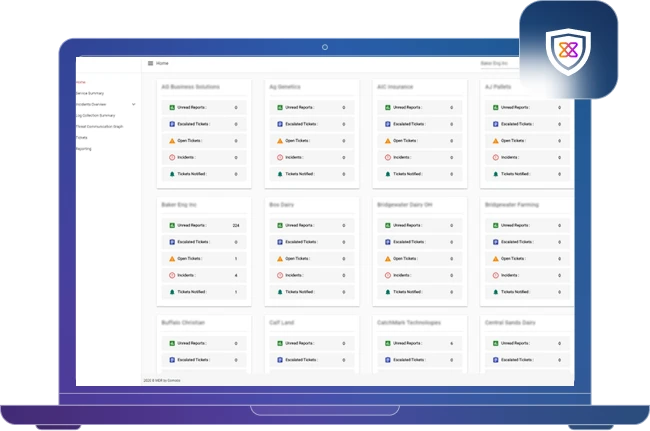
White Label our SOC Platform with Your Brand
Xcitium’s complete SOC platform offers full white label capability for any MSP, MSSP, or Enterprise. SOCaaP is ready-made to provide access to your own SOC in under 24 hours, with zero capital outlay. It provides a unified view across all your clients in one pane-of-glass.
Why MSPs Should Move Their Customers To
A Government-Compliant MSSP Platform
CISA, America’s Cyber Defense Agency, has come out with an advisory for protecting against cyber threats to managed service providers (MSPs) and their customers. The summary highlights MSPs should implement endpoint detection and response (EDR), secure remote access, comprehensive monitoring, and incident response plans. Note that cybersecurity insurance providers typically require these guidelines for eligibility.

How It Works
We have the only Managed SOC that is built by a platform provider. Other companies simply “Frankenstein” together solutions for MSPs. Xcitium’s SOCaaP provides MSPs with a multi-tenant view of all their clients in on pane-of-glass.
Key Features
Become an MSSP Overnight!
Start earning a profit with lucrative cybersecurity as a service options. The integrated MSSP platform is while-labeled as you and your brand; no minimum requirements, simply pay as you go.

Seasoned Security Analysts
Performing Event Validations
All events are validated by the Xcitium MSSP Platform SOC Analyst team prior to alert reporting. No need to aggregate, correlate, or contextualize alerts. Our security team generates custom reports, and provides your customers with guidance that will benefit long term success and security.

Proactive Threat Hunters
The MSSP Platform Team is a global team of highly-skilled professionals with expertise in incident handling and response, forensic analysis, SOC analysis, identity protection, threat hunting, and IT administration.

Integrated EPP & EDR
Get access to Advanced Endpoint Protection and Endpoint Detection & Response to secure all of your customers endpoints with Zero Threat, next-gen malware protection, and endpoint telemetry.

Threat Intelligence-Based
Detections and Analytics
Our SOC analysts leverage proprietary and global threat intel derived from Threat Labs research, threat hunting, 24/7 continuous data monitoring, and our Verdict Cloud malware analysis engine.
Benefits
Profitable MSSP
Security Analysts
Threat Hunting
Cybersecurity
Compliance




