- November 07, 2025
- 8 mins
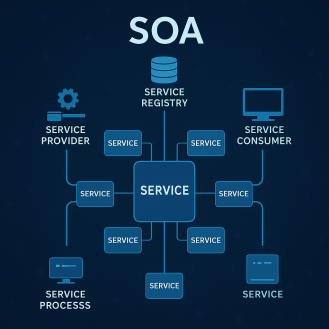
In an age where digital transformation drives business success, the ability to connect multiple...

- November 07, 2025
- 7 mins
In cybersecurity and data management, the term hash function often appears in discussions about...
- November 06, 2025
- 7 mins
Artificial Intelligence, or AI, has become one of the most transformative technologies of the 21st...
- November 06, 2025
- 8 mins
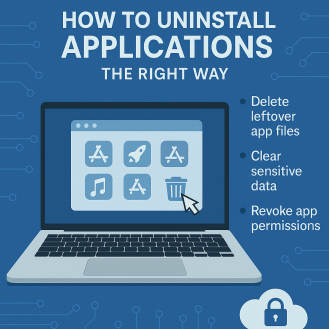
Are unused apps cluttering your Mac and slowing it down? You’re not alone. Many users install new...

- November 05, 2025
- 8 mins
Have you ever wondered how companies gather massive amounts of data from websites — everything...
- November 05, 2025
- 8 mins
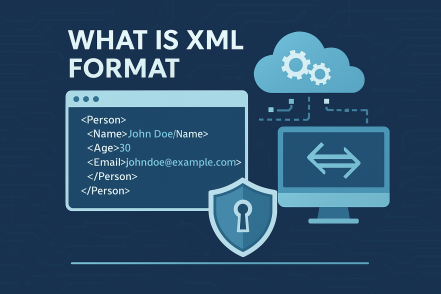
Have you ever wondered how applications, websites, and business systems exchange information so...

- November 05, 2025
- 7 mins
Have you ever wondered what is ESG in business and why it’s suddenly the talk of boardrooms,...

- November 05, 2025
- 8 mins
Have you ever wondered how your antivirus software detects and blocks threats the moment they...
- November 04, 2025
- 8 mins
When you power on your computer or smartphone, millions of operations begin instantly — from...








