What Is Cyber Resilience? A Complete Guide for Modern Businesses
Updated on March 25, 2026, by Xcitium
What happens if your organization is hit by a cyberattack today—would you recover quickly or face major disruption? That’s why understanding what is cyber resilience has become critical for businesses of all sizes.
Cyber threats are no longer a matter of “if” but “when.” Traditional security focuses on prevention, but modern organizations must also prepare to respond and recover. This is where cyber resilience comes in.
In this guide, we’ll explain what is cyber resilience, why it matters, and how you can build a resilient cybersecurity strategy for your organization.
What Is Cyber Resilience?
What is cyber resilience? Cyber resilience is the ability of an organization to prepare for, respond to, and recover from cyberattacks while continuing normal operations.
It combines:
- Cybersecurity
- Business continuity
- Risk management
Unlike traditional security, which focuses only on prevention, cyber resilience ensures your organization can bounce back quickly after an incident.
Why Cyber Resilience Is Important
Understanding what is cyber resilience helps organizations shift from reactive to proactive security.
Key Reasons It Matters:
- Increasing Cyberattacks: Ransomware and data breaches are rising
- Business Continuity Needs: Downtime can cost millions
- Regulatory Requirements: Compliance demands resilience planning
- Reputation Protection: Customers expect secure services
Without cyber resilience, even a small attack can cause major damage.
Cyber Resilience vs Cybersecurity
Many people confuse these terms.
Key Differences:
| Cybersecurity | Cyber Resilience |
|---|---|
| Focuses on prevention | Focuses on prevention + recovery |
| Blocks threats | Ensures continuity during attacks |
| Reactive approach | Proactive + adaptive approach |
Cybersecurity is part of cyber resilience—but resilience goes further.
Core Components of Cyber Resilience
To fully understand what is cyber resilience, you need to know its key components.
1. Risk Management
Identify and assess potential threats.
This includes:
- Vulnerability assessments
- Threat modeling
- Risk prioritization
2. Threat Prevention
Prevent attacks using strong security controls.
Examples:
- Firewalls
- Endpoint security
- Access controls
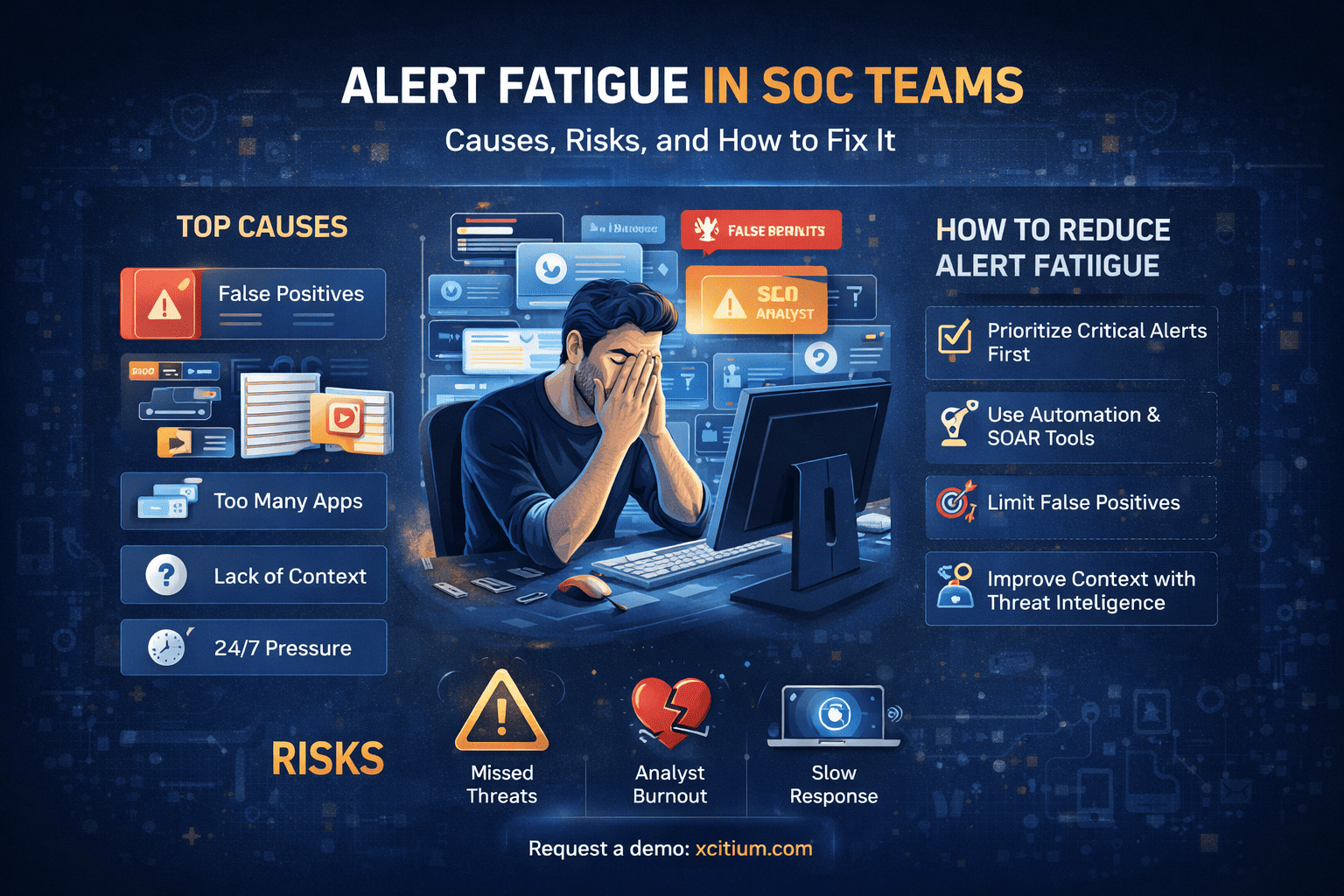
3. Detection and Monitoring
Quick detection reduces damage.
Use:
- SIEM systems
- Continuous monitoring tools
- AI-based threat detection
4. Incident Response
Prepare for when attacks happen.
This includes:
- Response plans
- Defined roles and responsibilities
- Communication strategies
5. Recovery and Continuity
Recovery is a key part of what is cyber resilience.
Ensure:
- Data backups
- Disaster recovery plans
- Business continuity processes
Benefits of Cyber Resilience
Implementing cyber resilience offers several advantages.
1. Reduced Downtime
Quick recovery minimizes business disruption.
2. Improved Risk Management
Identify and address risks proactively.
3. Stronger Security Posture
Combine prevention, detection, and recovery.
4. Regulatory Compliance
Meet industry standards more easily.
5. Customer Trust
Build confidence with secure operations.
Common Challenges in Building Cyber Resilience
Despite its importance, organizations face challenges.
Lack of Awareness
Many businesses focus only on prevention.
Complex IT Environments
Hybrid and cloud systems increase complexity.
Limited Resources
Smaller teams struggle to manage everything.
Evolving Threats
Cyber threats constantly change.
Overcoming these challenges is essential for achieving true cyber resilience.
Best Practices to Build Cyber Resilience
To implement what is cyber resilience effectively, follow these best practices:
Adopt a Zero Trust Model
Verify every user and device.
Regularly Test Incident Response Plans
Run simulations to ensure readiness.
Implement Continuous Monitoring
Detect threats in real time.
Backup Critical Data
Ensure quick recovery after attacks.
Train Employees
Reduce human error through awareness.
Role of Zero Trust in Cyber Resilience
Zero Trust plays a major role in cyber resilience.
Key Principles:
- Never trust, always verify
- Limit access based on risk
- Monitor continuously
This approach reduces the impact of cyberattacks and supports faster recovery.
Real-World Example
A company experienced a ransomware attack.
Because it had a cyber resilience strategy:
- Systems were isolated quickly
- Backups were restored
- Operations resumed within hours
Without resilience, recovery could have taken weeks.
Cyber Resilience Frameworks
Organizations can follow established frameworks to build resilience.
Popular Frameworks:
- NIST Cybersecurity Framework
- ISO 27001
- CIS Controls
These provide structured guidance for improving resilience.
Future Trends in Cyber Resilience
The future of what is cyber resilience is evolving rapidly.
Emerging Trends:
- AI-driven threat detection
- Automated incident response
- Cloud-native resilience solutions
- Integration with Zero Trust
Organizations adopting these trends will be better prepared for future threats.
How to Get Started with Cyber Resilience
Building cyber resilience doesn’t have to be overwhelming.
Follow These Steps:
- Assess your current security posture
- Identify critical assets
- Implement layered security controls
- Develop incident response plans
- Continuously monitor and improve
Conclusion
So, what is cyber resilience? It’s the ability to prepare for, respond to, and recover from cyber threats while maintaining business operations.
In today’s threat landscape, prevention alone is not enough. Organizations must focus on resilience to:
- Minimize impact
- Recover quickly
- Stay competitive
Cyber resilience is not just a security strategy—it’s a business necessity.
🚀 Strengthen Your Cyber Resilience Today
Don’t wait for a cyberattack to test your defenses.
👉 Request a demo now: https://www.xcitium.com/request-demo/
FAQs: What Is Cyber Resilience?
1. What is cyber resilience in simple terms?
It is the ability to prevent, respond to, and recover from cyberattacks effectively.
2. How is cyber resilience different from cybersecurity?
Cybersecurity focuses on prevention, while cyber resilience includes recovery and continuity.
3. Why is cyber resilience important for businesses?
It reduces downtime, protects data, and ensures business continuity during attacks.
4. What tools support cyber resilience?
SIEM, EDR, backup systems, and Zero Trust platforms support resilience.
5. How can organizations improve cyber resilience?
By implementing strong security controls, training employees, and preparing for incident response.