
- April 24, 2026
- 9 mins
As cyber threats continue to evolve in both sophistication and scale, and as workforces become...

- April 24, 2026
- 9 mins
As organizations grow, expand into new geographies, and adopt cloud-based applications, traditional...

- April 24, 2026
- 9 mins
In today’s rapidly evolving digital landscape, organizations are undergoing a massive shift...

- April 22, 2026
- 10 mins
In today’s rapidly evolving threat landscape, organizations are no longer struggling with a lack...
- March 26, 2026
- 5 mins
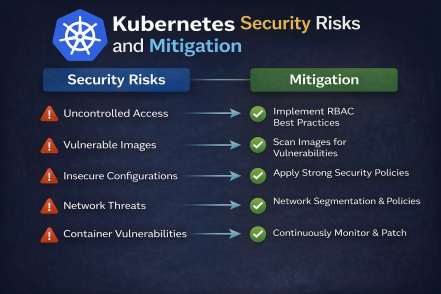
Kubernetes has become the backbone of modern cloud-native applications. But with great flexibility...

- March 26, 2026
- 5 mins
Is your AWS environment truly secure—or just assumed to be? Many organizations believe that...
- March 26, 2026
- 5 mins
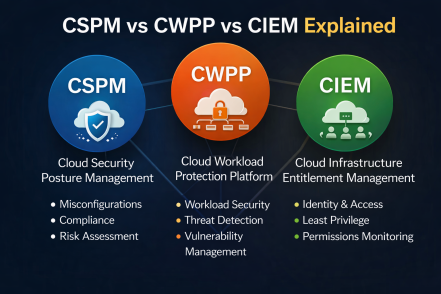
Cloud security is getting more complex every year. With businesses rapidly moving workloads to the...

- March 25, 2026
- 5 mins
What if your biggest cybersecurity vulnerability isn’t your technology—but your people? Studies...
- March 25, 2026
- 5 mins
What happens if your organization is hit by a cyberattack today—would you recover quickly or face...








