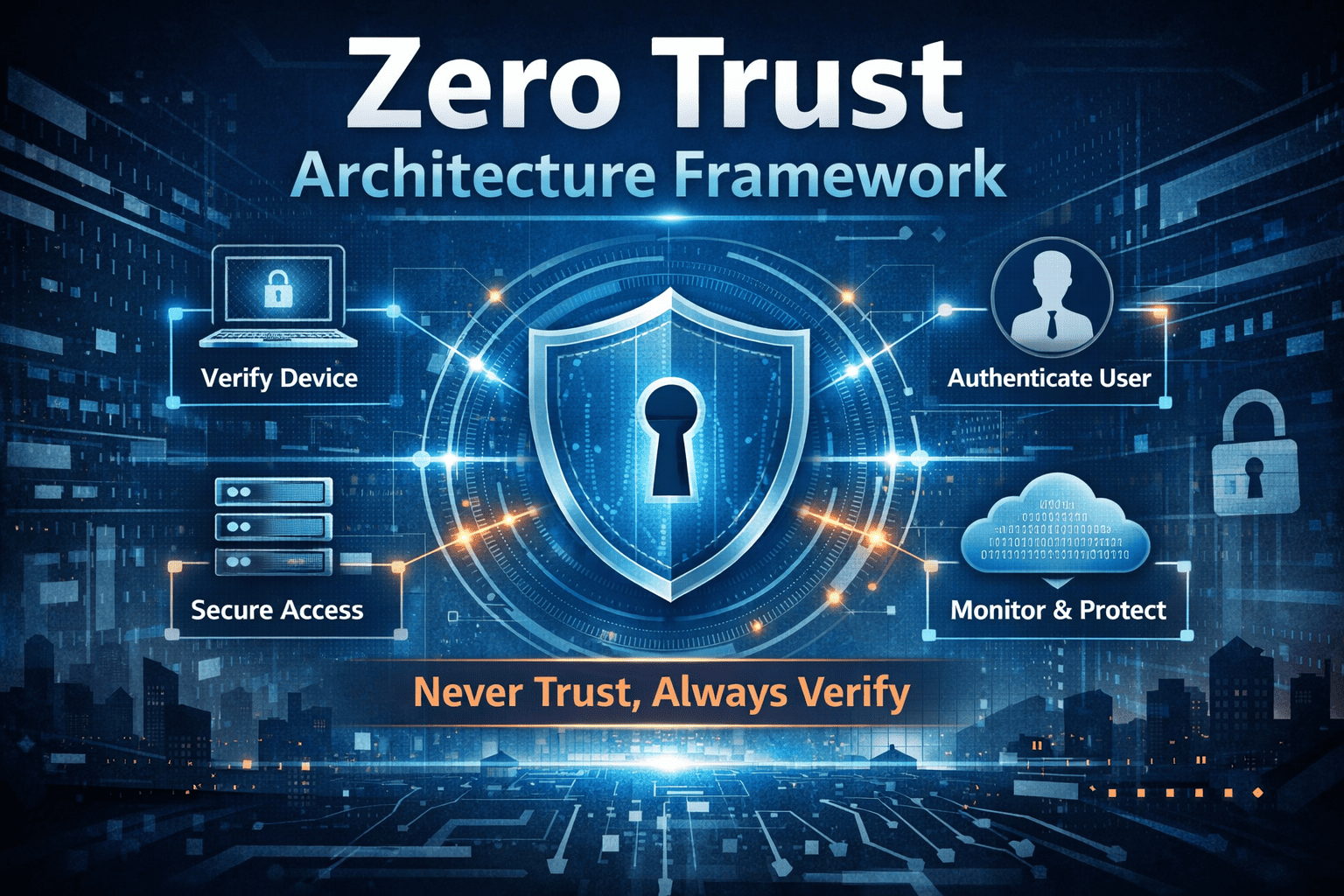
Zero Trust Architecture Framework
Updated on March 6, 2026, by Xcitium
Cybersecurity threats are evolving rapidly, and traditional security models are struggling to keep up. For decades, organizations relied on perimeter-based security—protecting the network boundary while trusting everything inside it. But today’s distributed environments, cloud services, and remote workforces have made that approach obsolete.
This is where the Zero Trust Architecture Framework comes in.
Instead of assuming that internal users or devices are safe, Zero Trust operates on a simple principle: “Never trust, always verify.” Every access request must be authenticated, authorized, and continuously validated.
In this comprehensive guide, we’ll explore the Zero Trust Architecture Framework, how it works, its core components, and how organizations can implement it to strengthen their cybersecurity posture.
What Is the Zero Trust Architecture Framework?
The Zero Trust Architecture Framework is a cybersecurity model that eliminates implicit trust in networks, users, or devices. Every entity requesting access to systems or data must be verified before access is granted.
Unlike traditional security models that rely on a secure perimeter, Zero Trust assumes that threats can originate from anywhere—inside or outside the network.
Core Idea of Zero Trust
The foundation of Zero Trust is built on three key principles:
-
Verify every user and device
-
Limit access to only what is necessary
-
Continuously monitor and validate activity
This approach helps organizations reduce the risk of data breaches and unauthorized access.
Why Organizations Are Moving to Zero Trust
Modern IT environments have become more complex than ever.
Organizations now rely on:
-
Cloud platforms
-
Remote workforces
-
Mobile devices
-
Third-party integrations
-
Internet-connected applications
These changes have expanded the attack surface.
Challenges with Traditional Security Models
Traditional security approaches often fail because:
-
Internal networks are trusted automatically
-
Lateral movement within networks is easier for attackers
-
Remote access introduces vulnerabilities
-
Cloud environments extend beyond the corporate perimeter
The Zero Trust Architecture Framework addresses these weaknesses by enforcing strict access controls.
Key Principles of the Zero Trust Architecture Framework
Understanding the principles behind Zero Trust is essential for successful implementation.
Continuous Identity Verification
Every user and device attempting to access resources must be authenticated.
Identity-Based Security
Authentication mechanisms may include:
-
Multi-factor authentication (MFA)
-
Single sign-on (SSO)
-
Identity federation
-
Behavioral analytics
Identity verification ensures that only authorized users access sensitive resources.
Least Privilege Access
The Zero Trust model enforces the principle of least privilege.
This means users receive only the access they need to perform their tasks.
Benefits of Least Privilege
-
Reduced insider threats
-
Limited impact of compromised accounts
-
Stronger data protection
Limiting access reduces the risk of unauthorized actions.
Continuous Monitoring and Validation
Zero Trust does not stop at authentication.
Every activity must be monitored in real time.
Security Monitoring Techniques
Organizations monitor:
-
User behavior
-
Device health
-
Network traffic
-
Application activity
Continuous monitoring helps detect anomalies quickly.
Core Components of Zero Trust Architecture
Implementing the Zero Trust Architecture Framework requires multiple technologies working together.
Identity and Access Management (IAM)
Identity management is the foundation of Zero Trust.
IAM solutions help organizations control who can access systems and applications.
Key IAM Capabilities
-
Identity verification
-
Role-based access control (RBAC)
-
Access policy enforcement
-
Authentication monitoring
Strong identity controls prevent unauthorized access.
Endpoint Security
Every device connecting to the network must meet security requirements.
Endpoint Security Measures
Organizations monitor device status such as:
-
Operating system updates
-
Antivirus status
-
Security configuration
Devices failing security checks may be blocked from accessing resources.
Network Segmentation
Network segmentation divides infrastructure into smaller zones.
Benefits of Microsegmentation
Microsegmentation helps:
-
Prevent lateral movement
-
Isolate compromised systems
-
Reduce attack impact
Segmentation limits attackers’ ability to move within networks.
Secure Access Service Edge (SASE)
SASE combines networking and security capabilities into a cloud-based platform.
SASE Features
-
Secure web gateways
-
Cloud access security brokers (CASB)
-
Zero Trust network access (ZTNA)
SASE helps organizations enforce Zero Trust policies across distributed environments.
How the Zero Trust Architecture Framework Works
Zero Trust frameworks follow a structured approach when evaluating access requests.
Step-by-Step Access Process
-
A user or device requests access to a resource.
-
Identity and device status are verified.
-
Access policies evaluate risk factors.
-
Access is granted only if security requirements are met.
-
Activity is continuously monitored.
This process ensures that trust is never assumed.
Benefits of Implementing Zero Trust Architecture
Organizations adopting the Zero Trust Architecture Framework gain several advantages.
Stronger Data Protection
Sensitive data remains protected even if attackers breach network boundaries.
Reduced Attack Surface
Strict access controls limit opportunities for cybercriminals.
Improved Visibility
Security teams gain better insight into user activity and network traffic.
Better Compliance
Zero Trust supports regulatory frameworks such as:
-
GDPR
-
HIPAA
-
PCI-DSS
-
ISO 27001
Challenges in Implementing Zero Trust
Despite its benefits, implementing Zero Trust requires careful planning.
Integration Complexity
Legacy systems may not support modern authentication protocols.
Organizational Resistance
Employees may initially find stricter access controls inconvenient.
Resource Requirements
Implementing Zero Trust technologies requires investment in infrastructure and expertise.
However, the long-term benefits significantly outweigh these challenges.
Steps to Implement the Zero Trust Architecture Framework
Organizations can follow a structured approach to implement Zero Trust.
Step 1: Identify Critical Assets
Begin by identifying sensitive systems, applications, and data.
Understanding what needs protection is the first step.
Step 2: Map User and Device Access
Document how users and devices interact with systems.
This helps identify potential vulnerabilities.
Step 3: Implement Strong Authentication
Introduce multi-factor authentication and identity verification processes.
Authentication is a core component of Zero Trust.
Step 4: Segment the Network
Use microsegmentation to isolate systems and prevent lateral movement.
Step 5: Deploy Monitoring Tools
Continuous monitoring ensures threats are detected early.
Zero Trust vs Traditional Security Models
The Zero Trust model differs significantly from traditional security approaches.
| Traditional Security | Zero Trust Architecture |
|---|---|
| Trust inside network | Verify every request |
| Perimeter-based defense | Identity-based defense |
| Limited monitoring | Continuous monitoring |
| Static access controls | Dynamic policy enforcement |
Zero Trust provides stronger protection in modern distributed environments.
Industries Adopting Zero Trust Security
Organizations across industries are implementing the Zero Trust Architecture Framework.
Financial Services
Banks protect customer data and financial systems.
Healthcare
Hospitals secure patient records and medical devices.
Government Agencies
Public sector organizations protect sensitive national data.
Technology Companies
Tech companies secure cloud infrastructure and development environments.
Future Trends in Zero Trust Security
Zero Trust continues to evolve alongside emerging technologies.
Key trends include:
-
AI-powered threat detection
-
Automated policy enforcement
-
Cloud-native security architectures
-
Integration with DevSecOps pipelines
These advancements will further strengthen cybersecurity resilience.
Frequently Asked Questions (FAQ)
1. What is Zero Trust Architecture?
Zero Trust Architecture is a cybersecurity model that requires continuous verification of users, devices, and systems before granting access.
2. Why is Zero Trust important?
It reduces the risk of data breaches by eliminating implicit trust and enforcing strict access controls.
3. Is Zero Trust only for large enterprises?
No. Organizations of all sizes can implement Zero Trust principles to improve security.
4. What technologies support Zero Trust?
Technologies include identity management, endpoint security, microsegmentation, and continuous monitoring tools.
5. How long does it take to implement Zero Trust?
Implementation timelines vary depending on infrastructure complexity, but most organizations adopt it gradually.
Final Thoughts: Building a Strong Zero Trust Security Strategy
Cyber threats continue to evolve, and traditional security models can no longer provide adequate protection. The Zero Trust Architecture Framework offers a modern approach that focuses on identity verification, least privilege access, and continuous monitoring.
By implementing Zero Trust principles, organizations can reduce cyber risks, improve visibility, and strengthen their overall security posture.
If your organization is ready to modernize its cybersecurity strategy and protect critical systems from advanced threats, now is the time to act.
👉 Request a demo today:
https://www.xcitium.com/request-demo/
Discover how advanced cybersecurity solutions can help your organization implement Zero Trust and stay ahead of evolving cyber threats.