Kubernetes Security Risks and Mitigation: A Complete Guide for Modern Enterprises
Updated on March 26, 2026, by Xcitium
Kubernetes has become the backbone of modern cloud-native applications. But with great flexibility comes significant risk. Are your Kubernetes clusters truly secure—or are hidden vulnerabilities putting your business at risk?
Understanding Kubernetes Security Risks and Mitigation is essential for IT leaders, cybersecurity teams, and business decision-makers. Misconfigured clusters, weak access controls, and unprotected workloads can expose sensitive data and disrupt operations.
In this guide, we break down the most critical Kubernetes Security Risks and Mitigation strategies to help you secure your environment effectively.
Why Kubernetes Security Matters More Than Ever
Kubernetes environments are dynamic and complex. Containers spin up and down quickly, making it harder to track vulnerabilities.
Without addressing Kubernetes Security Risks and Mitigation, organizations may face:
- Unauthorized access to clusters
- Data breaches and compliance violations
- Supply chain attacks via container images
- Lateral movement across workloads
As adoption grows, attackers increasingly target Kubernetes environments. Security must be built into every layer.
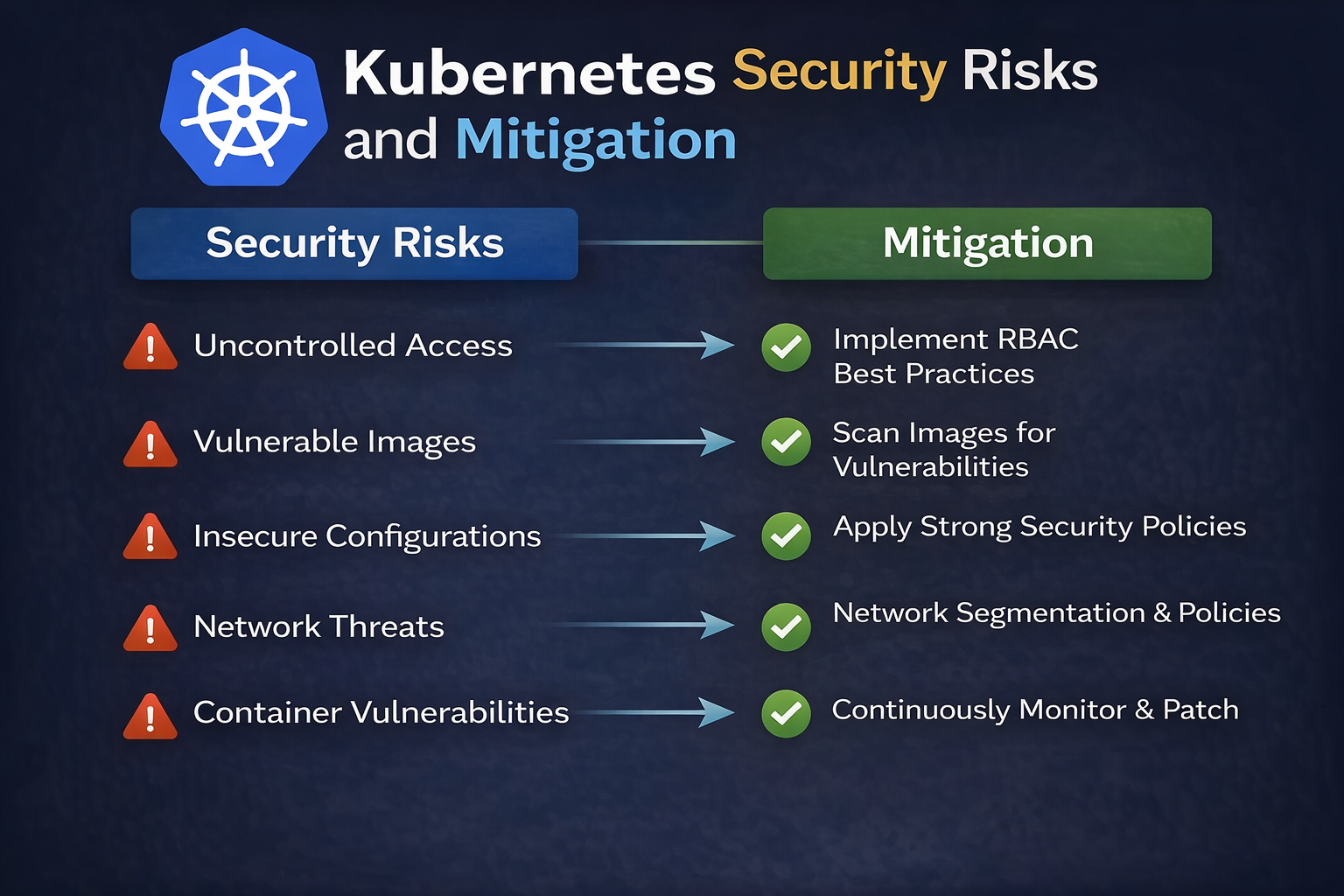
Top Kubernetes Security Risks You Must Know
Before applying solutions, it’s important to understand the key risks.
1. Misconfigured Clusters
One of the most common Kubernetes security risks is misconfiguration.
Examples:
- Open dashboards without authentication
- Exposed etcd databases
- Weak network policies
Misconfigurations often occur due to lack of expertise or rushed deployments.
2. Weak Identity and Access Management (IAM)
Improper access controls can lead to privilege escalation.
Risks Include:
- Over-permissioned users
- Lack of role-based access control (RBAC)
- Shared credentials
Attackers exploit these gaps to gain full control over clusters.
3. Insecure Container Images
Containers are only as secure as the images they are built from.
Common Issues:
- Vulnerable base images
- Embedded secrets
- Outdated libraries
This is a major concern in Kubernetes Security Risks and Mitigation strategies.
4. Lack of Network Segmentation
Without proper network controls, attackers can move freely within clusters.
Risks:
- Lateral movement between pods
- Unauthorized service communication
- Exposure of internal services
5. Insufficient Monitoring and Logging
If you can’t see what’s happening, you can’t stop attacks.
Problems:
- No real-time alerts
- Missing audit logs
- Delayed incident response
6. Secrets Mismanagement
Sensitive data like API keys and passwords are often stored improperly.
Risks:
- Secrets stored in plain text
- Hardcoded credentials in code
- Unauthorized access to secrets
Kubernetes Security Risks and Mitigation: Best Practices
Now let’s focus on how to mitigate these risks effectively.
1. Strengthen Cluster Configuration
Proper configuration is the first step in Kubernetes Security Risks and Mitigation.
Action Steps:
- Disable anonymous access
- Secure the Kubernetes API server
- Restrict access to etcd
- Use secure kubelet settings
Tip:
Follow CIS Kubernetes Benchmarks for standardized security guidelines.
2. Implement Strong RBAC Policies
Role-Based Access Control (RBAC) ensures users only have necessary permissions.
Best Practices:
- Apply the principle of least privilege
- Avoid using cluster-admin roles unnecessarily
- Regularly audit user permissions
- Use separate accounts for different roles
3. Secure Container Images
Container security is critical in Kubernetes environments.
Checklist:
- Use trusted and minimal base images
- Scan images for vulnerabilities
- Avoid storing secrets in images
- Regularly update dependencies
Related Keywords: container security best practices, Kubernetes vulnerability scanning
4. Enforce Network Policies
Network segmentation limits the spread of attacks.
What to Do:
- Define strict network policies
- Restrict pod-to-pod communication
- Use service meshes for encryption
- Monitor network traffic
5. Protect Secrets and Sensitive Data
Proper secrets management is essential for Kubernetes Security Risks and Mitigation.
Best Practices:
- Use Kubernetes Secrets securely
- Encrypt secrets at rest
- Integrate with external secret managers
- Avoid hardcoding credentials
6. Enable Continuous Monitoring and Logging
Visibility is key to preventing and responding to threats.
Tools to Use:
- Kubernetes Audit Logs
- Prometheus and Grafana
- SIEM integrations
- Runtime security tools
Checklist:
- Monitor suspicious activity
- Set up real-time alerts
- Retain logs for compliance
7. Secure the Supply Chain
Software supply chain attacks are on the rise.
Mitigation Steps:
- Verify image sources
- Use signed container images
- Implement CI/CD security checks
- Scan dependencies continuously
Related Keywords: cloud native security, DevSecOps Kubernetes
Common Mistakes to Avoid
Even experienced teams can overlook critical areas.
- Ignoring default security settings
- Over-reliance on perimeter security
- Lack of regular audits
- Not updating Kubernetes versions
- Poor visibility into workloads
Avoiding these mistakes strengthens your overall Kubernetes security posture.
How to Build a Kubernetes Security Strategy
To effectively manage Kubernetes Security Risks and Mitigation, follow a structured approach:
1. Assess Your Current Environment
Identify vulnerabilities and misconfigurations.
2. Prioritize High-Risk Areas
Focus on access control, secrets, and exposed services.
3. Automate Security Processes
Use tools for scanning, monitoring, and compliance.
4. Integrate Security into DevOps
Adopt DevSecOps practices to secure applications early.
5. Continuously Improve
Regularly review and update your security measures.
Future of Kubernetes Security
The future of Kubernetes security lies in:
- Zero Trust architecture
- AI-driven threat detection
- Unified platforms like CNAPP
- Automated remediation
Organizations that embrace these trends will stay ahead of evolving threats.
Conclusion: Secure Your Kubernetes Environment Today
Understanding Kubernetes Security Risks and Mitigation is essential for protecting modern cloud-native applications.
From misconfigurations to weak access controls, risks are everywhere—but so are solutions. By implementing best practices like RBAC, network policies, and continuous monitoring, organizations can significantly reduce their attack surface.
👉 Ready to strengthen your Kubernetes security?
Request a demo today and discover how advanced security solutions can protect your infrastructure.
FAQs: Kubernetes Security Risks and Mitigation
1. What are the biggest Kubernetes security risks?
Misconfigurations, weak access controls, insecure images, and lack of monitoring are the most common risks.
2. How can I secure Kubernetes clusters?
Use RBAC, network policies, secure configurations, and continuous monitoring tools.
3. What is Kubernetes RBAC?
RBAC controls who can access and perform actions within a Kubernetes cluster.
4. Why is container security important in Kubernetes?
Containers run applications, so vulnerabilities in them can lead to breaches.
5. How often should Kubernetes security be reviewed?
Regularly—at least quarterly or after major updates.