- July 23, 2025
- 5 mins
Have you ever plugged in your Ethernet cable expecting a fast, reliable internet connection—only...

- July 23, 2025
- 5 mins
If you’ve ever wondered what is a thread in programming, you’re not alone. In today’s...
- July 21, 2025
- 4 mins
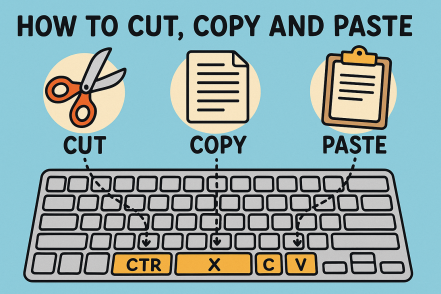
Have you ever wondered how to cut, copy and paste on keyboard without using your mouse? Whether...

- July 21, 2025
- 4 mins
Have you noticed your Android phone slowing down, overheating, or showing pop-ups out of nowhere?...
- July 21, 2025
- 4 mins
Have you ever opened an incognito tab and then asked yourself, “How do I exit Incognito Mode?”...
- July 21, 2025
- 4 mins
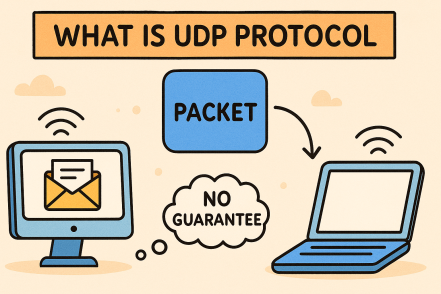
Have you ever streamed a video, played an online game, or made a VoIP call and wondered how it all...

- July 18, 2025
- 4 mins
Ever received a text asking you to “confirm your account” or “verify payment”? You might be...
- July 18, 2025
- 4 mins
Ever wondered what is API gateway and why it’s suddenly everywhere in cloud discussions? In...
- July 18, 2025
- 5 mins
Ever wondered what is IPsec and why cybersecurity professionals rely on it to protect data in...








