The MITRE ATT&CK Framework is a comprehensive knowledge base that provides various matrices for comprehending tactics, techniques and procedures adversaries use. ATT&CK in ATTACK MITRE stands for Adversarial Tactics, Techniques & Common Knowledge that MITRE develops.
Security professionals use the ATTACK MITRE Framework for identifying and analyzing potential vulnerabilities and risks associated with an organization’s security posture. Its common language for describing cyber-attacks helps organizations for developing effective defenses against them. The major beneficial factor of this organization is that it regularly updates the knowledge base to reflect on the new tactics and techniques used by adversaries. This makes an updated resource for security practitioners.
How Does The ATTACK MITRE Framework Gather Data?
The data accumulation in the ATTACK MITRE Framework comes from sources that include malware analysis reports, public threat intelligence, and real-world incidents. ATTACK MITRE operates with several organizations and government agencies to ensure the framework reflects the latest trends and developments in the cybersecurity landscape.
The Framework of ATTACK MITRE is continually updated based on feedback and contributions from the broader cybersecurity community. This collaborative approach ensures that the framework remains relevant and effective EDR in helping organizations defend against cyber-attacks. Threat intelligence professionals use ATTACK MITRE to understand various ways bad actors operate so adversarial behaviors can be detected and stopped.
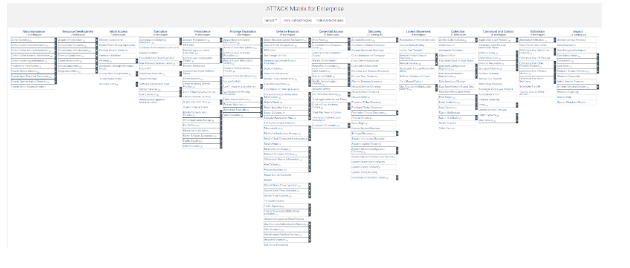
What Are MITRE ATT&CK Matrix Tactics And Techniques?Certain adversaries use certain attack techniques while staying undetectable. The ATTACK MITRE Framework curates the information that correlates adversary groups to campaigns. The various ATTACK MITRE matrices are what give you the visual representation of the tactics, techniques and procedures adversaries use during cyber attacks. The matrix is organized into rows of tactics and columns of techniques, making it easy to identify potential attack vectors and prioritize defensive measures.
TacticsAdversarial tactics on ATTACK MITRE are specific technical objectives the adversary intends to achieve. For instance, defense evasion, lateral movement, or exfiltration. Tactics can be categorized and organized according to these intended goals on the ATTACK MITRE matrix. In the enterprise matrix there are more than 14 tactics are cataloged:
- Reconnaissance
- Resource Development
- Initial Access
- Execution
- Persistence
- Credential Access
- Privilege Escalation
- Defense Evasion
- Discovery
- Lateral movement
- Collection
- Command and Control
- Exfiltration
- Impact
Techniques in an ATTACK MITRE matrix are known as one specific way an adversary might try to obtain a specific goal. Users can find a plethora of techniques under each tactic category on the ATTACK MITRE matrix. It’s because a specific adversary may use several techniques for a tactic depending on factors like their skill sets, targets’ system configuration or availability of tools. Each technique shows a method description, systems & platforms used and, which adversary groups use the technique, mitigating ways, and real-world use references.
How To Use The ATTACK MITRE Framework?
Using the ATTACK MITRE framework is essential for cybersecurity professionals to better understand tactics and techniques used by adversaries in cyber attacks. So how to use Mitre ATT&CK? Below are the steps you need to use for ATT&CK:
- Identify The ATT&CK Techniques
- Read The ATT&CK Technique Pages
- Explore Additional Resources
- Conduct An Emulation
In the first step, you need to identify the specific techniques used by an adversary in a particular attack through the ATTACK MITRE framework. Analyze security logs and incident response reports for conducting threat intelligence research and use other cybersecurity tools and methods for identifying the attack.
Once a specific technique used in the attack is identified, go to the corresponding page in the ATTACK MITRE framework. The ATTACK MITRE Technique page would describe how adversaries use it, what platforms it targets and the detection & mitigation process. The technique description page may include real-world incidents and examples of the technique's use.
Once a specific technique used in the attack is identified, go to the corresponding page in the ATTACK MITRE framework. The ATTACK MITRE Technique page would describe how adversaries use it, what platforms it targets and the detection & mitigation process. The technique description page may include real-world incidents and examples of the technique's use.
Once you are familiar with the technique and have explored additional resources on the ATTACK MITRE framework, it’s time to conduct an emulation. It would test your organization’s network defenses against the technique. Emulation involves simulating an attack using the same tactics and techniques adversaries use, as mentioned in the ATTACK MITRE framework. This can be done using various Mitre ATT&CK techniques and tools for penetration testing, red teaming or cyber defense exercises.
While conducting an emulation, you can test your organization’s detection and response capabilities. This would help identify any weaknesses or gaps in your defenses. You can use the results of the emulation to improve your defenses to develop more effective security strategies. It’s all possible with an understanding of ATTACK MITRE techniques on the framework base.
Security professionals can use the ATTACK MITRE matrix to analyze gaps and plan improvements. This helps with strengthening cyber threat intelligence and accelerating alert triaging and investigation. You can use it for more realistic red team exercises and adversary emulations scenarios. Get in touch with Xcitium to integrate the right solution for threat detection of your ATTACK MITRE navigator tool for bridging the security gaps.
