by your organization.
You can add/remove users (one at a time or in bulk) by uploading a list through the online portal at insight.d2cybersecurity.com. Please confirm there are no typos on your list before submitting to ensure all users receive the simulated phishing emails.
Answer the Administrator questions if you are responsible for: vendor management and audit, communication and press communication, defining policies/procedures/guidelines, coordinating RFPs, arranging security awareness training, assessing security risk and working with Cyber Insurance, and authority to invoke incident response and disaster recovery.
Answer the IT questions if you are responsible for: network and infrastructure management, implementing physical and technical safeguards, configuration/inventory/account management, scanning/patching/remediation, managing access to network/systems/accounts, backup and recovery of data, and incident reporting/logging/analysis/documentation.
Will my answers be audited? Depending on the kind of service prescribed: Gap Assessment Lite — answers will be reviewed by an auditor without you and a final report provided. Gap Assessment Full — answers will be audited by an auditor with both IT and Administrator POC.
Log in to your Insight portal and navigate to User Menu → Service Settings → Vulnerability Assessment
Enter the following information:
- Estimated number of active hosts
- List of all domains
- Public IP addresses and ranges (active and inactive)
- Whether you are using a dynamic IP address
Once completed, save the information. If you need assistance, please contact d2support@xcitium.com.
Please keep in mind that new vulnerabilities and exploits can be found daily, so you may see something appear on the next report.
Vulnerability Scanning and External Penetration Testing are conducted against your public IPs and domains. Please keep in mind the private IPs in the ranges listed below are not valid IPs for those services:
- Class A: 10.0.0.0 — 10.255.255.255
- Class B: 172.16.0.0 — 172.31.255.255
- Class C: 192.168.0.0 — 192.168.255.255
In general, any IP in the following ranges is a private IP used inside a network/firewall and not suitable for external scans:
- 10.0.0.0 to 10.255.255.255
- 172.16.0.0 to 172.31.255.255
- 192.168.0.0 to 192.168.255.255
- Please keep in mind there are others such as 127.0.0.1 that are special addresses that would also be unacceptable for external vulnerability scanning. See https://en.wikipedia.org/wiki/Reserved_IP_addresses
Additional IP addresses can be added at any time.
Penetration testing is a manual process that involves exploiting vulnerabilities, emulating what a hacker might attempt in an effort to access and take control of your network.
One of our goals is to identify potentially forgotten internet connected devices that might compromise the security of your network.
- Our advice is to scan every external IP address to detect any vulnerabilities. Leaving a critically important section of the network unscanned/tested might leave it vulnerable to a cyber-attack that could have otherwise been prevented.
- Xcitium will NOT conduct a vulnerability scan on any interconnected systems.
- Xcitium will NOT attempt to connect to any interconnected county, state, or federal systems.
- Only the IP addresses listed on the KYC form will be included.
Vulnerability Scanning and External Penetration Testing are conducted against your public IPs and domains. The following private IP ranges are not valid for those services:
- Class A: 10.0.0.0 — 10.255.255.255
- Class B: 172.16.0.0 — 172.31.255.255
- Class C: 192.168.0.0 — 192.168.255.255
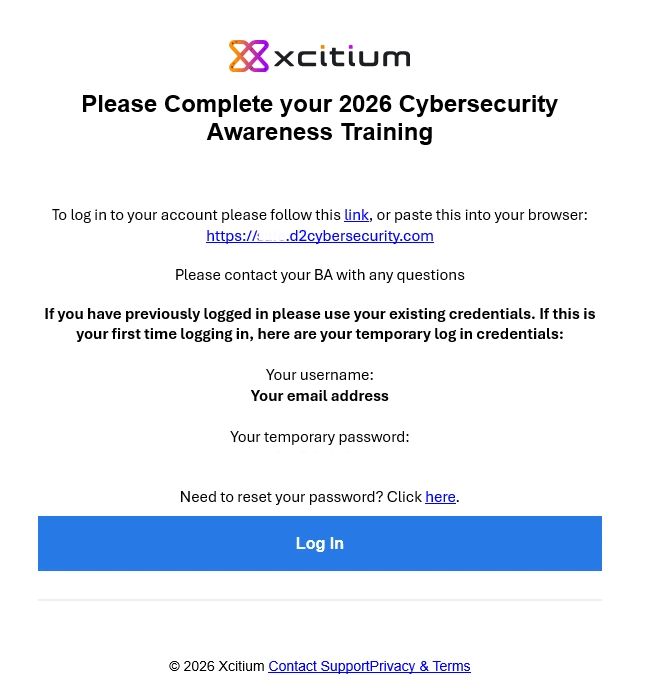
After your training course is configured, every trainee added to your organization will be automatically enrolled. They will receive a welcome email with their credential information.
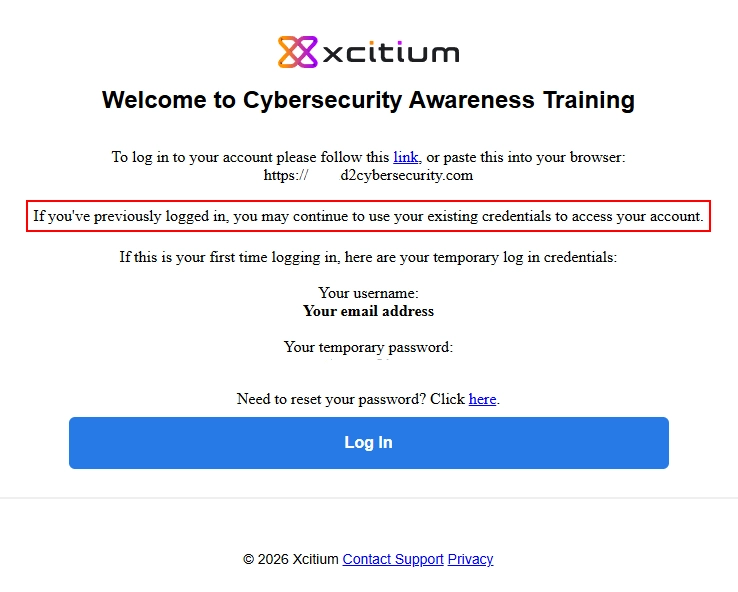
Your organization has enrolled you in Xcitium Cybersecurity's Cyber Awareness Education program, and you have not yet fully completed your courseware.
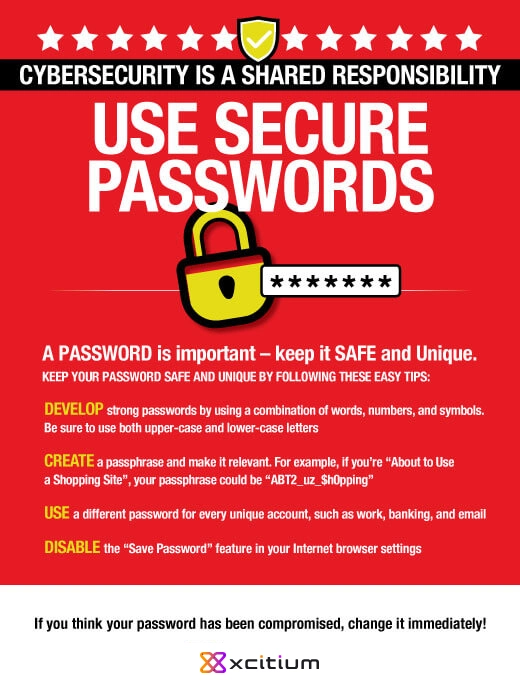
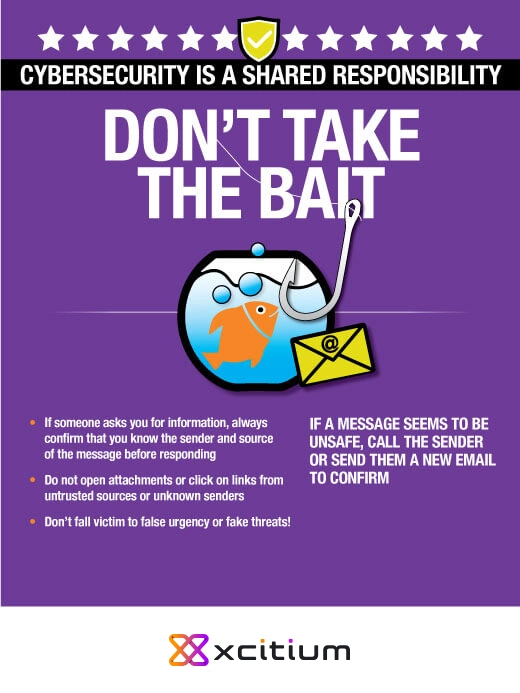
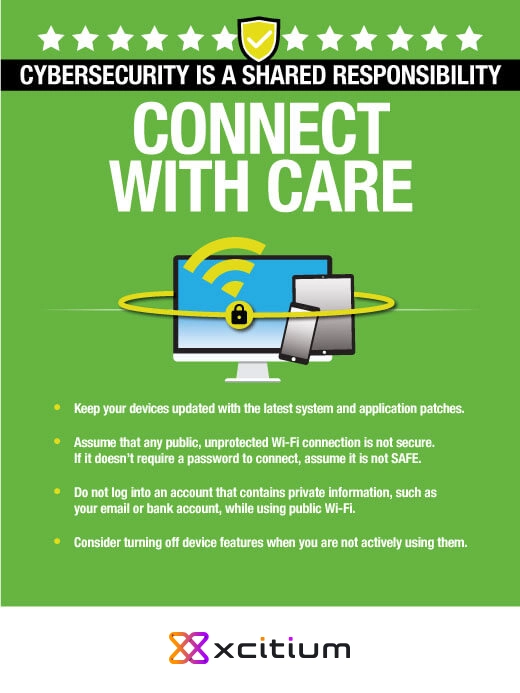
Download our collection of professionally designed cybersecurity awareness posters for use in your workspace. Each poster combines bright visuals and useful tips to keep viewers mindful of cybersecurity best practices.