
- July 29, 2025
- 5 mins
Cybersecurity professionals often focus their efforts on external threats—malware, phishing,...
- July 29, 2025
- 5 mins
In today’s hyper-connected world, where every device—your phone, laptop, smart fridge—is...
- July 29, 2025
- 5 mins
In a digital world filled with increasing threats, simply having antivirus software isn’t...

- July 29, 2025
- 5 mins
Ever missed a package because you weren’t home? Or worried about parcels sitting unattended on...
- July 29, 2025
- 6 mins
Have you ever struggled with a slow internet connection or lost access to your Wi-Fi altogether?...
- July 29, 2025
- 5 mins
Have you forgotten your voicemail password? Need to re-record your greeting or fix voicemail...
- July 29, 2025
- 5 mins
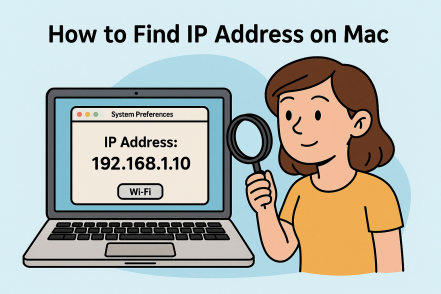
Ever wondered how to find your IP address on a Mac, whether for troubleshooting, network...
- July 29, 2025
- 5 mins
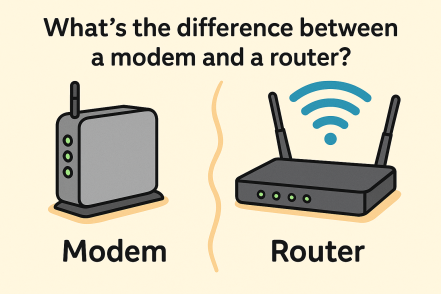
Have you ever looked at your internet setup and wondered: what’s the difference between a modem...
- July 29, 2025
- 5 mins
Have you ever accessed your emails from different devices, used Google Docs, or backed up your...








