
- December 31, 2025
- 7 mins
Modern IT systems rarely operate in isolation. Applications, databases, cloud platforms, and...

- December 31, 2025
- 7 mins
If you’ve ever opened Task Manager and seen multiple processes named svchost.exe, you’re not...

- December 31, 2025
- 7 mins
What does breach mean in today’s digital world—and why does it matter so much to businesses?...

- December 30, 2025
- 6 mins
What is NAT networking, and why does almost every modern network depend on it? As organizations...
- December 30, 2025
- 6 mins
In today’s hyper-connected business environment, network performance and security can make or...

- December 30, 2025
- 6 mins
What is SOC 2, and why are so many customers asking for it before signing contracts? In today’s...
- December 29, 2025
- 6 mins
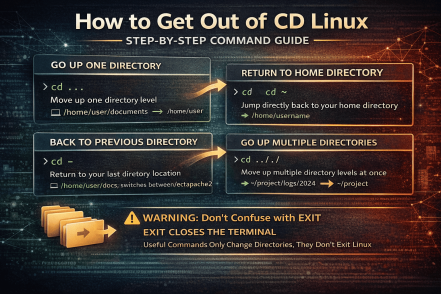
Have you ever typed a command in Linux, only to find yourself stuck inside a directory and unsure...
- December 29, 2025
- 5 mins
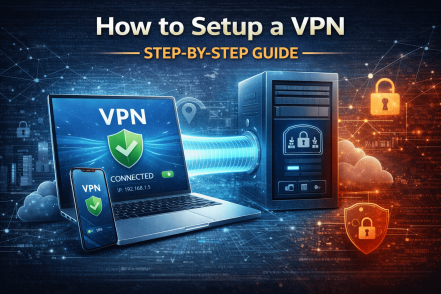
In an era of remote work, cloud services, and constant cyber threats, knowing how to setup a VPN is...
- December 29, 2025
- 5 mins
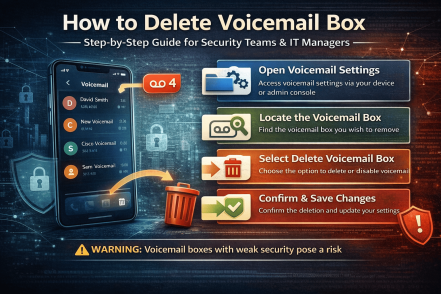
Have you ever wondered whether old voicemail boxes pose a security risk? Many organizations...








