Remote Desktop Protocol (RDP) Security Risks: What Every Business Must Know
Updated on March 24, 2026, by Xcitium
Is your organization using Remote Desktop for remote access? If so, you must understand the growing Remote Desktop Protocol (RDP) Security Risks that threaten businesses worldwide.
RDP has become essential for remote work and IT management. However, it is also one of the most targeted entry points for cybercriminals. In fact, many ransomware attacks begin with compromised RDP access.
In this guide, we’ll explore the biggest Remote Desktop Protocol (RDP) Security Risks, why they matter, and how to protect your organization effectively.
What Is Remote Desktop Protocol (RDP)?
Remote Desktop Protocol (RDP) is a Microsoft protocol that allows users to connect to another computer over a network.
It enables:
- Remote system access
- IT troubleshooting
- Server management
While convenient, improper configuration exposes organizations to serious Remote Desktop Protocol (RDP) Security Risks.
Why RDP Is a Major Cybersecurity Target
Cybercriminals actively scan the internet for open RDP ports. Once found, they attempt to gain access using various attack methods.
Key Reasons RDP Is Targeted:
- Widely used across industries
- Often exposed to the internet
- Weak authentication in many setups
- Lack of proper monitoring
This makes Remote Desktop Protocol (RDP) Security Risks a top concern for IT managers and security teams.
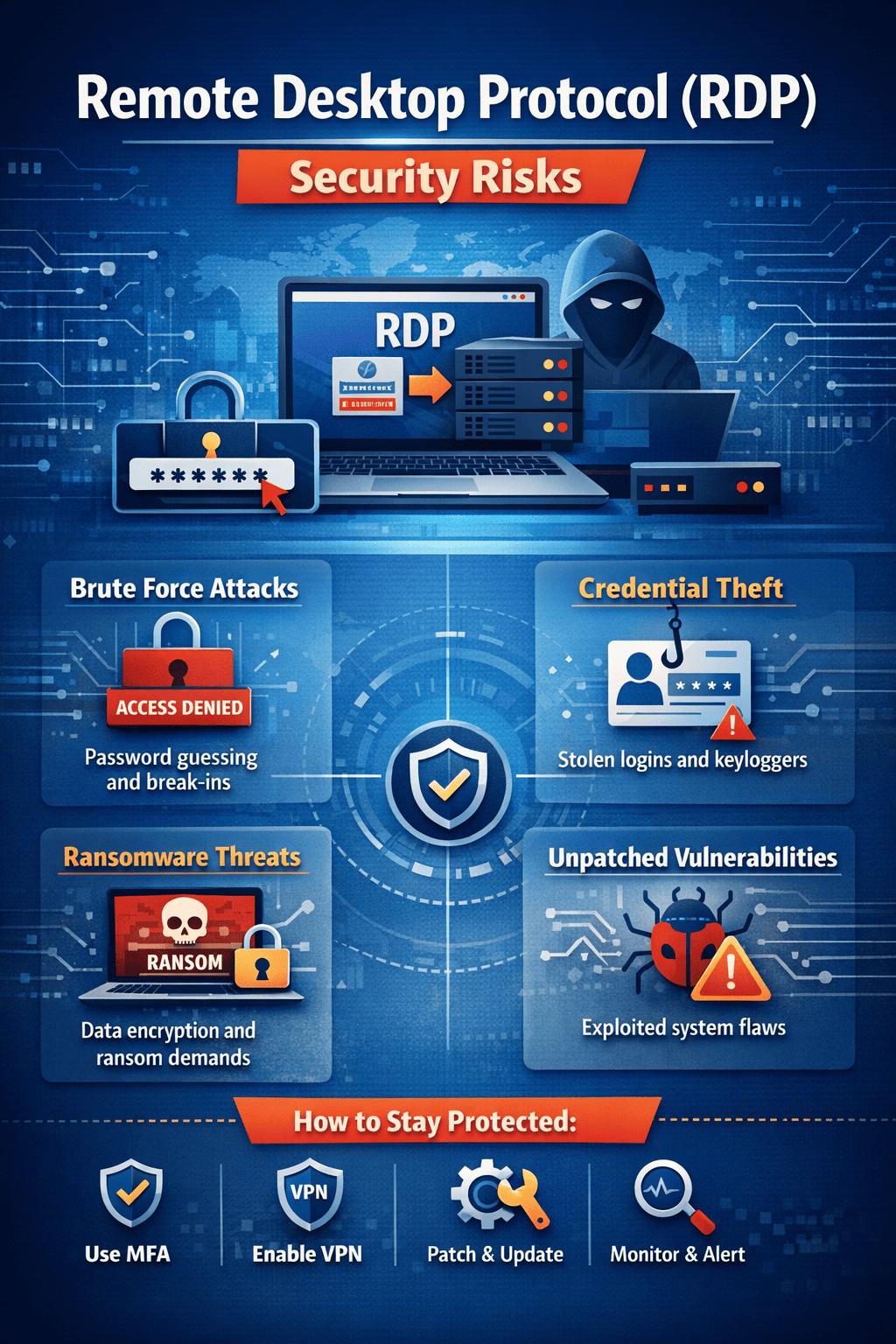
Top Remote Desktop Protocol (RDP) Security Risks
Understanding the risks is the first step to protecting your systems.
1. Brute Force Attacks
One of the most common Remote Desktop Protocol (RDP) Security Risks is brute force attacks.
Attackers:
- Use automated tools
- Try thousands of password combinations
- Gain access if credentials are weak
2. Credential Theft
If attackers steal login credentials, they can access systems without triggering alarms.
Methods include:
- Phishing attacks
- Keyloggers
- Data breaches
This makes credential protection critical.
3. Ransomware Attacks
Many ransomware incidents start with compromised RDP access.
Once inside, attackers:
- Move laterally across networks
- Encrypt critical data
- Demand ransom payments
4. Unpatched Vulnerabilities
Outdated systems expose organizations to known exploits.
For example:
- BlueKeep vulnerability
- Weak encryption protocols
Regular updates are essential to reduce Remote Desktop Protocol (RDP) Security Risks.
5. Misconfigured RDP Settings
Poor configurations can leave systems wide open.
Common mistakes:
- Open RDP ports (3389)
- No firewall restrictions
- Weak access controls
Real-World Impact of RDP Attacks
Consider a scenario:
A company leaves RDP open to the internet without MFA.
- Attackers gain access via brute force
- Install ransomware
- Shut down operations
The result? Financial loss, downtime, and reputational damage—all due to unmanaged Remote Desktop Protocol (RDP) Security Risks.
How to Reduce Remote Desktop Protocol (RDP) Security Risks
The good news is that these risks can be mitigated with the right approach.
1. Use Strong Authentication
Weak passwords are a major vulnerability.
Best practices:
- Enforce complex passwords
- Implement multi-factor authentication (MFA)
- Use account lockout policies
2. Restrict RDP Access
Never expose RDP directly to the internet.
Instead:
- Use VPNs
- Limit access by IP address
- Disable unused accounts
3. Change Default RDP Port
Port 3389 is widely known.
Changing it:
- Reduces automated attack attempts
- Adds an extra layer of security
4. Enable Network Level Authentication (NLA)
NLA requires authentication before a session starts.
This:
- Reduces attack surface
- Prevents unauthorized access
5. Regularly Patch Systems
Keep systems updated to avoid known exploits.
Ensure:
- OS updates are applied
- Security patches are current
- Legacy systems are replaced
6. Monitor and Log RDP Activity
Visibility is key.
Use tools to:
- Track login attempts
- Detect unusual behavior
- Alert on suspicious activity
Best Practices for Secure Remote Desktop Access
To fully address Remote Desktop Protocol (RDP) Security Risks, follow these best practices:
Implement Zero Trust Security
Never trust any user or device by default.
Use Endpoint Protection
Secure all devices accessing RDP.
Apply Least Privilege Access
Limit user permissions.
Use Encryption
Ensure secure communication channels.
Disable RDP When Not Needed
Reduce unnecessary exposure.
The Role of Advanced Security Solutions
Modern threats require modern solutions.
Advanced platforms offer:
- AI-driven threat detection
- Automated response
- Real-time monitoring
Solutions like Xcitium Zero Trust help:
- Prevent unauthorized access
- Contain threats instantly
- Reduce Remote Desktop Protocol (RDP) Security Risks
Future of RDP Security
As remote work grows, RDP security will evolve.
Emerging Trends:
- Increased use of Zero Trust
- AI-based threat detection
- Cloud-based remote access solutions
- Passwordless authentication
Organizations that adapt will stay ahead of attackers.
Conclusion
Remote Desktop Protocol (RDP) Security Risks are a serious concern for modern businesses.
Without proper controls, RDP can become a gateway for cyberattacks, including ransomware and data breaches.
By implementing strong authentication, restricting access, and using advanced security solutions, organizations can:
- Reduce risks
- Improve visibility
- Strengthen cybersecurity posture
🚀 Secure Your Remote Access Today
Don’t let RDP vulnerabilities expose your business.
👉 Request a demo now: https://www.xcitium.com/request-demo/
FAQs: Remote Desktop Protocol (RDP) Security Risks
1. Why is RDP considered risky?
RDP is often targeted by attackers due to weak passwords, open ports, and lack of security controls.
2. What is the biggest RDP threat?
Brute force attacks and ransomware are the most common threats.
3. How can I secure RDP access?
Use MFA, VPNs, strong passwords, and restrict access to trusted networks.
4. Should RDP be exposed to the internet?
No, it should always be protected behind a VPN or firewall.
5. What tools help reduce RDP risks?
Endpoint security, SIEM, SOAR, and Zero Trust platforms help mitigate risks effectively.