CSPM vs CWPP vs CIEM Explained: A Complete Guide for Cloud Security Leaders
Updated on March 26, 2026, by Xcitium
Cloud security is getting more complex every year. With businesses rapidly moving workloads to the cloud, security teams face a critical question: how do you protect cloud environments effectively?
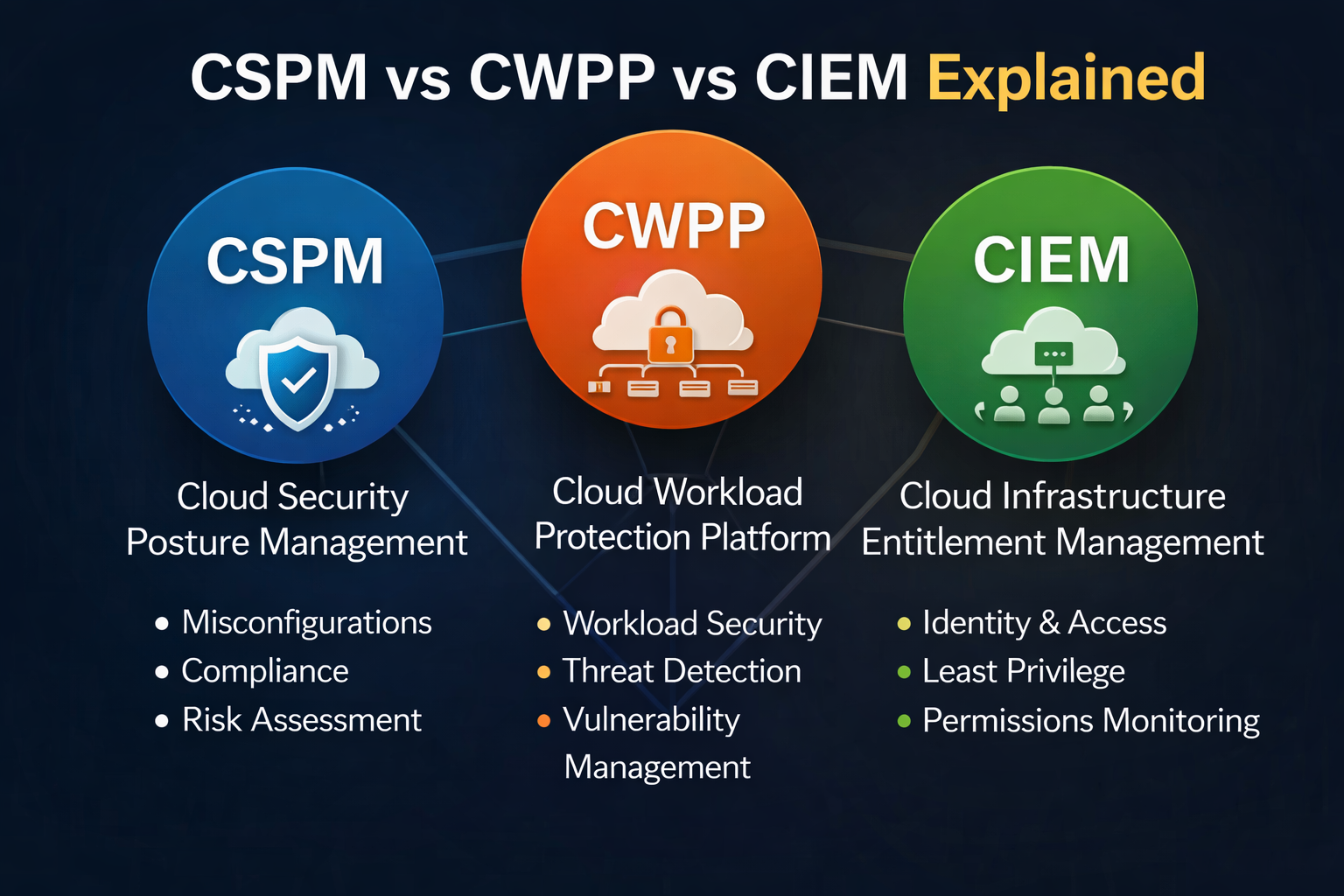
That’s where understanding CSPM vs CWPP vs CIEM explained becomes essential. These three security solutions play different roles in protecting cloud infrastructure, workloads, and identities. But many IT leaders and security teams still struggle to differentiate them.
In this guide, we’ll break everything down in simple terms so you can choose the right approach for your organization.
What Is CSPM, CWPP, and CIEM? (Quick Overview)
Before diving deeper into CSPM vs CWPP vs CIEM explained, let’s define each term clearly:
- CSPM (Cloud Security Posture Management): Focuses on identifying misconfigurations and compliance risks in cloud environments.
- CWPP (Cloud Workload Protection Platform): Secures workloads like VMs, containers, and serverless applications.
- CIEM (Cloud Infrastructure Entitlement Management): Manages identity permissions and access controls in cloud environments.
Each tool solves a different problem—but together, they create a strong cloud security strategy.
Why Understanding CSPM vs CWPP vs CIEM Matters
Cloud environments are not just about infrastructure anymore—they include workloads, APIs, identities, and data.
Without a clear understanding of CSPM vs CWPP vs CIEM explained, organizations risk:
- Misconfigured cloud resources
- Over-permissioned user access
- Vulnerable workloads
- Compliance failures
- Increased attack surface
Modern cyber threats often exploit these exact gaps. That’s why choosing the right mix of tools is critical.
CSPM Explained: Securing Cloud Configurations
CSPM tools continuously monitor cloud environments for misconfigurations and compliance issues.
Key Features of CSPM
- Detects misconfigured storage buckets, databases, and networks
- Ensures compliance with standards (GDPR, HIPAA, PCI-DSS)
- Provides automated remediation
- Offers visibility across multi-cloud environments
When to Use CSPM
Use CSPM if your organization:
- Runs workloads on AWS, Azure, or GCP
- Needs compliance reporting
- Wants to reduce configuration-related risks
Example
An open S3 bucket exposing sensitive data? CSPM detects and fixes it quickly.
CWPP Explained: Protecting Cloud Workloads
CWPP focuses on securing workloads regardless of where they run—cloud, hybrid, or on-premises.
Key Features of CWPP
- Runtime protection for workloads
- Vulnerability management
- Malware detection and prevention
- Container and Kubernetes security
When to Use CWPP
CWPP is ideal if:
- You use containers or microservices
- You need runtime threat detection
- You want workload-level visibility
Example
If malware infects a container, CWPP detects and blocks it in real time.
CIEM Explained: Managing Cloud Identities and Permissions
CIEM solutions focus on identity and access management in cloud environments.
Key Features of CIEM
- Detects excessive permissions
- Enforces least privilege access
- Monitors identity-related risks
- Provides visibility into user roles and access
When to Use CIEM
Use CIEM if:
- You manage multiple users and roles in the cloud
- You want to prevent insider threats
- You need better control over access policies
Example
A developer accidentally gets admin access? CIEM flags and removes it.
CSPM vs CWPP vs CIEM Explained: Key Differences
Understanding the differences is crucial for building a complete security strategy.
| Feature | CSPM | CWPP | CIEM |
|---|---|---|---|
| Focus Area | Configuration | Workloads | Identity & Access |
| Security Layer | Infrastructure | Runtime | Permissions |
| Main Risk Addressed | Misconfigurations | Malware & vulnerabilities | Over-permissioned access |
| Use Case | Compliance & visibility | Threat detection | Access control |
In Simple Terms:
- CSPM = “Is your cloud configured securely?”
- CWPP = “Are your workloads protected?”
- CIEM = “Who has access—and should they?”
How These Tools Work Together
Instead of choosing one, modern organizations combine all three.
Integrated Cloud Security Approach
- CSPM identifies risks in configurations
- CWPP protects workloads in real time
- CIEM controls access and permissions
Together, they provide:
- End-to-end visibility
- Reduced attack surface
- Strong compliance posture
Best Practices for Implementing CSPM, CWPP, and CIEM
To get the most value from your cloud security strategy:
1. Adopt a Layered Security Approach
Don’t rely on a single tool—combine CSPM, CWPP, and CIEM.
2. Enforce Least Privilege Access
Limit user permissions to only what’s necessary.
3. Automate Security Monitoring
Use tools that provide real-time alerts and remediation.
4. Continuously Audit Configurations
Cloud environments change rapidly—monitor them constantly.
5. Integrate with DevSecOps
Shift security left by embedding it into development pipelines.
Common Challenges Organizations Face
Even with the right tools, challenges remain:
- Tool overlap and confusion
- Lack of skilled security professionals
- Alert fatigue
- Integration complexity
Understanding CSPM vs CWPP vs CIEM explained helps reduce these issues and build a more efficient strategy.
Future of Cloud Security: Convergence Is Key
The future is moving toward CNAPP (Cloud-Native Application Protection Platform)—a unified solution combining:
- CSPM
- CWPP
- CIEM
This approach simplifies security management and improves visibility across cloud environments.
Conclusion: Choosing the Right Cloud Security Strategy
By now, CSPM vs CWPP vs CIEM explained should be clear. Each plays a unique role in securing modern cloud environments.
- CSPM protects configurations
- CWPP secures workloads
- CIEM manages access
The best approach isn’t choosing one—it’s integrating all three.
👉 Want to strengthen your cloud security strategy?
Request a demo today and see how advanced solutions can protect your business from evolving cyber threats.
FAQs: CSPM vs CWPP vs CIEM Explained
1. What is the main difference between CSPM, CWPP, and CIEM?
CSPM focuses on configurations, CWPP protects workloads, and CIEM manages access and permissions.
2. Do I need all three tools for cloud security?
Yes, for complete protection. Each tool addresses a different layer of cloud security.
3. What is CNAPP?
CNAPP is a unified platform that combines CSPM, CWPP, and CIEM into one solution.
4. Which tool helps with compliance?
CSPM is primarily used for compliance monitoring and reporting.
5. How does CIEM improve security?
CIEM reduces risks by enforcing least privilege access and preventing excessive permissions.