What Is DMZ in Networking? A Complete Guide for IT Leaders
Updated on October 8, 2025, by Xcitium
Did you know that over 70% of cyberattacks target applications and services exposed to the internet? For IT managers and cybersecurity professionals, protecting business-critical systems means balancing accessibility with security. That raises the question: what is DMZ, and why is it important for modern enterprises?
Introduction: Why DMZ Is Still Relevant
A DMZ (Demilitarized Zone) in networking is a separate network segment that acts as a buffer zone between an organization’s internal network and the public internet. It isolates public-facing systems like web servers, email servers, and DNS servers from sensitive internal resources, reducing the risk of cyber intrusions.
What Is DMZ?
In networking, a DMZ (Demilitarized Zone) is a physical or logical subnetwork that hosts an organization’s external-facing services. It is designed to limit exposure by creating a controlled environment where outsiders can interact with necessary resources without accessing the corporate LAN.
Key Characteristics of a DMZ:
-
Isolates public-facing servers from internal systems.
-
Uses firewalls to control traffic flow between zones.
-
Provides an additional layer of defense against cyberattacks.
-
Supports compliance by segmenting sensitive data.
👉 In simple terms: A DMZ is a protective shield that separates what’s public from what’s private.
Why Businesses Need a DMZ
Without a DMZ, external users directly interact with internal systems—an enormous security risk. For IT managers, implementing a DMZ is about reducing the attack surface and maintaining business continuity.
Benefits of a DMZ:
-
Enhanced Security – Prevents attackers from moving laterally into corporate networks.
-
Regulatory Compliance – Meets standards like PCI DSS, HIPAA, and GDPR.
-
Service Availability – Ensures public services (web, email, DNS) remain operational even under attack.
-
Traffic Control – Monitors and filters inbound/outbound requests effectively.
-
Business Continuity – Minimizes damage if external services are compromised.
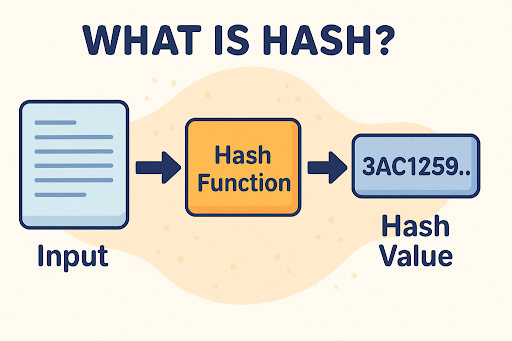
How Does a DMZ Work?
A DMZ operates by segmenting network layers and controlling access via firewalls.
Typical DMZ Setup:
-
Public-Facing Services – Web servers, FTP servers, DNS, and email servers placed in the DMZ.
-
Firewalls – One firewall separates the DMZ from the internet, another separates it from the LAN.
-
Access Control Rules – Define who can access services in the DMZ and what data can flow back to the internal network.
-
Monitoring Tools – IDS/IPS systems detect suspicious activity in the DMZ.
👉 This layered approach means that even if a hacker breaches a public server, internal systems remain protected.
DMZ vs Firewall: What’s the Difference?
A common misconception is that a firewall replaces the need for a DMZ. In reality, both complement each other.
| Feature | Firewall | DMZ |
|---|---|---|
| Function | Blocks or permits traffic | Segments public-facing apps |
| Placement | Between networks | Between internet & LAN |
| Protection Level | Packet/traffic filtering | Isolates risky services |
| Best For | General security | Public service hosting |
👉 Verdict: Firewalls filter. DMZs isolate. Together, they harden defenses.
Security Risks Without a DMZ
Operating without a DMZ exposes enterprises to critical risks:
-
Direct Exposure – Internal systems face the internet with no barrier.
-
Lateral Attacks – Hackers can move freely inside the network after one breach.
-
Service Downtime – A compromised web server can take down business-critical apps.
-
Regulatory Violations – Failure to segment networks can result in compliance fines.
For cybersecurity leaders, skipping a DMZ is like leaving the front door unlocked.
Best Practices for Implementing a DMZ
-
Use Dual Firewalls – Separate internet-to-DMZ and DMZ-to-LAN traffic.
-
Least Privilege Access – Limit user and service permissions strictly.
-
Regularly Update Servers – Patch vulnerabilities in DMZ systems.
-
Deploy Intrusion Detection Systems – Monitor unusual activity in real time.
-
Isolate Critical Apps – Place sensitive apps in the LAN, not the DMZ.
-
Integrate with Zero Trust Models – Treat every connection as untrusted.
Real-World Use Cases of a DMZ
-
E-Commerce Websites – Hosting payment gateways in DMZ to protect customer data.
-
Healthcare Systems – Isolating patient portals from hospital records.
-
Financial Institutions – Using DMZs to secure online banking platforms.
-
Corporate Email – Preventing attackers from pivoting from mail servers to LAN.
-
DNS Hosting – Ensuring external DNS lookups don’t compromise internal networks.
The Future of DMZ in Cybersecurity
As enterprises shift to cloud and hybrid networks, the concept of a DMZ is evolving:
-
Cloud DMZs – Virtualized demilitarized zones in public and private cloud.
-
SD-WAN & Zero Trust – Replacing static perimeters with dynamic, identity-based segmentation.
-
Microsegmentation – Breaking down networks into smaller, more secure segments.
-
AI-Powered Monitoring – Automated detection of anomalies in DMZ traffic.
👉 Even in modern architectures, the principle of network isolation remains essential.
FAQs: What Is DMZ?
1. What does DMZ stand for in networking?
DMZ stands for Demilitarized Zone, a network segment for isolating public-facing services.
2. What is the purpose of a DMZ?
To provide an extra layer of security by keeping external services separate from internal systems.
3. Is DMZ still relevant in 2025?
Yes. While modern solutions like Zero Trust evolve the concept, DMZ principles remain vital.
4. What’s the difference between DMZ and VPN?
A VPN provides secure remote access, while a DMZ isolates servers exposed to the internet.
5. Can hackers bypass a DMZ?
If misconfigured, yes. But when combined with firewalls and monitoring, a DMZ significantly reduces risks.
Conclusion: Why Every Business Needs a DMZ
So, what is DMZ? It’s a network security strategy that isolates public-facing services from sensitive corporate systems. For IT managers, CEOs, and cybersecurity leaders, a DMZ is not an outdated concept—it’s a foundational layer of defense that reduces risks, supports compliance, and strengthens resilience.
As cyberattacks grow more sophisticated, businesses must evolve, but the principle remains the same: segregate, monitor, and protect.
👉 Take the next step in safeguarding your enterprise: Request a Demo