- December 22, 2025
- 6 mins
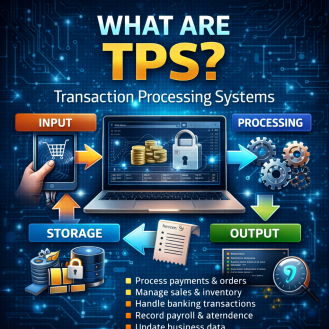
In today’s always-on digital economy, businesses process thousands—or even millions—of...
- December 19, 2025
- 7 mins
Cyber threats are no longer simple, isolated events. They are persistent, adaptive, and designed to...
- December 19, 2025
- 7 mins
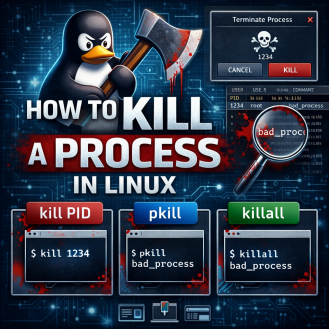
Ever had a Linux application freeze, spike CPU usage, or refuse to close? Whether you’re...

- December 18, 2025
- 5 mins
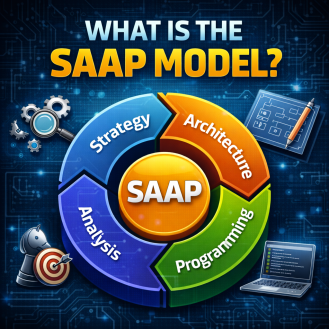
Modern IT environments are under constant pressure to be faster, simpler, and more secure....
- December 18, 2025
- 6 mins
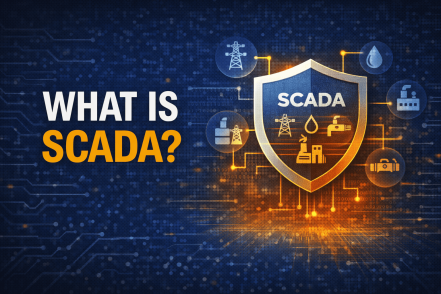
Power grids, water treatment plants, manufacturing lines, oil pipelines, and transportation systems...
- December 17, 2025
- 6 mins
Cyberattacks today are faster, stealthier, and more coordinated than ever before. Threat actors no...

- December 17, 2025
- 6 mins
Forgot your Wi-Fi password right when you need it most? You’re not alone. Whether you’re...
- December 16, 2025
- 6 mins
As cyber threats grow more advanced, organizations need security that starts at the very foundation...

- December 16, 2025
- 6 mins
Have you ever seen someone’s private address, phone number, or employer exposed online during an...








