What Is a Subnet? Understanding Network Segmentation Clearly
Updated on August 8, 2025, by Xcitium
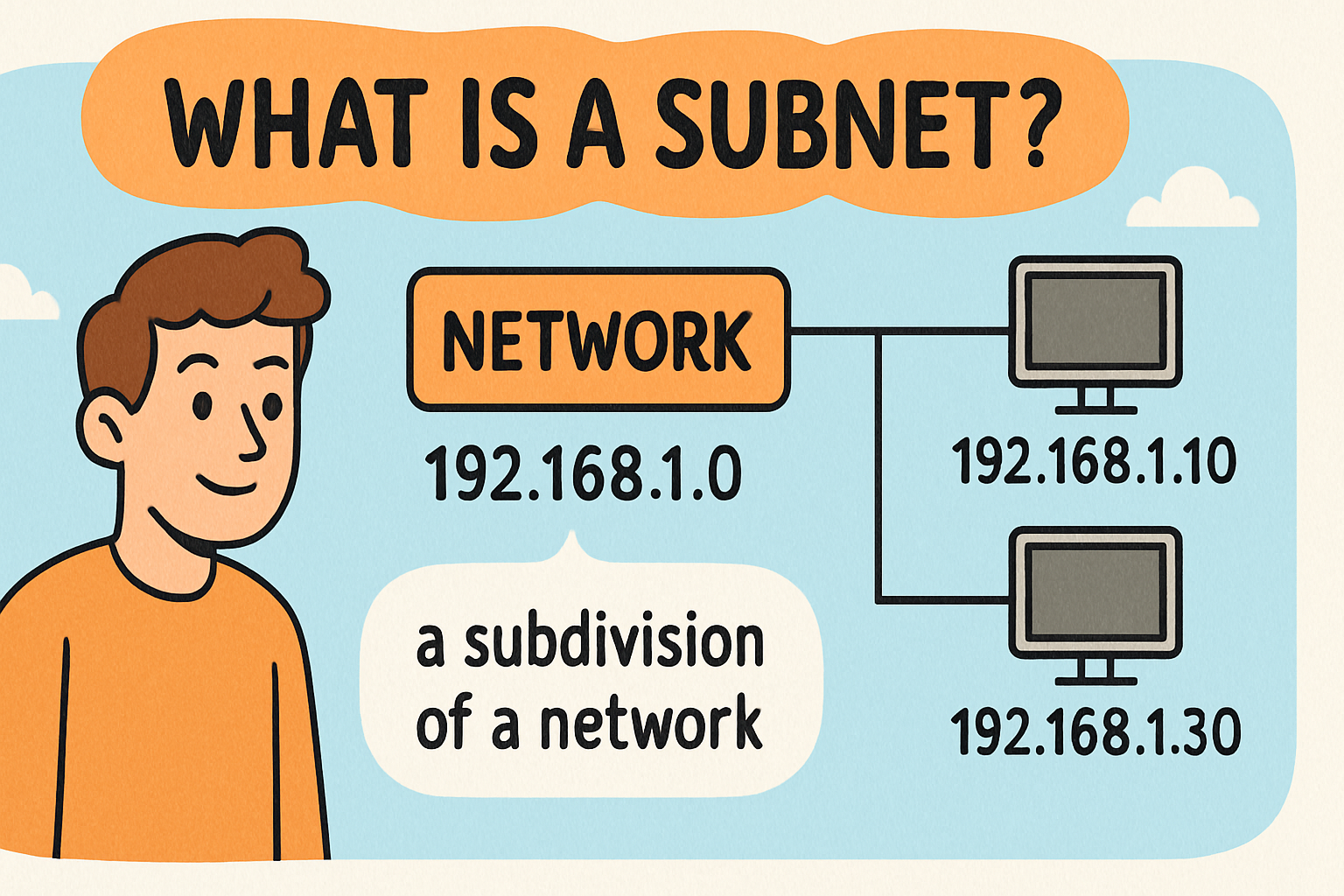
Ever wondered what is a subnet and why companies split their networks into sub-networks? A subnet—short for subnetwork—is a logical division of an IP network. Each subnet operates as its own segment, improving performance, managing traffic better, and enhancing security.
Whether you’re an IT manager struggling with network growth or a cybersecurity lead implementing segmentation policies, this guide walks you through the what, how, why, and security advantages of subnetting.
What Is a Subnet?
A subnet, or subnetwork, is a subdivision of a larger IP network. It’s created by dividing a parent IP address block into smaller, logical segments. Devices within the same subnet share a common network prefix and can communicate directly. Communication across subnets requires routing via a router or Layer 3 switch.
Subnetting helps administrators group devices—such as by department or location—while reducing congestion and improving network control.
Why Subnet? Benefits of Subnetting Explained
Subnetting offers advantages for performance, security, and administration:
- Improved performance: Smaller broadcast domains reduce unnecessary network traffic.
- Better security: Isolate departments or IoT devices into separate subnets with tailored firewall rules.
- Efficient IP usage: With CIDR and variable prefixes, you avoid wasted IPs.
- Simplified network troubleshooting and management by sectioning off manageable segments.
Subnet Masks & CIDR Notation
What Is a Subnet Mask?
A subnet mask is a 32‑bit binary number that divides an IP address into network and host parts. Leading bits (1) indicate the network portion, and trailing bits (0) indicate hosts
For instance, 255.255.255.0 is a common mask for a /24 network.
CIDR Notation
Classless Inter-Domain Routing (CIDR) enables flexible subnetting using slash notation. For example, 192.168.1.0/24 indicates that the first 24 bits define the network.
CIDR allows aggregation into supernets like /23, reducing the number of routing entries needed.
Real‑World Examples & Use Cases
Example: Splitting a Class C Network
A /24 network such as 192.168.1.0/24 with a mask of 255.255.255.0 gives 254 usable IPs. Splitting into two /25 subnets (mask 255.255.255.128) creates two segments each supporting up to 126 hosts.
Use Case: Departmental Segmentation
A company may assign:
- 192.168.10.0/25 – HR team
- 192.168.10.128/25 – Engineering
Traffic stays segmented; cross-subnet access passes through controlled firewalls.
Use Case: IoT Device Isolation
Placing IoT within 10.0.0.0/24 and user devices into a separate subnet prevents lateral movement if IoT is compromised.
Subnet Calculations: How Hosts & Subnets Are Derived
- Host count per subnet is 2^h – 2 (reserving network and broadcast addresses).
- Increasing prefix length reduces hosts per subnet but increases granularity.
- Example: /26 mask (255.255.255.192) yields 62 usable hosts.
Differences: Subnet vs Subnet Mask vs CIDR Prefix
| Term | Description | Example |
| Subnet | Logical subdivision within an IP network | 192.168.2.0/24 |
| Subnet Mask | Binary mask separating network and host bits | 255.255.255.0 |
| CIDR Prefix | Number of network bits in mask | /24 |
Subnetting and Cybersecurity
From a cybersecurity perspective, subnetting is more than traffic control:
- Enables zero-trust access: define policies per subnet.
- Limits spread of malware between subnets.
- Supports network monitoring and segmentation.
- Helps meet compliance requirements (e.g., isolating PCI data).
Best Practices for Network Design
- Use CIDR notation for clarity (/25, /26, etc.)
- Avoid using classful assumptions (A/B/C).
- Reserve separate subnets for guest, production, IoT, and management segments.
- Use VLSM to maximize address usage.
- Document subnet assignments, masks, and gateways.
- Implement inter-subnet firewall rules and ACLs.
FAQs
Q1: Can devices in different subnets communicate without routing?
No—cross-subnet communication requires a router or Layer 3 switch.
Q2: What is the difference between VLSM and traditional subnetting?
VLSM allows variable-length subnet masks, enabling finer segmentation than fixed classful masks.
Q3: How many subnets can /24 support if split into /26?
A /24 divided into /26 yields 4 subnets. Each supports up to 62 hosts (4 × 62 = 248).
Q4: Why reserve the network and broadcast addresses?
They identify the subnet and enable sending to all devices in that subnet. Hosts shouldn’t use them.
Q5: Does IPv6 use subnetting?
Yes, but IPv6 standard subnet size is /64 due to its 128‑bit address space.
Final Thoughts
Understanding what is a subnet and how subnetting works is foundational for secure, efficient network architecture. Subnetting enables better performance, tighter security, and optimized IP use. Whether you’re IT leadership or a network admin, mastering this concept is essential in modern cloud-connected infrastructures.
🚀 Call to Action
Looking to strengthen network segmentation, simplify security policies, and get granular visibility across subnets?
👉 Request a Free Demo from Xcitium to explore automated segmentation, network monitoring, and policy enforcement tools.