Access logs are detailed server records that document every request made to a system, website, or application. They provide time-stamped entries of user activity, revealing who accessed what, when, and from where. For businesses, they are indispensable for security monitoring, troubleshooting, and analytics.
Types of Access Logs
Understanding the different kinds of access logs helps in better monitoring and analysis.
Web Server Access Logs
- Used by Apache and Nginx to track HTTP/HTTPS requests.
- Show client IP, requested resource, status code, and user-agent.
Application Access Logs
- Monitor interactions within software or APIs.
- Record API requests, data queries, and session activities.
System Access Logs
- Found in Linux (/var/log/secure) or Windows Event Viewer.
- Track login attempts, user account activity, and privilege use.
Error Logs vs Access Logs
- Error logs capture failures only; access logs record all requests.
- Both are vital for root-cause analysis.
Cloud Access Logs
- AWS S3, Azure Storage, and Google Cloud all offer access logging to monitor cloud resource usage.
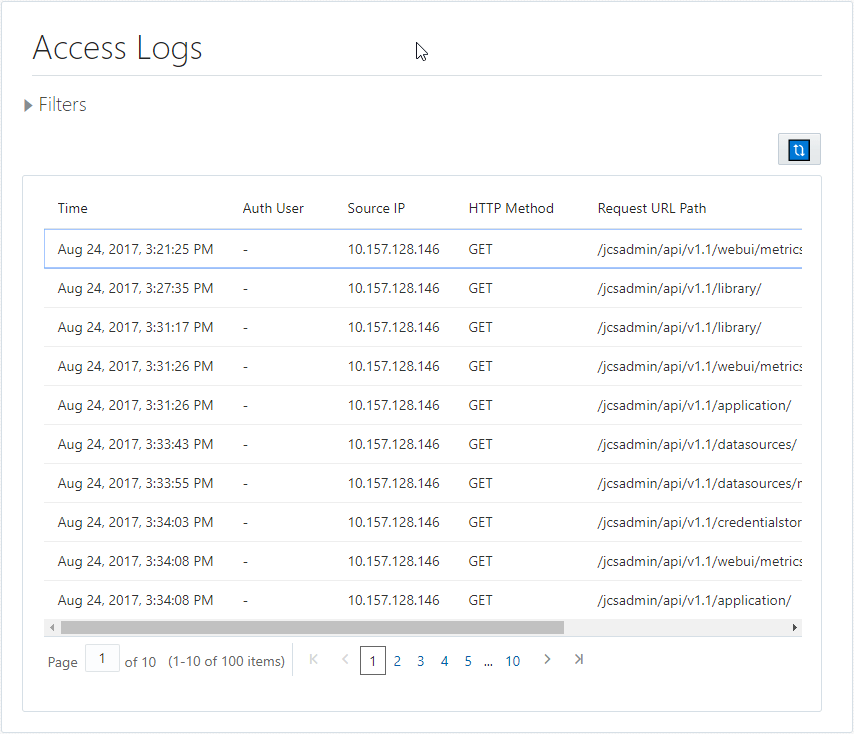
What Do Access Logs Record?
An access log entry can include:
- Timestamp – Exact date/time of access.
- IP Address – Identifies the client device.
- HTTP Method – GET, POST, PUT, DELETE, etc.
- Requested URL – The page or file accessed.
- Status Code – 200 OK, 404 Not Found, 500 Server Error.
- Referrer URL – Where the visitor came from.
- User Agent – Browser or device used.
- Bytes Sent – Size of response data.
Example (Apache Combined Log Format):
swift CopyEdit 203.0.113.45 - - [06/Aug/2025:09:21:15 +0000] "GET /dashboard HTTP/1.1" 200 3456 "https://example.com/login" "Mozilla/5.0"
Why Access Logs Are Important
Access logs serve multiple purposes beyond simple tracking.
Security Monitoring
- Detect suspicious IPs.
- Identify brute-force attempts.
- Monitor unauthorized resource requests.
Performance Optimization
- Find slow-loading resources.
- Detect high-traffic endpoints.
Compliance & Auditing
- Support HIPAA, PCI-DSS, and GDPR requirements.
- Serve as verifiable audit trails.
Business Insights
- Map user journeys.
- Improve marketing campaigns.
Where Are Access Logs Stored?
Apache (Linux): /var/log/apache2/access.log
Nginx (Linux): /var/log/nginx/access.log
IIS (Windows): %SystemDrive%\inetpub\logs\LogFiles\W3SVC1
How to View Them:
- Linux CLI: tail -f /var/log/nginx/access.log
- Windows: Event Viewer or file explorer.
- Control Panels: cPanel, Plesk.
- Cloud Consoles: AWS CloudWatch, Azure Monitor.
How to Read and Analyze Access Logs
- Command Line: grep, awk, less.
- Log Management Tools: Splunk, Graylog, ELK Stack.
- Cloud Tools: AWS Athena, GCP BigQuery for log analysis.
Configuring Access Logs
- Choose formats: Common Log Format (CLF) or Combined Log Format.
- Add custom fields (GeoIP, session IDs).
- Apache example:
Perl CopyEdit LogFormat "%h %l %u %t \"%r\" %>s %b" common CustomLog /var/log/apache2/access.log common
Managing Access Logs
- Rotation: Prevents oversized files (logrotate for Linux).
- Retention Policies: Keep logs 3–12 months (or as compliance requires).
- Archiving: Compress and move to secure storage.
Platform-Specific Examples
- Apache - Default in /var/log/apache2/access.log.
- Nginx - /var/log/nginx/access.log.
- AWS S3 - Must be enabled per bucket.
- Windows UAL - Tracks feature/service access.
Access Logs for Security Monitoring
- Compare access logs vs audit logs.
- Use anomaly detection rules.
- Feed into SIEM platforms for correlation.
Marketing & SEO Insights
- Detect most-visited landing pages.
- Track referral sources.
- Find and fix broken inbound links (404 errors).
Best Practices
- Automate monitoring alerts.
- Encrypt logs.
- Regularly review and purge old entries.
- Comply with privacy laws.
FAQs (People Also Ask Optimization)
Access logs record all requests; error logs record only failures or problems.
Retention varies — 3–12 months for most businesses; longer if compliance requires.
Yes. They help identify crawling issues, broken links, and high-traffic content.
Many regulations (HIPAA, PCI-DSS, GDPR) require maintaining access records.
Check your platform’s default log location or use control panel/cloud dashboard tools.
Conclusion
Access logs are critical for security, compliance, performance, and marketing. By understanding their structure and value, businesses can transform raw data into actionable insights. Implement a structured log management strategy to maximize their benefits.