What Is the SAAP Model? A Complete Guide for Modern Cybersecurity
Updated on December 19, 2025, by Xcitium
Cyber threats are no longer simple, isolated events. They are persistent, adaptive, and designed to bypass traditional defenses. This reality has pushed organizations to rethink how they approach security. If you’re asking what is the SAAP model, you’re already thinking in the right direction.
The SAAP model is gaining attention in cybersecurity because it focuses on structured prevention, intelligent analysis, and proactive protection—not just reacting after a breach occurs. In this guide, we’ll break down what the SAAP model is, how it works, and why it matters for organizations of all sizes.
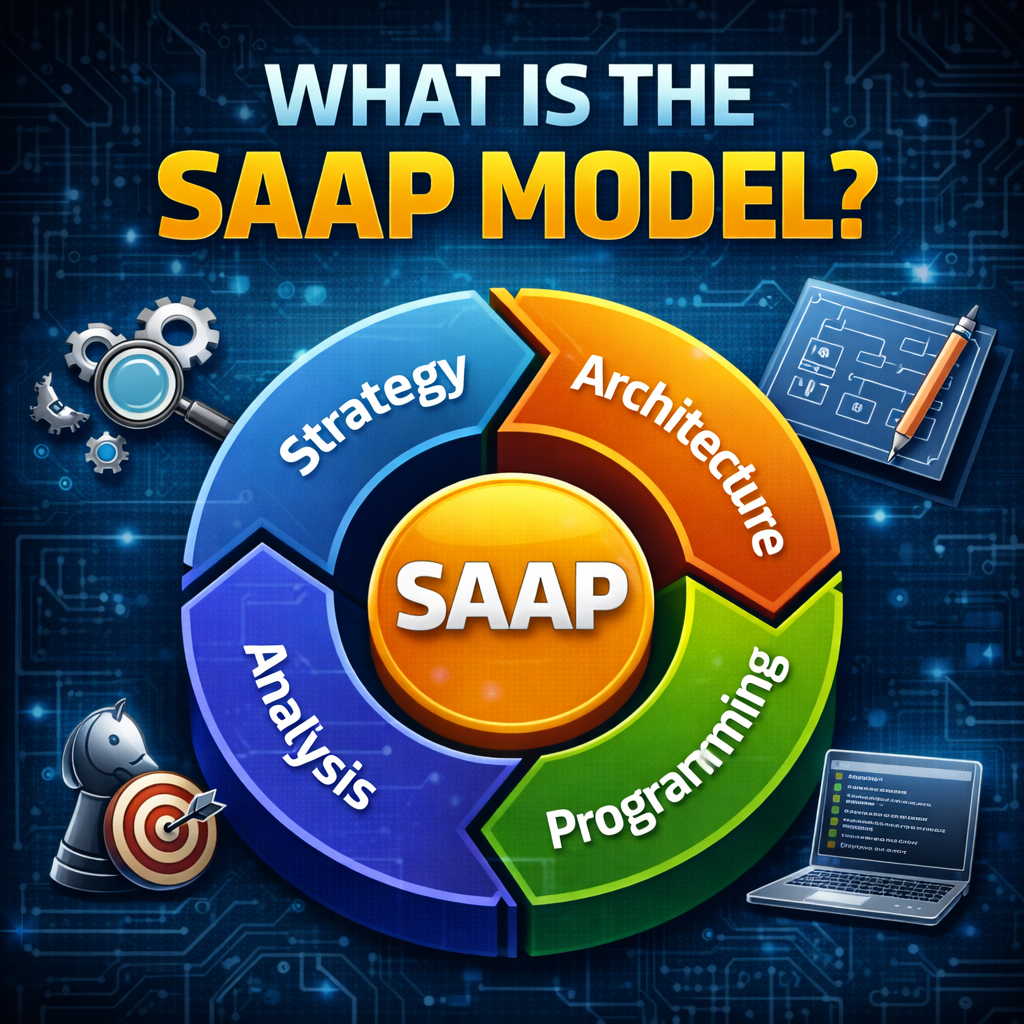
What Is the SAAP Model?
The SAAP model is a cybersecurity framework built around four core principles:
S – Secure
A – Analyze
A – Act
P – Protect
At its core, the SAAP model is designed to continuously secure systems, analyze behavior, take action against threats, and protect assets from both known and unknown attacks.
When people ask what is the SAAP model, the simplest explanation is this:
It’s a proactive security approach that assumes threats will happen and focuses on stopping damage before it spreads.
Why the SAAP Model Matters in Today’s Threat Landscape
Cybersecurity has changed dramatically over the last decade. Traditional perimeter-based security models no longer work in environments that rely on cloud services, remote work, and mobile devices.
Here’s why the SAAP model is relevant today:
-
Attacks bypass signature-based tools
-
Zero-day threats are increasingly common
-
Credential theft enables lateral movement
-
Dwell time is the biggest risk factor
The SAAP model addresses these challenges by focusing on continuous control instead of reactive cleanup.
Breaking Down the SAAP Model Components
To truly understand what the SAAP model is, let’s examine each component in detail.
1. Secure: Building a Strong Foundation
The first pillar of the SAAP model is Secure.
This step focuses on:
-
Hardening systems and configurations
-
Reducing the attack surface
-
Enforcing access controls
-
Establishing baseline security policies
Security begins before an attack ever happens. By securing endpoints, networks, and cloud resources, organizations reduce the number of opportunities attackers can exploit.
In the SAAP model, security is not a one-time setup—it’s an ongoing process.
2. Analyze: Understanding Behavior, Not Just Signatures
The second pillar, Analyze, is where the SAAP model truly stands out.
Rather than relying solely on known malware signatures, the SAAP model emphasizes:
-
Behavioral analysis
-
Anomaly detection
-
Context-aware monitoring
This allows security teams to identify suspicious activity even when no known signature exists. When asking what is the SAAP model, this analysis phase is critical—it shifts security from reactive to intelligent.
3. Act: Responding in Real Time
Once a potential threat is detected, the SAAP model moves to Act.
This includes:
-
Automated response
-
Threat isolation
-
Containment of suspicious processes
-
Blocking malicious activity immediately
Speed matters. The SAAP model minimizes dwell time by acting as soon as suspicious behavior is detected—often before human intervention is required.
4. Protect: Preventing Damage and Spread
The final pillar is Protect.
Protection in the SAAP model goes beyond simple blocking. It focuses on:
-
Preventing lateral movement
-
Safeguarding data and applications
-
Ensuring business continuity
Even if a threat executes, the SAAP model ensures it cannot cause damage or spread across the environment.
How the SAAP Model Differs from Traditional Security Models
To better understand what the SAAP model is, it helps to compare it with older approaches.
Traditional Security Models
-
Rely on perimeter defenses
-
Focus on known threats
-
React after compromise
-
Depend heavily on alerts
SAAP Model
-
Assumes threats will bypass defenses
-
Analyzes behavior continuously
-
Acts automatically
-
Protects assets even from unknown threats
This shift makes the SAAP model far more effective against modern attacks.
Key Benefits of the SAAP Model
Organizations adopting the SAAP model experience several advantages.
Reduced Breach Impact
Threats are contained before they can spread.
Improved Visibility
Continuous analysis provides deep insight into system behavior.
Faster Response
Automated actions eliminate delays.
Stronger Zero Trust Alignment
The SAAP model naturally aligns with Zero Trust principles.
SAAP Model and Zero Trust Security
Zero Trust operates on the idea of “never trust, always verify.” The SAAP model complements this philosophy perfectly.
In practice, the SAAP model:
-
Treats unknown processes as untrusted
-
Monitors behavior continuously
-
Limits privileges by default
-
Contains threats automatically
This combination significantly reduces risk in complex environments.
How the SAAP Model Supports Endpoint Security
Endpoints are often the entry point for attacks. The SAAP model strengthens endpoint security by:
-
Preventing execution of unknown or suspicious files
-
Monitoring process behavior in real time
-
Isolating threats instantly
-
Protecting endpoints without relying solely on detection
This makes the SAAP model especially valuable for remote and hybrid workforces.
Use Cases for the SAAP Model
The SAAP model is versatile and applies across industries.
Enterprise IT
Protects endpoints, servers, and cloud workloads.
Healthcare
Safeguards sensitive patient data and meets compliance requirements.
Financial Services
Prevents fraud, credential abuse, and ransomware.
Manufacturing
Secures operational technology and connected systems.
Common Misconceptions About the SAAP Model
Let’s clear up a few myths.
Myth: The SAAP model replaces antivirus
Reality: It enhances and modernizes endpoint protection.
Myth: It’s only for large enterprises
Reality: Small and mid-sized organizations benefit significantly.
Myth: Automation removes human oversight
Reality: Automation supports analysts—it doesn’t replace them.
How to Implement the SAAP Model Effectively
Successful adoption requires more than tools.
Best Practices
-
Start with endpoint visibility
-
Integrate behavioral monitoring
-
Automate response actions
-
Align with Zero Trust principles
-
Continuously refine policies
The SAAP model works best when security is treated as an ongoing strategy, not a product.
Why IT Managers and Executives Should Care
For leaders, understanding what the SAAP model is goes beyond technical interest.
The SAAP model:
-
Reduces operational risk
-
Improves incident response times
-
Protects business continuity
-
Supports compliance and governance
In today’s threat environment, proactive security is a business necessity.
The Future of the SAAP Model
As threats evolve, the SAAP model continues to grow in relevance.
Future advancements include:
-
AI-driven behavioral analysis
-
Deeper automation
-
Integration with XDR platforms
-
Cloud-native security controls
Organizations that adopt the SAAP model early gain a long-term security advantage.
Final Thoughts
So, what is the SAAP model? It’s a modern cybersecurity framework designed to secure systems, analyze behavior, act against threats, and protect assets—continuously and proactively.
In an era where unknown threats are the norm, the SAAP model provides a smarter, more resilient approach to security that aligns with Zero Trust and modern endpoint protection strategies.
Take the Next Step Toward Proactive Security
If you’re ready to move beyond reactive security and adopt a proactive, Zero Trust–aligned approach, modern platforms built on SAAP principles can help.
👉 Request a demo today:
https://www.xcitium.com/request-demo/
Frequently Asked Questions (FAQ)
1. What is the SAAP model in cybersecurity?
It’s a security framework focused on Secure, Analyze, Act, and Protect to stop threats proactively.
2. How does the SAAP model differ from traditional security?
It emphasizes behavior analysis and containment rather than reactive detection.
3. Is the SAAP model suitable for small businesses?
Yes. It scales well and reduces the need for large security teams.
4. Does the SAAP model replace antivirus software?
No. It enhances protection by addressing unknown and advanced threats.
5. Is the SAAP model aligned with Zero Trust?
Yes. It naturally supports Zero Trust security principles.