- February 13, 2026
- 6 mins
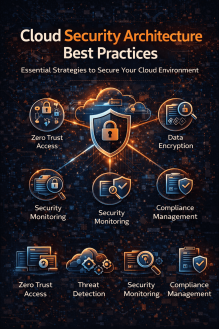
Cloud adoption continues to surge across industries. Organizations are rapidly shifting to public,...

- February 12, 2026
- 6 mins
What is SSO login, and why are so many organizations adopting it? If your employees juggle multiple...

- February 12, 2026
- 6 mins
What is Skybox, and why are security teams and IT leaders talking about it? In today’s threat...

- February 12, 2026
- 7 mins
What is a local network, and why should IT managers and CEOs care about it? Every email sent inside...
- February 11, 2026
- 6 mins
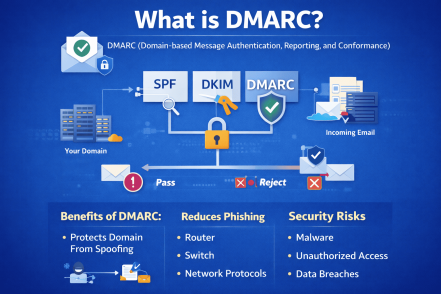
Email remains the #1 attack vector for cybercriminals. In fact, phishing and spoofing attacks cost...
- February 11, 2026
- 6 mins
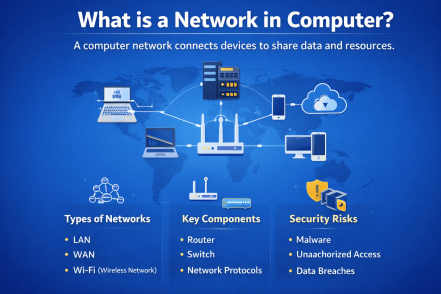
Have you ever wondered how your laptop connects to the internet, shares files with colleagues, or...
- February 11, 2026
- 7 mins
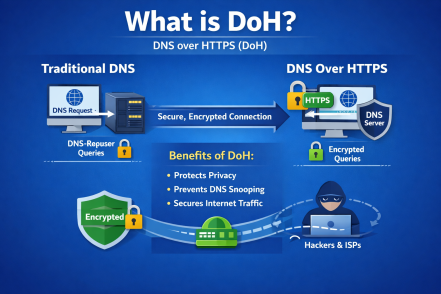
Have you ever wondered how exposed your DNS traffic really is? If you’re asking what is DoH,...
- February 10, 2026
- 7 mins
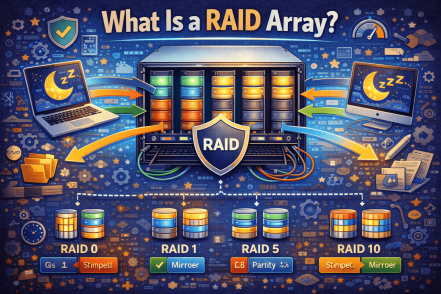
Data loss is one of the most expensive and disruptive problems an organization can face. Whether...

- February 10, 2026
- 6 mins
Have you ever discovered tools, applications, or processes running in your organization that no one...








