What Is an Endpoint Protection Service? Essential Guide for IT Leaders & CISOs
Updated on August 12, 2025, by Xcitium

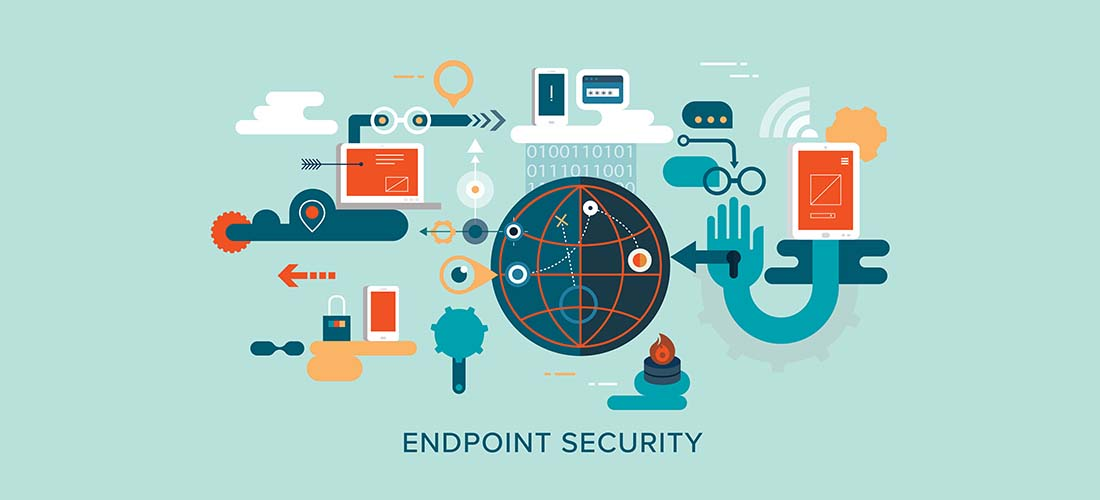
Ever wondered what an endpoint protection service truly does—and why organizations increasingly rely on it to secure a growing array of devices? At its core, endpoint protection service (EPP service) defends every device—from laptops and servers to mobile and IoT devices—against cyberattacks. For IT managers, cybersecurity leaders, and executives, understanding and implementing this foundational layer is essential in a world where breaches often start at the endpoint. Let’s unpack how these services help you stay secure, streamlined, and ahead of threats.
What Is an Endpoint Protection Service?
An endpoint protection service—also known as endpoint security or EPP platform—is a bundled solution that safeguards all network-connected devices, such as desktops, mobile devices, servers, and IoT endpoints, from malware, ransomware, and advanced cyber threats. These solutions have evolved from traditional antivirus tools into full-scale platforms enabling prevention, detection, and response in real time.
Why Endpoint Protection Matters More Than Ever
Endpoints are often the first gateway for breaches—up to 70% of data breaches start at an endpoint.
- Remote work and BYOD trends have significantly expanded the endpoint attack surface.
- Comprehensive endpoint security acts as the new network perimeter, closing gaps that traditional firewalls miss.
Core Components of Modern Endpoint Protection
- Real‑time Threat Detection — using behavioral analysis, ML algorithms, and threat intelligence.
- Endpoint Detection & Response (EDR) — provides continuous monitoring, threat hunting, and automated response.
- Device & Application Control — manages access, blocks unauthorized software, and controls USBs and apps.
- Patch & Vulnerability Management — ensures timely updates to close security vulnerabilities.
- Centralized Management Console (“Single‑pane‑of‑glass”) — provides unified visibility and control across all endpoints.
Endpoint Protection vs. Traditional Antivirus
| Feature | Traditional Antivirus | Endpoint Protection Service (EPP) |
| Threat Scope | Malware only | Malware, ransomware, zero-day, phishing |
| Detection Methods | Signature-based | ML, behavior analysis, AI |
| Response Ability | Manual removal | Real-time isolation, rollback, containment |
| Management | Local device only | Centralized policy & deployment |
Modern EPP platforms offer layered defenses far beyond the anti-malware focus of legacy antivirus tools.
Benefits Tailored for IT Leaders & Security Teams
- Proactive Defense: Blocks threats before damage occurs.
- Faster Incident Response: Automated containment and remediation.
- Visibility & Control: Full audit trails, asset tracking, and policy enforcement.
- Compliance Support: Helps meet PCI-DSS, GDPR, HIPAA requirements.
- Scalability: Easy deployment across on-prem, cloud, and remote endpoints.
Best Practices for Deploying Endpoint Protection Services
- Choose platforms offering both EPP and EDR capabilities.
- Enforce Zero Trust principles—verify every endpoint continuously.
- Use automated patch management to reduce risk windows.
- Educate and train staff to reduce risk from phishing and human error.
- Regularly audit and review policies, and adapt to new threats.
Future Trends in Endpoint Protection
- Increased AI adoption, enabling predictive threat detection.
- Expansion into hardware ecosystems, as seen with Canon.
- Growth in MDR (Managed Detection & Response) services—outsourced threat hunting and response.
- Shift towards XDR (Extended Detection & Response) for cross-layer visibility.
Frequently Asked Questions (FAQ)
- What is the difference between EPP and EDR?
EPP prevents attacks using antivirus, firewalls, and behavioral analysis; EDR adds real-time monitoring, threat hunting, and response capabilities. - Can endpoint protection work with remote devices?
Yes—cloud-based consoles and remote agents enable management across global, mobile, and BYOD environments. - Why not rely just on antivirus software?
Antivirus is reactive and limited to known threats. Modern EPP platforms are proactive, detecting unknown threats and managing endpoints holistically. - How does endpoint protection support compliance?
Through consistent deployment, logging, automated response, and near-instant containment across devices. - Should small companies invest in endpoint protection?
Absolutely—regardless of size, endpoint breaches pose serious business risks. Scalable solutions can fit diverse teams and budgets.
Final Thoughts
An endpoint protection service is no longer optional—it’s foundational. By combining prevention, detection, and rapid response in a centralized platform, EPP supports secure operations, reduces breach risk, and enables resilient, agile cybersecurity leadership.
Ready to Strengthen Your Endpoint Strategy?
Explore how layered endpoint defense, AI-driven threat intelligence, and unified visibility can empower your security posture.