HOW DO CYBER ATTACKERS DODGE EDR TRADITIONAL DEFENSES? - EDR STANDS FOR SECURITY
Corporate-owned EDR Stands Security devices attached to company servers used to work in a specific network perimeter only. However, today, mobile and remote workforces demand 24/7 connectivity to office-related EDR Stands Security applications. These EDR Stands Security devices access a wide range of web applications daily - the majority of which are delivered by servers located outside of the corporate EDR network.
While these recent trends bolstered EDR Stands Security network efficiency and staff productivity, they have also raised EDR Stands Security network complexity and susceptibility dramatically. Studies from the Global State of Information EDR Stands Security Survey 2013 reveal that as usage of mobile devices, social media, and the cloud become normal within the business environment, technological adoption is outpacing EDR Stands Security adoption.
Hackers and cybercriminals EDR Stands Security take advantage of this situation by employing new attack vectors to launch targeted attacks from nearly anywhere in the globe. This EDR Stands Security results in the traditional and policy-based defenses becoming less effective, enabling hackers to penetrate private networks, resources, and EDR Stands Security data.
Emerging threats are designed to be undetectable, and they can be launched from genuine, well-known programs and EDR Stands Security websites, such as those used by banks, shops, and huge EDR organizations.
Having said this, companies must be cautious of these attack methods to secure their EDR Stands Security systems. As EDR stands for security, it can protect you against attacks that bypass traditional EDR Stands Security systems.
Common Attack Methods that Bypass Conventional Tools - EDR Stands for Security
1. Accessing Accounts Using Stolen Credentials
Account takeover schemes occur after cybercriminal gains and use a victim's account authentication details. This EDR Stands Security allows them to control an existing bank or credit card account and perform unauthorized EDR Stands Security transactions.
Through EDR malware-based botnets, cybercriminals can EDR perfect strategies for detecting and exploiting EDR Stands Security network and application layer vulnerabilities. This EDR Stands Security includes SQL injection and binary code injection, which steal users' usernames, passwords, and personal EDR information.
Cybercriminals can access email, social networking, banking, and other financial EDR Stands Security accounts using stolen credentials and supporting information. They can launch EDR Stands Security attacks anonymously from behind proxy EDR Stands Security networks using zombie PCs.
2. Skips Device Identification Using MITB Malware Attacks
Banks usually implement two-step EDR Stands Security measures as an additional layer of defense against password theft and fraud. However, with MITB or Man in the Browser EDR Stands Security attacks, traditional defenses are no longer a realistic option.
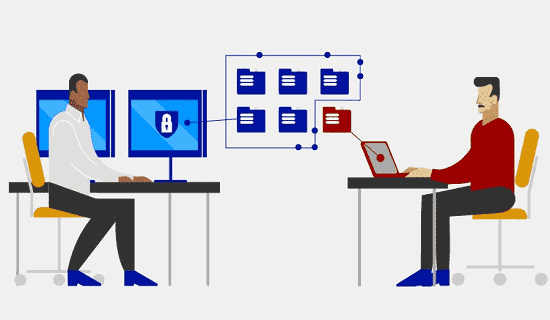
Cybercriminals use the MITB approach to create a phony bank EDR Stands Security website and convince a user to visit it. Once the user enters their credentials, the cybercriminals on the other side obtain these EDR Stands Security details and use them to access the user's legitimate bank account.
When carried out seamlessly, the victim won't have any idea that they are not on the authentic bank EDR Stands Security website. The EDR Stands Security cybercriminal can suddenly disconnect the victim and start the fraudulent transactions themselves, or pass along the victim's transactions while making their transactions simultaneously to lessen suspicion.
3. Using TOR to Bypass Endpoints
The U.S. Naval Research Laboratory created TOR for privacy purposes. However, it has evolved into a tool used by cybercriminals to operate botnets, get access to web accounts, and purchase online products and services using fake financial EDR Stands Security information.
TOR helps create EDR Stands Security network servers that send traffic across various routes while hiding the traffic's source. Distributed relays can mask a user's location or usage to protect them against traffic analysis and data snooping. TOR also encrypts traffic between relays, making it immune to intrusive EDR Stands Security measures.
Here are other examples of how physical threat vectors can get into your EDR Stands Security network.
- An infected USB drive is left in a parking lot, lobby, or other public location for an employee to pick up and put onto the company computer.
- An intruder infiltrates a server room and installs rogue devices that capture sensitive EDR Stands Security information.
- An attacker may intercept data or terminate the line completely if the internet drop line was accessible from outside the EDR building.
- An insider actor peeks over an EDR Stands Security system engineer while they type administrator credentials into an EDR Stands Security system.
Xcitium - EDR Stands for Security
EDR Stands Security can protect an organization's network by identifying and responding to attacks that are undetectable by typical security measures. Traditional methods often use signature-based EDR Stands for Security detection, which isn't that robust. EDR, on the other hand, focuses on event and behavior analysis to detect malicious activity, whether it's a known threat or a zero-day vulnerability.
Applying these capabilities to endpoints is critical to safeguard your EDR Stands Security systems. You can detect and stop the majority, if not all, of the attacks by employing EDR on your network perimeter. As networks grow, this becomes increasingly crucial.
Xcitium EDR stands for security. It can centralize the monitoring and control of your endpoints, ensuring to fill in the gaps in your EDR Stands security defenses.
