What Is Hashing? A Beginner-Friendly Guide to Digital Fingerprinting
Updated on June 20, 2025, by Xcitium
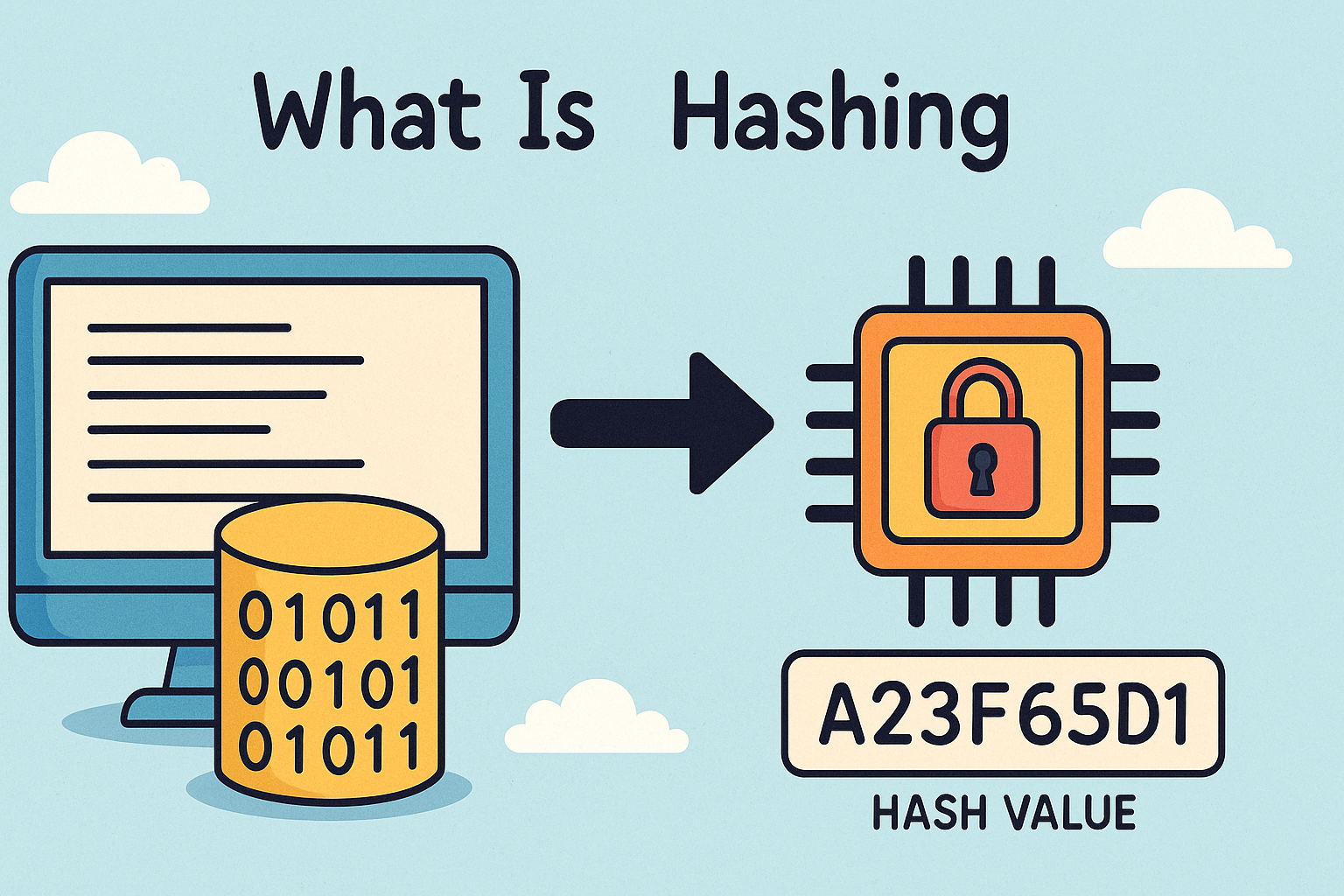
What is hashing, and why does it matter in cybersecurity and IT infrastructure? In an age where data security and integrity are paramount, hashing plays a foundational role in everything from password protection to blockchain verification. While it might sound complex, hashing is simply a way of converting data into a fixed-size string that acts like a digital fingerprint.
In this guide, you’ll learn the hashing meaning, how it compares to encryption, key hashing algorithms, and how businesses use hashing to secure data.
What Is Hashing?
Hashing is the process of converting any input (such as text, files, or passwords) into a fixed-length value, usually a string of numbers and letters. This value is called a hash or hash value. It is generated using a specific hashing function.
Hashing Meaning:
In simple terms, hashing is a one-way function that transforms data into a code—making it easy to verify but nearly impossible to reverse-engineer.
Definition of Hashing (Technical):
Hashing is a mathematical process that maps data of arbitrary size to a fixed-size output using a deterministic algorithm.
Why Is Hashing Important?
Hashing helps protect and verify data in various applications:
- Password storage: Ensures user credentials are stored securely
- File integrity checks: Confirms a file hasn’t been tampered with
- Digital signatures: Supports secure authentication in messaging and transactions
- Blockchain: Creates links between blocks of data for tamper-proof ledgers
How Does a Hashing Function Work?
A hashing function takes an input (or “message”) and produces a fixed-size output called a hash.
Key Characteristics:
- Deterministic: Same input always produces the same output
- Fast computation
- Pre-image resistance: Hard to derive original input from hash
- Collision resistance: Unlikely for two inputs to produce the same hash
- Avalanche effect: Small changes in input drastically change the output
Example:
Input: hello → Output (SHA-256): 2cf24dba5fb0a…
Even changing one letter changes the hash completely.
Popular Hashing Algorithms
1. MD5 (Message Digest Algorithm 5)
- Produces a 128-bit hash
- Considered obsolete due to collision vulnerabilities
2. SHA-1 (Secure Hash Algorithm 1)
- Produces a 160-bit hash
- Also deprecated due to security flaws
3. SHA-256 (Part of SHA-2)
- Widely used in blockchain, SSL certificates
- Strong cryptographic strength
4. SHA-3
- Designed as a stronger alternative to SHA-2
- Uses a completely different construction method (Keccak)
5. Bcrypt, Scrypt, Argon2
- Specifically designed for secure password hashing
- Slow by design to resist brute-force attacks
Hashing vs Encryption: What’s the Difference?
While both are essential for data security, they serve different purposes.
| Feature | Hashing | Encryption |
| Purpose | Data integrity/verification | Data confidentiality |
| Reversible? | No (one-way) | Yes (two-way) |
| Output Length | Fixed | Variable (depends on key) |
| Key Required | No | Yes (symmetric/asymmetric key) |
| Use Cases | Passwords, file verification | Messages, emails, file encryption |
Where Is Hashing Used in Cybersecurity?
1. Password Storage
- Passwords are hashed and stored in databases
- Even if leaked, original passwords remain hidden
2. Digital Signatures
- Hashes are signed using a private key
- Receivers verify with the sender’s public key
3. Blockchain Technology
- Every block includes a hash of the previous one
- Ensures immutability of data
4. File Integrity Verification
- Common in software downloads (e.g., “Verify with SHA-256 checksum”)
- Confirms no file tampering during transfer
Common Hashing Mistakes to Avoid
- Storing plain-text passwords
- Using outdated algorithms like MD5 or SHA-1
- Not using salt with password hashes (makes it easier to crack with rainbow tables)
- Rehashing already hashed values, which doesn’t enhance security
Best Practices for Secure Hashing
- Use strong, modern algorithms (e.g., SHA-256, Argon2)
- Apply a salt—random data added to the input to create unique hashes
- Limit access to hashed data
- Avoid using hash functions for encryption tasks
- Regularly review and update hashing policies
Real-World Examples
- LinkedIn Data Breach (2012): Hackers stole millions of user credentials hashed with SHA-1, which was eventually cracked
- Blockchain: Every Bitcoin transaction is validated with hashing
- Software Downloads: Many Linux distributions provide SHA-256 hashes for verification
FAQs About Hashing
1. What is hashing in cybersecurity?
Hashing is the process of transforming data into a fixed-size hash to verify integrity and protect sensitive information like passwords.
2. Is hashing secure?
Yes, if modern and secure algorithms like SHA-256 or Argon2 are used with proper implementation.
3. What’s the difference between hashing and encryption?
Hashing is one-way and used for verification; encryption is reversible and used for securing data in transit or storage.
4. Can you reverse a hash?
No, secure hash functions are designed to be irreversible.
5. Which hashing algorithm is best?
For passwords: Argon2 or Bcrypt. For general data integrity: SHA-256 or SHA-3.
Final Thoughts: Why Every IT Leader Should Understand Hashing
Knowing what is hashing isn’t just for cryptographers—it’s essential knowledge for IT managers, developers, and cybersecurity professionals. From verifying data integrity to safeguarding passwords, hashing ensures the backbone of trust in modern computing systems.
Want to protect your infrastructure with advanced security practices? Request a demo from Xcitium today.