
- February 02, 2026
- 6 mins
Cyberattacks don’t always start with malware or brute force. Often, they begin with a single,...
- February 02, 2026
- 6 mins
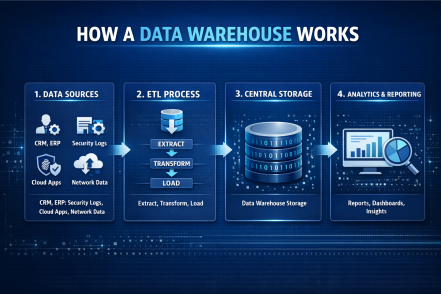
Data is everywhere—but turning raw data into meaningful insights is still a major challenge. If...

- February 02, 2026
- 3 mins
Microsoft provides a strong foundation for productivity and baseline security—but true protection...

- February 02, 2026
- 3 mins
Give your Microsoft ecosystem a higher level of security—without upgrading licenses or adding...

- January 30, 2026
- 6 mins
Have you noticed your computer slowing down, showing strange pop-ups, or behaving unpredictably?...

- January 30, 2026
- 5 mins
Have you ever tried running a script only to be blocked by Windows security warnings? Knowing how...
- January 30, 2026
- 6 mins
What is API integration, and why does it matter so much in today’s digital-first world? From...
- January 28, 2026
- 6 mins
Have you ever opened File Explorer in Windows 11 only to find missing files, outdated folder views,...
- January 28, 2026
- 7 mins
Email remains the backbone of business communication—but have you ever wondered what is an IMAP...








