Cyberattacks in this digital world are increasing day by day. You will notice that our digital data is at high risk due to the rise of cyberattacks. There are several types of attacks, and they all are highly dangerous for your system. A ransomware attack is one of the prevalent ones and can harm your system. This article will explain the ransomware attack and how to protect yourself.
Ransomware Attack
A ransomware attack is a technique in which the attackers control your computer. They will lock the data and then demands a ransom from the victim, promising to restore access to the data upon payment. In this attack, payment is required in the form of cryptocurrencies like Bitcoin to hide the identity and location of the attacker. Once all the files are encrypted behind the password, a text file is available to the victim.

People make payments hoping victims will send the files. When you send the money, there is still no guarantee that hackers sending the decryption key or unlock the files.
How does ransomware work?
- Generally, ransomware starts with phishing attacks. There are multiple reasons why the attacker gets access to the victim's device. Some of the most common ones are emails, malicious sites, and messages, and then they encrypt the data in that device.
- Once they have access to the files, they use simple asymmetric encryption algorithms which block the user's files. It makes it difficult for the user to decrypt the file.
- Not only this, but they also look for the location of targeted file types that include files stored locally and mapped and unmapped network-accessible devices.
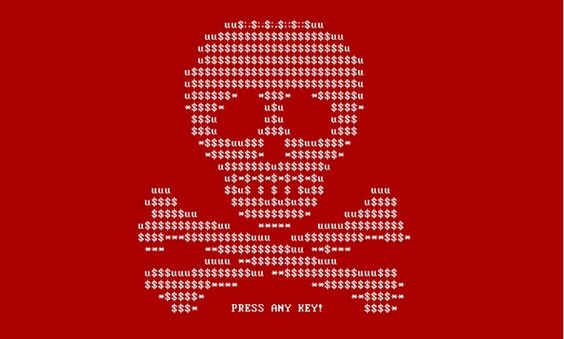
- Once the encryption is completed, the ransomware gets prepared to make ransom demand. Different ransomware variants implement this differently, but it's not uncommon for a ransom note to be displayed as the display background or for ransom notes to be placed in encrypted directories. The amount is set in cryptocurrency to access the victim's files.
It can also breach a system using RDP access, a remote desktop protocol. A hacker can quickly gain remote access to a computer using this protocol, allowing them to install malicious software without the owner knowing.
How can you prevent ransomware attacks?
There are specific ways through which you can protect your system against ransomware. Here are some of the ways you need to learn.
Cyber awareness training and education
As you now know that ransomware is often spread using phishing emails. With the help of training, you can identify how to avoid potential ransomware attacks. Multiple times it's seen that an individual receives an email that does not even contain malware but only a socially-engineered message that encourages the user to click on a malicious link. All these things demand user education which makes it highly necessary.

There should be continuous data backups.
Ransomware is malware, and if you come into a trap of the same without paying the ransom, there is no way to restore access to the encrypted data. With the help of data backups, you can minimise data loss without even paying a ransom. You must understand that you regularly maintain the data and backups, as a routine process is essential.
User authentication
Using stolen user credentials to access services like RDP is a favourite technique of ransomware attackers. It will be challenging for the attacker to guess or steal passwords due to the strong user authentication. So, it is another reason to prevent ransomware.
Use patching
Defending against ransomware attacks is also crucial since cyber-criminals often target systems that haven't been patched with the latest found exploits. Organisations must ensure that all the systems have the latest patches applied to them, as this reduces the number of potential vulnerabilities within the business for an attacker to exploit.
Application whitelisting and control
You can establish device controls on your device, limiting applications installed to a centrally controlled whitelist. Ensure you increase browser security settings, disable Adobe Flash and other vulnerable browser plugins, and more to prevent going to malicious sites.
Protect your email
This is another way to protect from the cyberattack. You must train the employees, which makes them recognise social engineering emails, and conduct drills to test if employees can identify and avoid phishing. Make sure you use spam protection technology to block suspicious emails automatically, and if the user clicks on them, block malicious links.
Final Words!
Ransomware is a popular cyberattack that is becoming common due to the shift in corporate work culture from in-office to working from home. It is challenging for people to detect ransomware activity due to a lack of education among the individual. You must keep up with all the above points to reduce your heavy burden.You can consult Xcitium for more information about ransomware and free your system from its effect. Visit their website to learn more about them https://www.xcitium.com