Building a Zero Trust Strategy: A Practical Guide for Modern Cybersecurity
Updated on March 12, 2026, by Xcitium
Cyberattacks are no longer limited to external threats. Today’s attackers often gain access through compromised credentials, insider threats, or vulnerable endpoints already inside corporate networks. This shift in attack methods has forced organizations to rethink traditional perimeter-based security models.
This is where building a Zero Trust strategy becomes essential.
The Zero Trust model assumes that no user, device, or system should be trusted automatically, even if it is inside the corporate network. Every request for access must be verified continuously. For IT managers, cybersecurity professionals, and business leaders, building a Zero Trust strategy is one of the most effective ways to strengthen modern security frameworks.
According to industry studies, organizations implementing Zero Trust architectures significantly reduce the risk of data breaches and insider attacks. However, building a Zero Trust strategy requires careful planning, the right technology stack, and well-defined security policies.
In this guide, we’ll explore what Zero Trust is, why it matters, and how organizations can successfully implement a Zero Trust cybersecurity strategy step by step.
What Is Zero Trust Security?
Zero Trust is a cybersecurity framework that eliminates implicit trust in network environments. Instead of assuming that users inside a network are safe, Zero Trust requires strict identity verification and continuous monitoring.
Core Principle of Zero Trust
The fundamental principle of Zero Trust is simple:
“Never trust, always verify.”
Every access request must be authenticated and authorized before granting access to resources.
Key Components of Zero Trust Security
A successful Zero Trust architecture typically includes several critical components:
-
Identity and access management (IAM)
-
Multi-factor authentication (MFA)
-
Device security verification
-
Network segmentation
-
Continuous monitoring and analytics
Organizations building a Zero Trust strategy must integrate these elements into their security architecture.
Why Organizations Are Moving Toward Zero Trust
Traditional security models rely heavily on network perimeters such as firewalls. However, modern IT environments have changed dramatically.
Expansion of Cloud Infrastructure
Many organizations now store applications and data in the cloud rather than on internal servers.
Remote and Hybrid Workforces
Employees access company systems from home networks, mobile devices, and public Wi-Fi.
Increased Cyber Threats
Cybercriminals exploit weak authentication systems and stolen credentials.
Insider Threat Risks
Employees and contractors with excessive privileges can accidentally or intentionally expose sensitive information.
Because of these challenges, building a Zero Trust strategy has become a top priority for many organizations.
Key Principles for Building a Zero Trust Strategy
Organizations must follow several guiding principles when implementing Zero Trust security.
Verify Identity Continuously
Every user attempting to access a system must prove their identity.
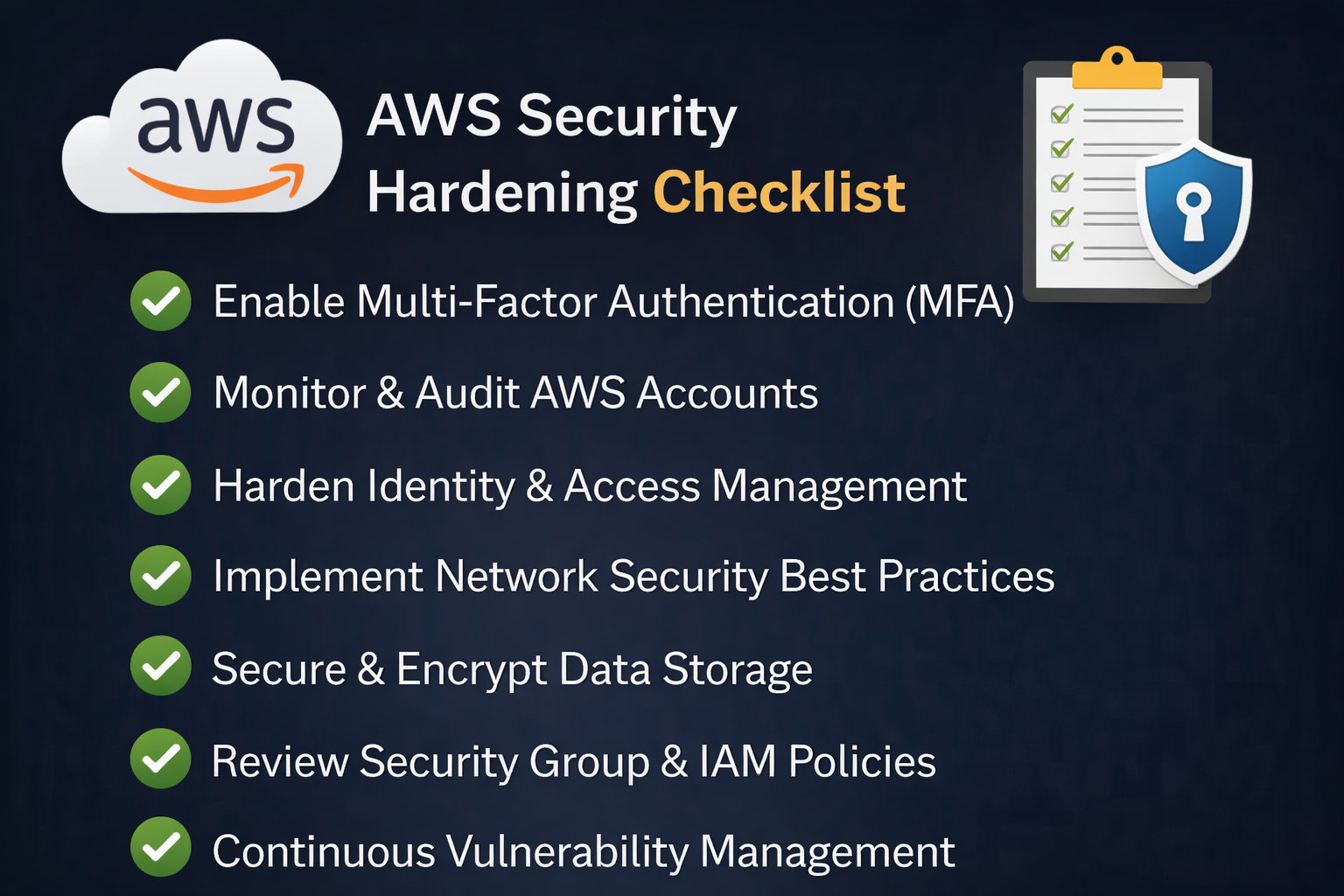
Implement Multi-Factor Authentication
Multi-factor authentication ensures that users verify their identity using more than one method.
Examples include:
-
Passwords
-
One-time codes
-
Biometric authentication
Use Identity and Access Management
IAM systems help organizations manage user identities and access privileges efficiently.
Apply the Principle of Least Privilege
Users should only receive access to the systems and data necessary for their roles.
Role-Based Access Control
Role-based access control (RBAC) assigns permissions based on job roles.
Temporary Access Permissions
Temporary privileges reduce long-term exposure to security risks.
By limiting access, organizations reduce the damage attackers can cause if accounts are compromised.
Secure All Devices and Endpoints
Endpoints are one of the most common entry points for attackers.
Device Verification
Before granting access, organizations should verify whether devices meet security requirements.
Endpoint Protection Tools
Security solutions such as endpoint detection and response (EDR) help detect suspicious activity.
Mobile Device Security
Mobile devices accessing corporate networks must follow strict security policies.
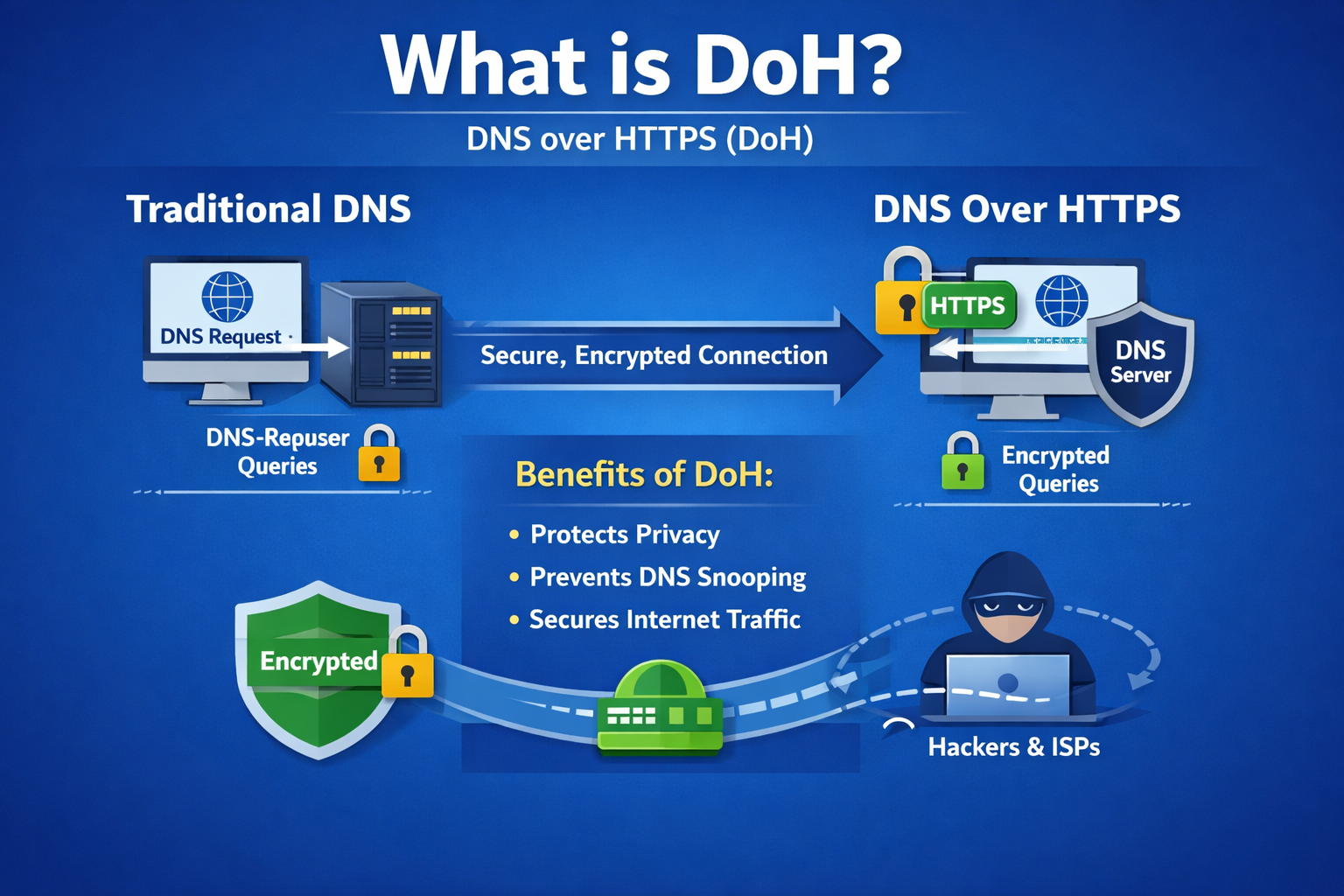
Implement Network Segmentation
Network segmentation divides networks into smaller isolated segments.
Benefits of Network Segmentation
Segmentation prevents attackers from moving laterally within networks.
Even if attackers compromise one system, segmentation limits their ability to access other resources.
Micro-Segmentation
Micro-segmentation provides even more granular control over network traffic.
Monitor and Analyze Network Activity
Continuous monitoring is essential when building a Zero Trust strategy.
Security Monitoring Tools
Organizations use tools such as:
-
SIEM (Security Information and Event Management)
-
Network detection and response (NDR)
-
Endpoint monitoring platforms
These tools analyze network activity and detect anomalies.
Behavioral Analytics
Behavioral analysis helps detect suspicious user behavior, even if login credentials appear legitimate.
Steps for Building a Zero Trust Strategy
Implementing Zero Trust requires a structured approach.
Step 1: Identify Critical Assets
Organizations must first identify the most sensitive systems and data.
Examples include:
-
Customer databases
-
Financial records
-
Intellectual property
-
Cloud applications
These assets should receive the highest level of protection.
Step 2: Map Network Architecture
Understanding how data flows through the organization helps security teams identify vulnerabilities.
Network mapping includes:
-
Devices
-
Servers
-
Applications
-
Cloud services
Step 3: Strengthen Identity Security
Identity security forms the foundation of Zero Trust.
Organizations should:
-
Enforce strong authentication policies
-
Implement multi-factor authentication
-
Monitor login activity
Step 4: Deploy Endpoint Security
Endpoints must be monitored continuously.
Security tools should detect:
-
Malware infections
-
Unauthorized access attempts
-
Suspicious device activity
Step 5: Enforce Continuous Monitoring
Continuous monitoring ensures that security teams detect threats early.
Automated alerts help security teams respond quickly.
Challenges When Implementing Zero Trust
While Zero Trust offers strong security benefits, organizations may face challenges during implementation.
Legacy Systems
Older systems may not support modern authentication methods.
Complexity of Integration
Integrating multiple security tools can be complex.
Employee Resistance
Users may resist new authentication procedures.
Budget Constraints
Deploying new security technologies requires investment.
Organizations must address these challenges to successfully implement Zero Trust.
Best Practices for Zero Trust Implementation
Organizations can improve their success rate by following proven strategies.
Start with High-Risk Areas
Begin implementation with critical systems and expand gradually.
Automate Security Processes
Automation helps reduce manual workloads and improve efficiency.
Educate Employees
Employees should understand why Zero Trust policies are necessary.
Continuously Improve Security Policies
Zero Trust strategies must evolve as cyber threats change.
The Future of Zero Trust Security
Zero Trust is rapidly becoming the standard cybersecurity model.
Emerging technologies are making Zero Trust more effective.
AI-Powered Security Monitoring
Artificial intelligence can detect threats faster by analyzing large datasets.
Integration with Cloud Security
Zero Trust frameworks are increasingly integrated with cloud platforms.
Automated Threat Response
Automation helps organizations respond to threats without manual intervention.
FAQ: Building a Zero Trust Strategy
What is a Zero Trust strategy?
A Zero Trust strategy is a cybersecurity approach that requires strict verification for every user and device attempting to access network resources.
Why is Zero Trust important?
Zero Trust helps prevent unauthorized access, protect sensitive data, and reduce the risk of cyberattacks.
What technologies support Zero Trust?
Technologies include identity management systems, multi-factor authentication, endpoint security tools, and network monitoring platforms.
Can small businesses implement Zero Trust?
Yes. Small organizations can implement Zero Trust gradually by focusing on identity verification and endpoint security.
Is Zero Trust suitable for cloud environments?
Yes. Zero Trust is particularly effective in cloud and hybrid IT environments where traditional network perimeters are less effective.
Final Thoughts
Cyber threats continue to evolve, making traditional perimeter-based security models increasingly ineffective. Organizations must adopt modern security frameworks that protect systems, users, and data regardless of location.
By building a Zero Trust strategy, businesses can reduce the risk of unauthorized access, detect threats earlier, and strengthen their overall cybersecurity posture.
A successful Zero Trust implementation combines strong identity verification, endpoint protection, network segmentation, and continuous monitoring.
Organizations that adopt this proactive approach will be better prepared to defend against modern cyber threats.
👉 Request a demo today to see how Xcitium can help strengthen your cybersecurity with advanced security solutions:
https://www.xcitium.com/request-demo/