- January 20, 2026
- 6 mins
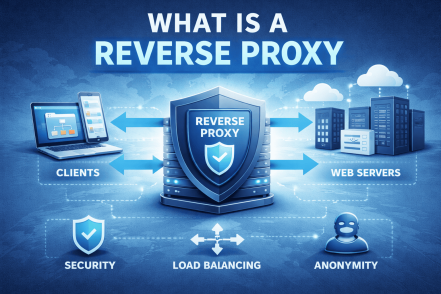
Have you ever wondered how large websites stay fast, secure, and available even during massive...
- January 20, 2026
- 5 mins
Do you waste time searching for shared files or repeatedly entering network paths? If so, learning...
- January 20, 2026
- 6 mins
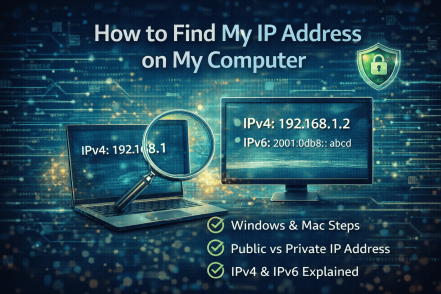
Have you ever needed your IP address to troubleshoot a network issue, configure security settings,...

- January 19, 2026
- 6 mins
How many suspicious emails land in your inbox every week? For many professionals, it’s more than...

- January 19, 2026
- 6 mins
What happens when attackers are allowed to think they’ve broken into your system—while you...
- January 19, 2026
- 5 mins
What do you do when your PC refuses to start normally, crashes repeatedly, or behaves suspiciously...
- January 14, 2026
- 6 mins
If you’re building a career in cybersecurity or leading an organization responsible for...
- January 14, 2026
- 6 mins
Have you ever wondered how computers understand everything from emails to videos using only...

- January 14, 2026
- 7 mins
How do large networks stay organized, secure, and reliable as they scale? If you’re asking what...








