In a world where security breaches and theft are a growing concern, surveillance systems are no...
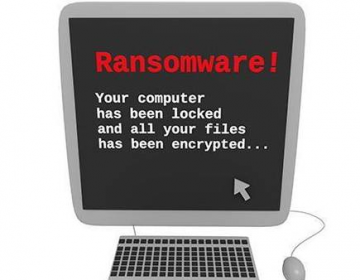
Ransomware attacks are becoming rampant. And it’s solely knowing to stop your laptop and...

The terminology “Data security” refers to the protective measures of securing data from...
One of the leading online threats we face today is ransomware. So much so, tech security companies...

Endpoint security is about protecting your network from the various security threats various...
Cyberattacks have become a part of our digital lives. Malicious software programs are launched in...

The role and capabilities of endpoints have progressed dramatically in the past few years, and...

There is a shortage with the cybersecurity skills worldwide and it will not be easy anytime soon....

Gone are those days when we managed to secure data in a secluded environment. From the rise of the...

The term threatware is commonly used to refer to computer programs that are designed to harm your...