Secure Access Service Edge Architecture
Updated on March 6, 2026, by Xcitium
Modern organizations are rapidly shifting toward cloud infrastructure, remote work, and distributed applications. While this digital transformation improves productivity and flexibility, it also introduces new security challenges. Traditional network security models—built around centralized data centers—struggle to protect today’s cloud-first environments.
This is where Secure Access Service Edge architecture comes into play.
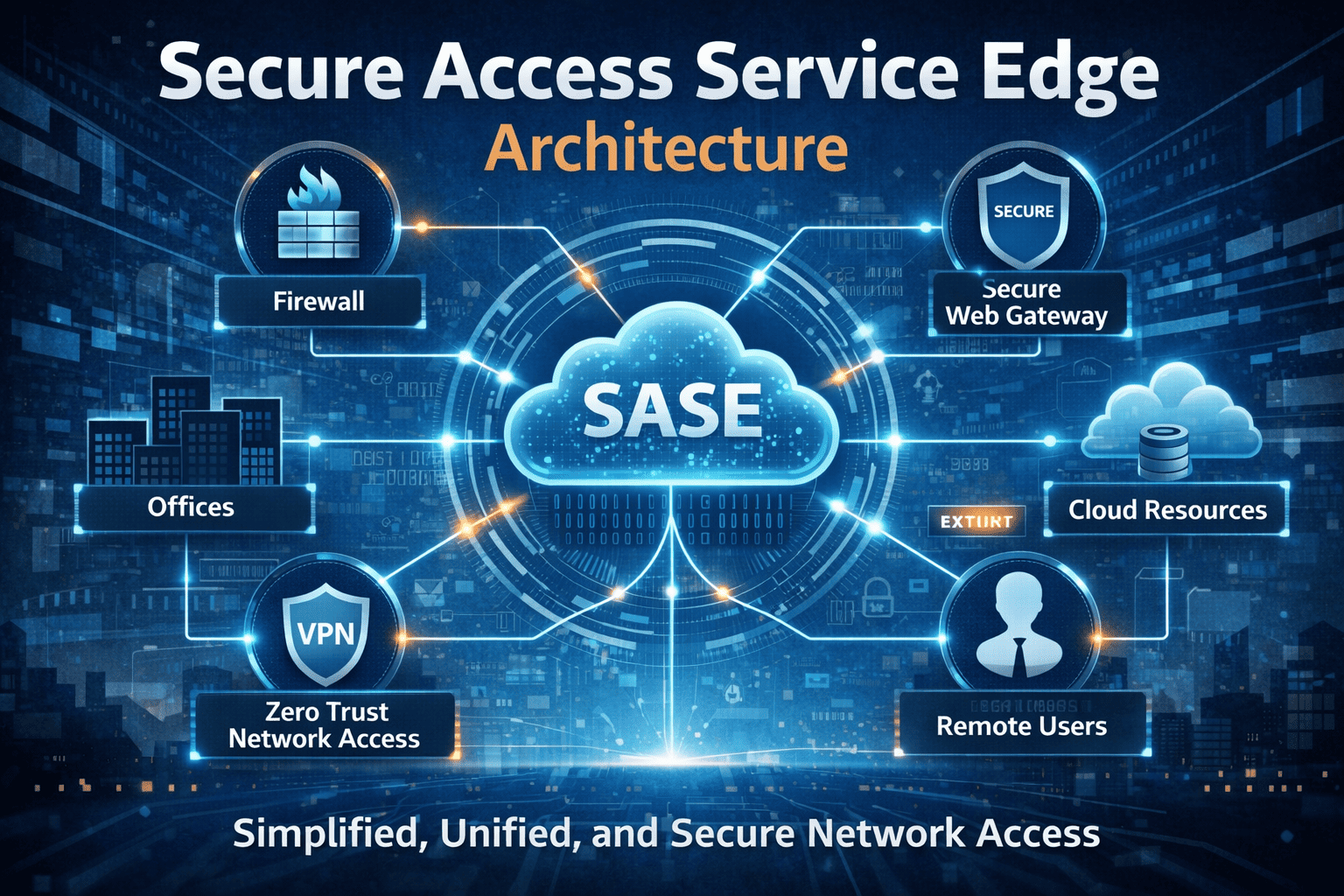
Secure Access Service Edge (SASE) combines networking and security services into a unified cloud-based framework. Instead of relying on traditional perimeter defenses, SASE delivers security directly from the cloud, allowing organizations to protect users, devices, and applications regardless of location.
In this guide, we’ll explore Secure Access Service Edge architecture, its key components, benefits, and best practices for implementation.
What Is Secure Access Service Edge (SASE)?
Secure Access Service Edge architecture is a cloud-native cybersecurity framework that integrates networking and security functions into a single platform. The term was introduced by Gartner to describe the convergence of networking and security services delivered through the cloud.
Unlike traditional security models that rely on hardware appliances and centralized gateways, SASE delivers security controls closer to users and applications.
Core Concept of SASE
Secure Access Service Edge architecture focuses on providing:
-
Identity-driven access control
-
Cloud-delivered security services
-
Secure connectivity for remote users
-
Scalable protection for cloud applications
This approach helps organizations secure distributed environments without sacrificing performance.
Why Organizations Need SASE Architecture
Modern IT environments have changed dramatically in the past decade. Employees now access applications from multiple devices and locations.
Key Drivers Behind SASE Adoption
Organizations are adopting Secure Access Service Edge architecture due to:
-
Remote and hybrid work environments
-
Increased cloud adoption
-
Rising cybersecurity threats
-
Growing network complexity
-
Demand for scalable security solutions
Traditional perimeter-based security cannot effectively protect modern distributed networks.
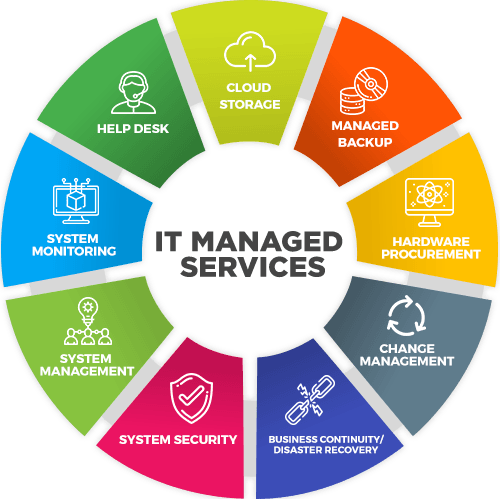
Key Components of Secure Access Service Edge Architecture
Secure Access Service Edge architecture integrates multiple security and networking capabilities into a single framework.
Software-Defined Wide Area Network (SD-WAN)
SD-WAN provides intelligent network connectivity between users, branch offices, and cloud services.
Benefits of SD-WAN
-
Optimized network performance
-
Reduced latency
-
Improved bandwidth management
-
Better cloud connectivity
SD-WAN forms the networking backbone of SASE architecture.
Secure Web Gateway (SWG)
A Secure Web Gateway protects users from malicious web traffic and unsafe websites.
SWG Capabilities
Secure Access Service Edge architecture uses SWG to:
-
Block malicious URLs
-
Enforce internet usage policies
-
Prevent malware downloads
-
Monitor web traffic
SWG ensures safe browsing for users accessing internet resources.
Cloud Access Security Broker (CASB)
CASB solutions protect data and applications hosted in cloud environments.
CASB Functions
CASB tools provide:
-
Data loss prevention (DLP)
-
Cloud application monitoring
-
Threat detection
-
Access control enforcement
This component helps organizations secure SaaS platforms like Google Workspace and Microsoft 365.
Zero Trust Network Access (ZTNA)
ZTNA is a key component of Secure Access Service Edge architecture.
Instead of granting broad network access, ZTNA provides access only to specific applications.
Advantages of ZTNA
-
Eliminates traditional VPN vulnerabilities
-
Reduces lateral movement inside networks
-
Enforces identity-based access control
ZTNA aligns with the Zero Trust security model.
Firewall as a Service (FWaaS)
Firewall as a Service delivers firewall capabilities through cloud infrastructure.
FWaaS Features
Organizations benefit from:
-
Network traffic inspection
-
Intrusion prevention systems
-
Application-level filtering
-
Threat intelligence integration
FWaaS protects networks without requiring on-premise hardware.
How Secure Access Service Edge Architecture Works
Secure Access Service Edge architecture works by delivering security and networking services through a distributed cloud platform.
Step-by-Step Workflow
-
A user attempts to access an application or service.
-
The SASE platform verifies identity and device security.
-
Traffic is routed through cloud security services.
-
Security policies evaluate access permissions.
-
Access is granted only if security conditions are met.
This architecture ensures secure access without compromising performance.
Benefits of Secure Access Service Edge Architecture
Organizations adopting SASE gain several operational and security advantages.
Improved Security Posture
SASE integrates multiple security controls into a unified framework, reducing security gaps.
Better Performance for Remote Users
Cloud-based security reduces latency for remote workers accessing cloud applications.
Simplified Network Management
Centralized management dashboards simplify policy enforcement and monitoring.
Scalability
Secure Access Service Edge architecture scales easily to support growing users and devices.
Reduced Infrastructure Costs
Organizations can reduce reliance on expensive hardware appliances.
SASE vs Traditional Network Security
The Secure Access Service Edge architecture differs significantly from traditional security approaches.
| Traditional Security | SASE Architecture |
|---|---|
| Hardware-based security | Cloud-delivered security |
| Perimeter-focused | Identity-focused |
| Static network routing | Dynamic traffic routing |
| Separate networking and security | Integrated platform |
SASE provides a modern security framework designed for cloud environments.
Best Practices for Implementing Secure Access Service Edge Architecture
Implementing SASE requires careful planning and strategic execution.
Assess Current Infrastructure
Organizations should begin by evaluating their existing network and security architecture.
Identify gaps that SASE can address.
Adopt Zero Trust Principles
Zero Trust security is essential for successful SASE deployment.
Ensure access decisions are based on:
-
User identity
-
Device posture
-
Application sensitivity
Secure Cloud Applications
Cloud services must be integrated with CASB and identity management systems.
This ensures consistent policy enforcement across environments.
Monitor Network Traffic
Continuous monitoring helps identify suspicious activity and security incidents.
Security analytics tools improve visibility across networks.
Train Security Teams
Security teams must understand how to manage and monitor SASE environments effectively.
Proper training improves operational efficiency.
Challenges in Deploying SASE Architecture
Despite its advantages, implementing SASE may present challenges.
Integration Complexity
Organizations with legacy infrastructure may face integration issues.
Vendor Selection
Choosing the right SASE vendor is critical for long-term success.
Organizational Change
Adopting cloud-native security models requires cultural and operational shifts.
Proper planning helps overcome these challenges.
The Future of Secure Access Service Edge Architecture
SASE continues to evolve as organizations embrace digital transformation.
Emerging trends include:
-
AI-driven threat detection
-
Automated policy management
-
Integration with Zero Trust security frameworks
-
Cloud-native security platforms
These innovations will further strengthen cybersecurity resilience.
Frequently Asked Questions (FAQ)
1. What is Secure Access Service Edge architecture?
Secure Access Service Edge architecture is a cloud-based framework that integrates networking and security services to protect users, devices, and applications.
2. Why is SASE important for modern organizations?
SASE secures distributed workforces, cloud environments, and remote access while improving network performance.
3. How does SASE differ from traditional VPN solutions?
SASE provides identity-based access control and cloud-delivered security instead of relying on centralized VPN gateways.
4. What are the main components of SASE?
Key components include SD-WAN, Secure Web Gateway, CASB, Zero Trust Network Access, and Firewall as a Service.
5. Is SASE suitable for small businesses?
Yes. SASE platforms are scalable and can support organizations of various sizes.
Final Thoughts: Building a Modern Security Strategy with SASE
Cybersecurity and networking are no longer separate domains. As organizations adopt cloud services and remote work models, security strategies must evolve accordingly.
Secure Access Service Edge architecture provides a modern solution by integrating networking and security into a unified cloud platform. By adopting SASE, organizations can improve security visibility, reduce infrastructure complexity, and provide secure access to applications from anywhere.
If your organization is ready to modernize its cybersecurity architecture and protect distributed environments, it’s time to explore advanced security solutions.
👉 Request a demo today:
https://www.xcitium.com/request-demo/
Discover how next-generation cybersecurity technologies can help secure your organization’s network, applications, and data in the modern digital landscape.