Software Supply Chain Security Guide
Updated on March 4, 2026, by Xcitium
Software powers nearly every modern business. From cloud platforms to mobile apps and enterprise systems, organizations depend heavily on software to run operations and deliver services. But here’s a growing concern: attackers are no longer targeting just networks or endpoints—they’re targeting the software supply chain itself.
In recent years, high-profile incidents like the SolarWinds breach exposed how a single compromised component can impact thousands of organizations. According to cybersecurity reports, supply chain attacks increased dramatically as threat actors realized they could compromise many companies through one entry point.
This Software Supply Chain Security Guide explains what software supply chain security is, why it matters, and how organizations can secure their development pipelines, dependencies, and infrastructure against modern threats.
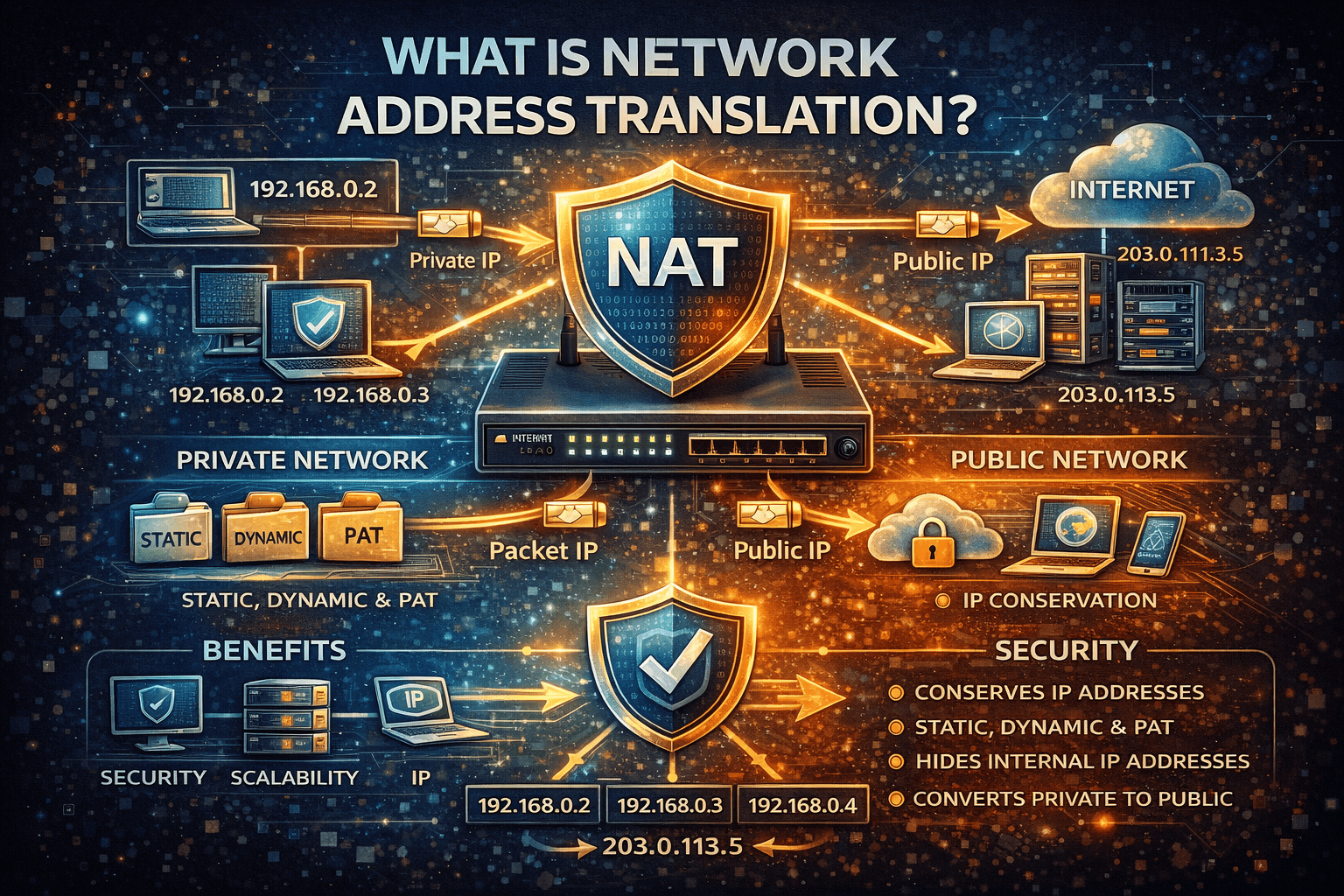
What Is Software Supply Chain Security?
Software supply chain security refers to the practices, technologies, and processes used to protect software throughout its entire lifecycle—from development and third-party dependencies to deployment and updates.
The software supply chain includes multiple components such as:
-
Source code repositories
-
Third-party libraries and dependencies
-
Development tools and CI/CD pipelines
-
Package managers
-
Build systems
-
Deployment environments
Because modern applications rely heavily on open-source components and external services, securing every stage of the supply chain has become critical.
Why Software Supply Chain Security Matters
Modern software development rarely happens in isolation. Developers rely on open-source packages, cloud infrastructure, container images, and automation tools.
While this accelerates development, it also increases risk.
Key Risks in the Software Supply Chain
-
Compromised open-source dependencies
-
Malicious code injection
-
Vulnerable libraries
-
Tampered build pipelines
-
Unauthorized access to code repositories
A single vulnerability in the supply chain can cascade across multiple organizations.
Real-World Impact
Supply chain attacks can lead to:
-
Data breaches
-
Service disruptions
-
Intellectual property theft
-
Financial losses
-
Reputational damage
For IT leaders and cybersecurity teams, supply chain security has become a top priority.
Understanding the Software Supply Chain Lifecycle
To secure the supply chain effectively, organizations must understand each stage of the lifecycle.
Source Code Development
The first stage of the supply chain is where developers write and maintain code.
Security Best Practices for Source Code
-
Use secure coding practices
-
Implement code reviews
-
Scan for vulnerabilities early
-
Enforce access controls in repositories
Tools like static application security testing (SAST) can help identify vulnerabilities during development.
Dependency Management
Modern applications often depend on hundreds of third-party libraries.
Risks of Third-Party Dependencies
-
Outdated packages with known vulnerabilities
-
Malicious packages uploaded to repositories
-
Hidden backdoors in open-source code
Dependency management tools and software composition analysis (SCA) can identify vulnerable packages.
Build and Integration
Continuous integration (CI) pipelines automatically build and test software.
Securing CI/CD Pipelines
A compromised pipeline can inject malicious code into software releases.
Key protections include:
-
Secure access controls
-
Signed builds
-
Secrets management
-
Pipeline monitoring
Protecting CI/CD infrastructure is essential for maintaining supply chain integrity.
Software Distribution
Once software is built, it must be distributed to users or internal systems.
Risks During Distribution
-
Package tampering
-
Malware injection
-
Unauthorized updates
Using cryptographic signing ensures users receive authentic software packages.
Deployment and Runtime
Even after deployment, software must be monitored continuously.
Runtime Security Measures
-
Container security monitoring
-
Runtime application self-protection (RASP)
-
Vulnerability patch management
Security does not end after deployment. Continuous monitoring ensures long-term protection.
Common Software Supply Chain Attacks
Understanding attack techniques helps organizations prepare better defenses.
Dependency Confusion Attacks
Attackers publish malicious packages with the same name as internal libraries.
If a system downloads the malicious package first, the attacker gains control.
Compromised Open-Source Libraries
Hackers may insert malicious code into open-source projects that developers trust.
Once included in applications, the malicious code spreads to every deployment.
CI/CD Pipeline Attacks
If attackers gain access to build systems, they can inject malicious code directly into releases.
This technique was used in several high-profile cyber incidents.
Package Repository Attacks
Attackers sometimes compromise software repositories to distribute malware through legitimate channels.
Key Components of Software Supply Chain Security
To protect the supply chain effectively, organizations must implement multiple security layers.
Software Bill of Materials (SBOM)
An SBOM lists every component used in a software product.
Benefits of SBOM
-
Transparency into dependencies
-
Faster vulnerability identification
-
Improved compliance tracking
SBOMs are becoming essential for modern software security programs.
Code Integrity Verification
Ensuring that code remains unchanged from development to deployment is critical.
Techniques for Code Integrity
-
Digital signatures
-
Hash verification
-
Immutable build artifacts
These mechanisms prevent unauthorized modifications.
Continuous Vulnerability Scanning
Security scanning tools help identify weaknesses before attackers exploit them.
Common tools include:
-
SAST (Static Analysis)
-
DAST (Dynamic Analysis)
-
SCA (Software Composition Analysis)
Continuous scanning ensures vulnerabilities are detected early.
Access Control and Identity Management
Supply chain security also depends on strong identity controls.
Best Practices
-
Use multi-factor authentication
-
Restrict developer privileges
-
Monitor access logs
-
Implement least-privilege access
Identity-based attacks are common entry points for supply chain compromises.
Best Practices for Software Supply Chain Security
Organizations can significantly reduce risk by following proven security practices.
Implement DevSecOps
Integrate security directly into the development lifecycle.
Security should be automated and embedded within CI/CD pipelines.
Monitor Third-Party Components
Regularly review and update dependencies.
Use automated tools to track vulnerabilities in external libraries.
Secure Build Infrastructure
Protect CI/CD environments using:
-
Network segmentation
-
Access restrictions
-
Secrets management systems
Maintain Visibility Across the Supply Chain
Organizations should maintain full visibility across:
-
Source code repositories
-
Build pipelines
-
Dependencies
-
Deployment environments
Security monitoring helps detect suspicious activity early.
Industry Regulations and Compliance
Regulatory frameworks increasingly require software supply chain transparency.
Examples include:
-
NIST Secure Software Development Framework (SSDF)
-
Executive Order on Improving Cybersecurity (U.S.)
-
ISO/IEC 27001
-
SOC 2 security standards
Compliance frameworks emphasize secure software development practices.
Emerging Trends in Supply Chain Security
Software supply chain security continues to evolve.
Key trends include:
-
AI-driven vulnerability detection
-
Automated SBOM generation
-
Zero Trust development environments
-
Secure container registries
-
Cloud-native supply chain protection
Organizations adopting these practices gain stronger resilience against advanced threats.
Challenges in Securing the Software Supply Chain
Despite improvements, organizations still face several challenges.
Complexity
Modern applications may contain thousands of dependencies.
Visibility Gaps
Without proper tools, tracking every component becomes difficult.
Rapid Development Cycles
Continuous releases make manual security reviews impractical.
Automation and security integration help address these challenges.
The Role of Security Platforms in Supply Chain Protection
Advanced cybersecurity platforms help organizations monitor and protect their entire supply chain.
These platforms provide:
-
Threat detection
-
Vulnerability management
-
Endpoint protection
-
Incident response capabilities
Unified security solutions strengthen overall resilience.
Frequently Asked Questions (FAQ)
1. What is software supply chain security?
Software supply chain security protects every stage of software development, including code, dependencies, build pipelines, and deployment systems.
2. Why are supply chain attacks increasing?
Attackers target supply chains because compromising one component can affect many organizations simultaneously.
3. What is a Software Bill of Materials (SBOM)?
An SBOM is a detailed inventory of all components used in a software product, helping organizations track vulnerabilities.
4. How can organizations secure third-party dependencies?
By using software composition analysis tools, updating libraries regularly, and verifying package authenticity.
5. Is supply chain security only relevant for large enterprises?
No. Any organization developing or using software can be affected by supply chain vulnerabilities.
Final Thoughts: Strengthening Software Supply Chain Security
Software supply chain attacks are becoming one of the most serious cybersecurity threats facing organizations today. As development environments grow more complex and interconnected, security must extend beyond traditional defenses.
By implementing strong software supply chain security practices—such as SBOM tracking, dependency monitoring, secure pipelines, and continuous vulnerability scanning—organizations can significantly reduce risk.
Cybersecurity is no longer just about protecting networks; it’s about securing every component that builds your software.
If you want to strengthen your security posture and protect your organization against evolving cyber threats, take the next step today.
👉 Request a demo:
https://www.xcitium.com/request-demo/
Discover how advanced cybersecurity solutions can help secure your infrastructure, endpoints, and software supply chain.