What Is Ransomware And How Does It Work?
Updated on October 11, 2022, by Xcitium

In 2017, hundreds of thousands of personal computers running Microsoft Windows fell victim to malware. The malware needed the user to pay $300 in bitcoin to be able to access their files.
That malware was WannaCry, which is a type of ransomware. Estimates of the damage it caused were about $4b, according to reports.
So, What’s Ransomware?
Ransomware is simply a software made with malicious intent to deny users access to their computer systems until a certain amount of money is paid. It can be frustrating to deal with ransomware.
Over the years, ransomware has become commonplace. Analysis of hundreds of ransomware attacks shows ransomware falls into two categories.
Crypto Ransomware
The most common type of ransomware is crypto-ransomware. This type of ransomware attack happens when the malware encrypts users’ files and demands a ransom before the data will be decoded.
The files are usually encoded in a format that most applications can’t access. Jigsaw, an infamous ransomware, encrypts and deletes victims’ files every hour. It also ensures that users won’t be able to shut down as 1000 files will be deleted if they attempt to shut down.
Locker Ransomware
Locker ransomware is less common. It can also be as destructive as its crypto cousin.
This ransomware denies its victim access to their computer or a computer network. To gain access to the system, the victim will have to pay a certain amount of money.
If you’re a member of a network of computers, it’s common to also be a victim of locker ransomware.
How Ransomware Happens
There are several ways ransomware gets into your computer systems. The most common way for your computer to be infected with ransomware is from infected files on the internet. Here is a detailed look:
By Clicking Links with Malicious Content
The most common way of being a victim of a ransomware attack is to click suspicious links. Usually, what most ransomware attackers do is to send emails with links that will infect your computer.
With social networks and text messages enabling link clicking, it’s easy to click a link that can infect your computer with ransomware.
Downloading Infected Files
Another way a ransomware attack infects your device is to embed an infected file in either email or a website. When you download the file, the malware gets installed and ready to carry out its acts.
Some might not explicitly tell you to download a file. For instance, some websites might ask you to enable notifications. In guise, what the foul website does is to download malware into your computer. From there, it encrypts your files and holds your computer to a ransom.
From an Infected Network
You can also be a victim of ransomware from a network you’re connected to. For instance, a computer network might already be compromised. Connecting to that network might cause the attackers to download malicious files to your computer and compromise your system.
Some attackers also lurk around public Wi-Fi, looking for victims. If you connect to that Wi-Fi without a secure firewall or security software, you might become a ransomware victim.
How To Prevent Ransomware
The best way to prevent ransomware attacks is to avoid opening infected files, software or using public networks. Always Examine links before clicking.
There are many unpleasant websites that promise free stuff. Some might ask you to play a strange game. Most of them are malicious websites and can install dangerous files into your device. You should avoid such websites.
However, it’s difficult to entirely prevent clicking of infected links, especially if you’re a business owner with several employees. What to do? Cybersecurity can help.
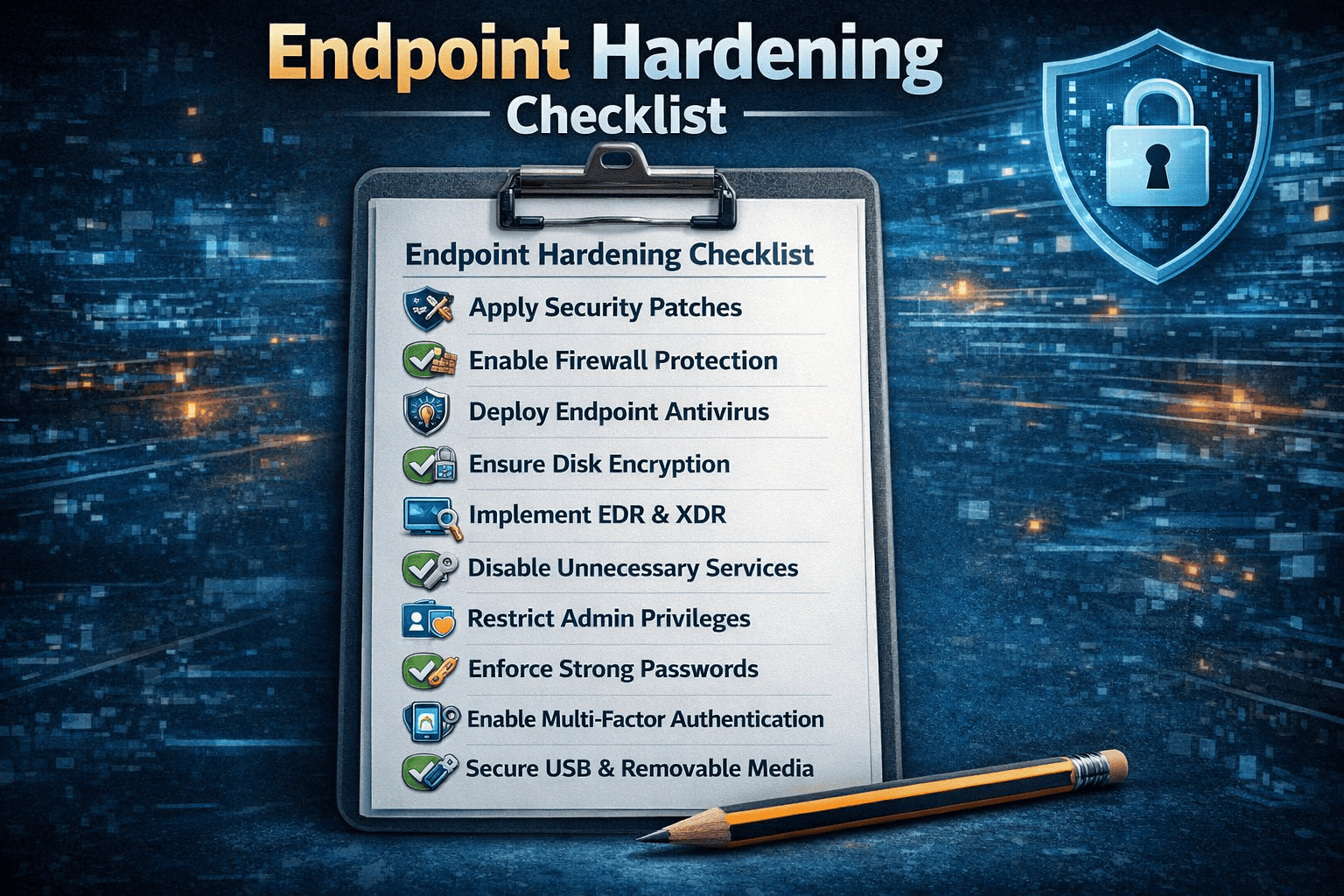
Install a Solid Antivirus
Antiviruses are generally known to protect against malware. Getting an active antivirus is, therefore, a good step in preventing malware attacks.
Update Your Operating System and Software
Make sure your operating system is updated from time to time. The WannaCry problem was solved on most computers by installing a patch from Microsoft. Essential apps like browsers and media viewers should be updated as they can be a carrier for ransomware.
Use Strong Passwords
Make your password hard to guess and unpredictable. Avoid using your date of birth or names as a password. These terms are easy to guess.
You should also change your passwords from time to time.
Use Advanced Endpoint Protection
Attackers are losing sleep to ensure they make progress—this is evident in the emergence of advanced malware that evades antivirus and other traditional security systems. You need advanced endpoint protection to protect your computer against notorious malware like ransomware.
Advanced endpoint protection is specially designed to tackle advanced threats. It uses high proactive technology like IoT, AI, and others to detect and block both files and fileless malware.