- December 26, 2025
- 6 mins
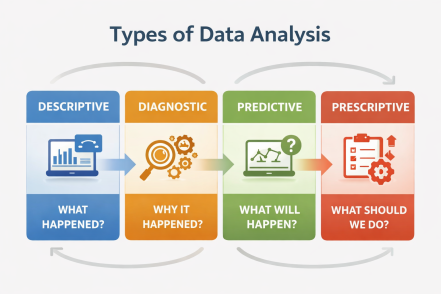
What separates high-performing organizations from those that struggle to keep up? The answer often...
- December 26, 2025
- 6 mins
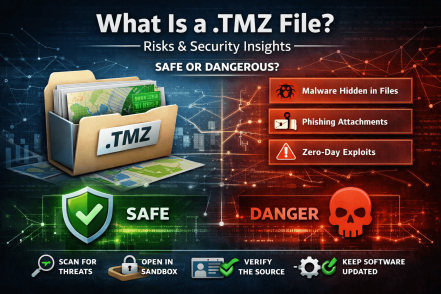
Have you ever received a file with a .tmz extension and wondered whether it’s safe to open?...
- December 24, 2025
- 6 mins
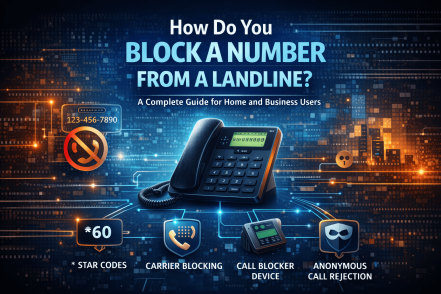
If your phone rings nonstop with spam, robocalls, or unwanted solicitations, you’re not alone....
- December 24, 2025
- 6 mins
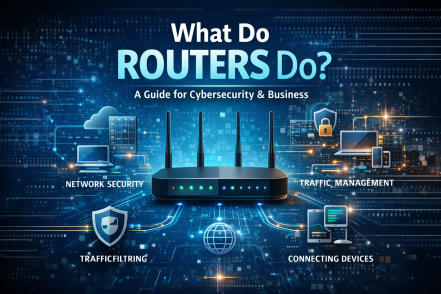
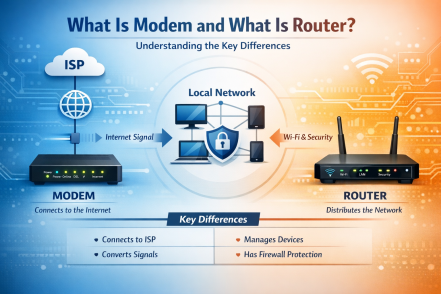
Have you ever stopped to think about what do routers do every time you send an email, join a video...
- December 24, 2025
- 6 mins
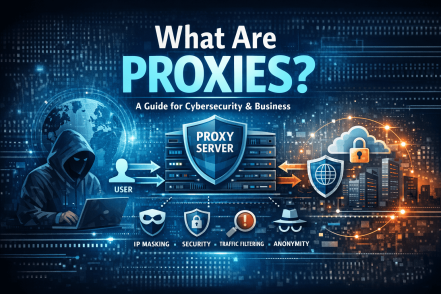
Have you ever wondered what happens behind the scenes when you browse the internet securely?In a...

- December 23, 2025
- 6 mins
Have you ever built a webpage that looked perfect in theory but slightly “off” in practice...

- December 23, 2025
- 7 mins
How secure is your organization’s network perimeter today? With cyberattacks increasing in volume...
- December 23, 2025
- 7 mins
Have you ever wondered why your internet suddenly slows down or why a security breach can start at...
- December 22, 2025
- 5 mins
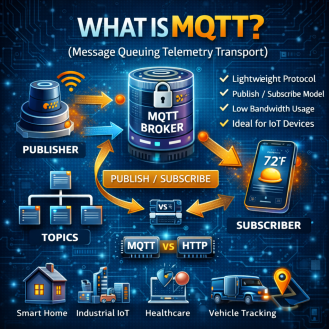
In a world where billions of devices communicate every second, speed and reliability matter. But...








