
- March 25, 2026
- 5 mins
What if your organization has hidden security gaps you don’t even know about? That’s exactly...

- March 24, 2026
- 5 mins
Is your organization using Remote Desktop for remote access? If so, you must understand the growing...
- March 24, 2026
- 5 mins
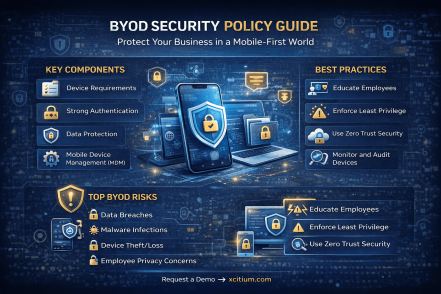
Is your organization allowing employees to use personal devices for work? If yes, then having a...

- March 24, 2026
- 5 mins
Security Operations Centers (SOCs) are the backbone of modern cybersecurity. But what happens when...

- March 23, 2026
- 5 mins
What if your biggest cybersecurity risk isn’t your technology—but your people? Despite advanced...

- March 23, 2026
- 5 mins
How do you justify cybersecurity spending when the goal is to prevent something that hasn’t...
- March 23, 2026
- 6 mins
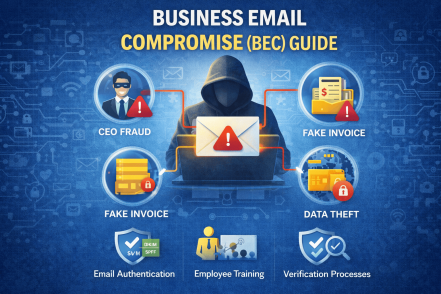
What if a single email could cost your company millions? That’s the reality of Business Email...
- March 20, 2026
- 5 mins
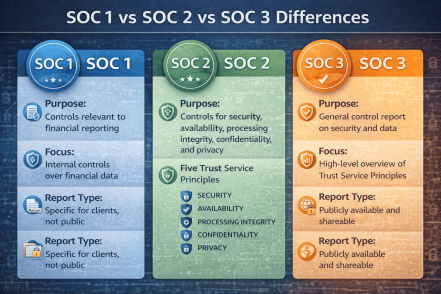
If your organization handles customer data, financial transactions, or cloud services, you’ve...

- March 20, 2026
- 5 mins
What would happen if a cyberattack disrupted your bank’s operations for just one hour? For...








