Network Detection and Response (NDR) Guide: How It Detects and Stops Advanced Cyber Threats
Updated on March 12, 2026, by Xcitium
Cyberattacks are becoming more advanced and difficult to detect. Traditional security tools such as firewalls and antivirus solutions often fail to identify sophisticated attacks that move silently across corporate networks. This is where a Network Detection and Response (NDR) Guide becomes essential for organizations looking to strengthen their cybersecurity defenses.
A Network Detection and Response (NDR) Guide helps security teams understand how NDR technologies monitor network traffic, identify suspicious behavior, and respond to cyber threats in real time. For IT managers, cybersecurity professionals, and business leaders, implementing NDR solutions can significantly improve threat visibility and incident response capabilities.
Organizations across industries are now investing in network detection and response solutions to detect lateral movement, identify advanced persistent threats (APTs), and stop attackers before they cause major damage.
In this Network Detection and Response (NDR) Guide, we’ll explore how NDR works, its key benefits, best practices for deployment, and why it has become a critical component of modern cybersecurity architectures.
What Is Network Detection and Response (NDR)?
Network Detection and Response (NDR) is a cybersecurity technology that monitors network traffic to detect suspicious activities and potential threats.
Unlike traditional security tools that rely mainly on signature-based detection, network detection and response solutions use behavioral analytics, machine learning, and threat intelligence to identify anomalies in network activity.
Key Functions of NDR
A typical NDR system performs several important security functions:
-
Monitoring network traffic continuously
-
Detecting abnormal behaviors across networks
-
Identifying hidden threats and malicious activity
-
Investigating security incidents
-
Automating response to security threats
Because attackers often move laterally inside networks after gaining initial access, Network Detection and Response (NDR) solutions are critical for detecting these stealthy movements.
Why Organizations Need Network Detection and Response
Modern enterprise networks are complex and distributed. Employees connect from multiple devices, applications run in the cloud, and sensitive data flows across various systems.
Traditional security tools struggle to keep up with this complexity.
A Network Detection and Response (NDR) Guide helps organizations understand why NDR technologies have become essential.
Growing Sophistication of Cyber Threats
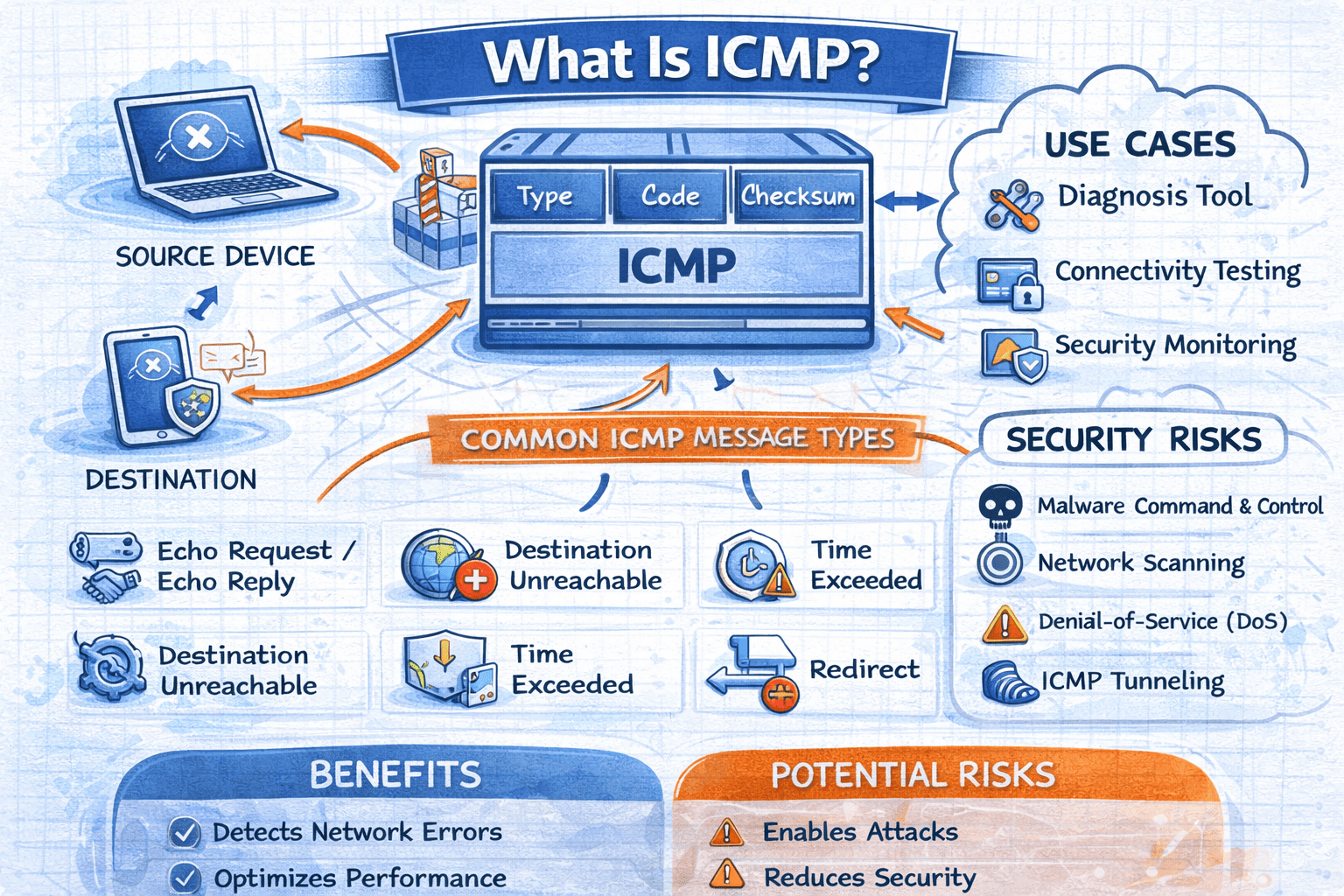
Attackers use advanced techniques such as:
-
Fileless malware
-
Command-and-control communication
-
Insider threats
-
Encrypted traffic attacks
These threats often bypass conventional defenses.
Increased Network Visibility
NDR platforms provide deep visibility into network activity, helping security teams understand how data flows through their infrastructure.
Faster Threat Detection
NDR tools analyze traffic in real time, enabling faster detection of potential threats.
Improved Incident Response
By correlating network activity with threat intelligence, NDR solutions help security teams respond quickly to incidents.
How Network Detection and Response Works
To understand the value of this Network Detection and Response (NDR) Guide, it’s important to understand how NDR systems operate.
Network Traffic Monitoring
NDR solutions collect network data from multiple sources such as:
-
Network sensors
-
Switches and routers
-
Cloud environments
-
Endpoint systems
This data provides a complete view of network activity.
Behavioral Analysis
Unlike traditional detection systems, NDR platforms analyze behavioral patterns.
They detect unusual activities such as:
-
Abnormal data transfers
-
Suspicious login attempts
-
Unauthorized lateral movement
Behavior-based detection helps identify threats that traditional tools miss.
Threat Intelligence Integration
Many NDR platforms integrate with threat intelligence feeds.
These feeds provide information about:
-
Known malicious IP addresses
-
Suspicious domains
-
Emerging attack techniques
This helps security teams detect threats more effectively.
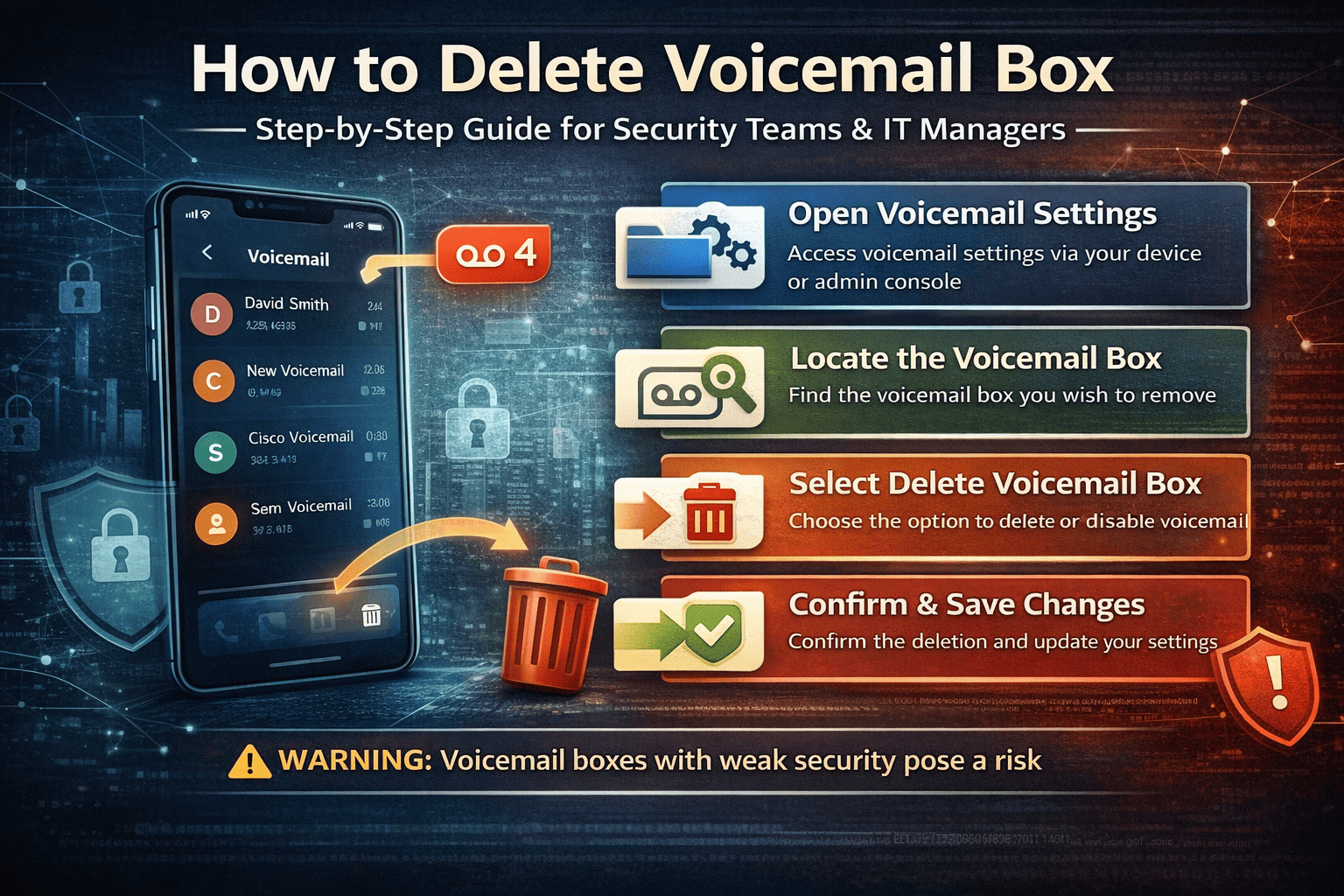
Automated Threat Response
Advanced network detection and response solutions can automatically respond to threats by:
-
Blocking suspicious network connections
-
Isolating compromised devices
-
Triggering security alerts
Automation reduces response time and minimizes damage.
Key Components of Network Detection and Response
An effective Network Detection and Response (NDR) Guide includes understanding the core components of NDR architecture.
Network Sensors
Network sensors collect traffic data from across the network.
They provide visibility into internal and external communications.
Analytics Engine
The analytics engine processes network data using:
-
Machine learning algorithms
-
Behavioral analytics
-
Threat detection models
This engine identifies anomalies that may indicate cyber threats.
Threat Intelligence Platform
Threat intelligence platforms enhance detection capabilities by providing context about known threats.
Incident Response Tools
These tools allow security teams to investigate and respond to threats detected by the NDR system.
Network Detection and Response vs Traditional Security Tools
Many organizations ask how Network Detection and Response (NDR) solutions differ from traditional cybersecurity tools.
NDR vs SIEM
SIEM platforms collect and analyze security logs from various systems.
NDR focuses specifically on network traffic analysis.
NDR vs EDR
EDR monitors endpoint devices such as laptops and servers.
NDR analyzes network traffic to detect threats moving across the network.
NDR vs IDS/IPS
Traditional intrusion detection systems rely heavily on signature-based detection.
NDR uses behavioral analysis to detect unknown threats.
Benefits of Network Detection and Response
Implementing NDR solutions provides several advantages for organizations.
Enhanced Network Visibility
Security teams gain deeper visibility into network traffic and communication patterns.
Detection of Advanced Threats
NDR tools can detect sophisticated attacks that evade traditional security systems.
Reduced Incident Response Time
Automated alerts and responses help organizations contain threats faster.
Improved Security Operations
NDR platforms integrate with other security tools to provide unified threat detection.
Best Practices for Implementing NDR
To maximize the effectiveness of Network Detection and Response (NDR) solutions, organizations should follow proven best practices.
Deploy Network Sensors Strategically
Sensors should be placed in critical network segments to capture relevant traffic.
Integrate with Existing Security Tools
NDR platforms should integrate with:
-
SIEM systems
-
Endpoint detection tools
-
Threat intelligence platforms
Use Automated Threat Detection
Automation helps identify threats quickly and reduce manual analysis.
Monitor Encrypted Traffic
Many cyberattacks use encrypted channels.
NDR systems should analyze encrypted traffic patterns to detect suspicious behavior.
Challenges of Network Detection and Response
While NDR solutions provide powerful capabilities, organizations may face challenges during deployment.
Alert Fatigue
Security teams may receive large volumes of alerts.
Proper tuning of detection rules helps reduce false positives.
Network Complexity
Large enterprise networks generate massive amounts of traffic data.
Advanced analytics are required to process this data effectively.
Integration Issues
Organizations must ensure NDR solutions integrate smoothly with existing security infrastructure.
Future Trends in Network Detection and Response
The future of NDR technology is evolving rapidly.
AI-Powered Threat Detection
Artificial intelligence will improve anomaly detection and threat analysis.
Integration with XDR Platforms
NDR solutions are increasingly integrated with Extended Detection and Response (XDR) platforms.
Cloud-Native NDR
Cloud-based NDR solutions will provide scalable monitoring for hybrid environments.
FAQ: Network Detection and Response (NDR)
What is Network Detection and Response?
Network Detection and Response (NDR) is a cybersecurity technology that monitors network traffic to detect suspicious behavior and respond to threats.
How does NDR improve cybersecurity?
NDR provides real-time network visibility and behavioral analysis that helps detect advanced threats.
Is NDR better than traditional intrusion detection systems?
NDR uses advanced analytics and machine learning, making it more effective at detecting unknown threats.
Can NDR work with other security tools?
Yes. NDR platforms integrate with SIEM, EDR, and threat intelligence systems.
Who should use NDR solutions?
Organizations with complex networks, sensitive data, and advanced cybersecurity requirements benefit most from NDR technologies.
Final Thoughts
As cyber threats become more sophisticated, organizations must adopt advanced security technologies to protect their networks. A strong Network Detection and Response (NDR) Guide helps security teams understand how to detect hidden threats, analyze suspicious network activity, and respond to incidents quickly.
By implementing network detection and response solutions, organizations gain greater visibility into network behavior and improve their ability to detect and stop cyberattacks before they cause significant damage.
If you’re looking to strengthen your organization’s threat detection capabilities and improve network security monitoring, advanced cybersecurity platforms can help.
👉 Request a demo today to see how Xcitium can strengthen your cybersecurity defenses:
https://www.xcitium.com/request-demo/