Why Does Your Organization Need EDR Security?
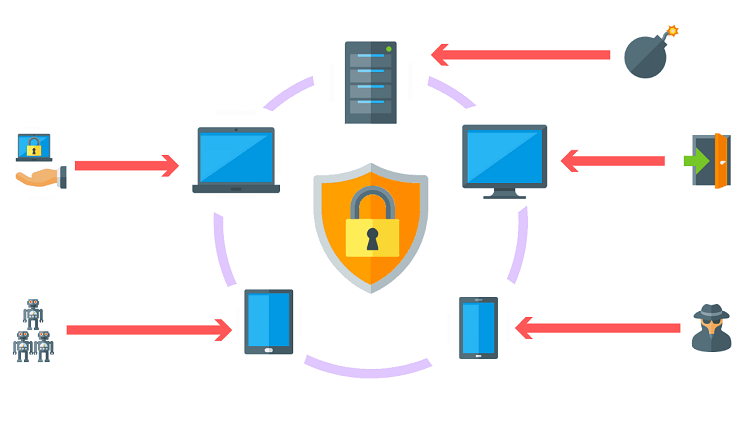
Organizations often face cyberattacks that put their assets, compliance posture, and brand reputation at risk. While there are traditional security tools you can use to deter and detect modern threats from penetrating your system, they don’t seem to be powerful enough.
To limit the adverse effects of security incidents, organizations need to reduce the dwell time or the time that attackers spend in an organization to steal data. Having a robust defense like EDR endpoint security could help address this issue. By using a multi-layered approach to cybersecurity EDR endpoint, it is able to buy time, delay attacks, or create enough roadblocks to fend off attackers.
What is Endpoint Detection and Response?
Endpoint detection and response (EDR Solutions) deploy coordinated defense methods that can block malware and other zero-day attacks to protect organizations from data breaches. It has the following capabilities:
- stores, records, and analyzes endpoint system-level behaviors
- blocks malicious activities
- centralized reporting and alerting
- detect unwanted malicious programs
- minimize detection of false positives
- eliminates threats
- provides remedial measures to restore the affected network.
Why Need EDR Tool?
Are you thinking about adopting this tool as part of your cybersecurity strategy? Here are some compelling reasons why you should use EDR endpoint security in your organization.
Ensures a strong security posture
Poor endpoint visibility is one of the reasons why organizations fail to understand the scope and impact of attacks. This usually happens when an incident occurs and the IT team thinks they are already safe because they were able to detect and remediate it. Little did they know that the same threat exists in another location.
EDR endpoint security tools provide additional insight as to how the machines are affected. This helps security analysts dive deep into incidents for additional investigation and potential remediation. Getting a clear view of your security posture can help you comply with regulations. It determines which areas are vulnerable to attacks and if these house sensitive company data.
Identifies attacks that have been missed
Sometimes, even the most advanced tools succumb to adversaries. Organizations typically depend on prevention to stay secure, and while this is helpful, it is ideal to have multiple layers of detection capabilities to find malicious files that have gone unnoticed.
Organizations can use (Endpoint detection response) EDR endpoint security tools to detect attacks by searching for key indicators of compromise. It will initiate the threat search after it receives a notification from third-party intelligence (like a government agency) saying there is suspicious activity in its network. EDR endpoint security tools may keep a list of the top suspicious events, which analysts can use to comb through their search. Using machine-learning capabilities, a list of the suspicious events is shown, ranked by their threat score. This makes it easy for analysts to determine which areas to focus on.
Suspicious events also highlight occurrences where analysts have to determine if something is indeed malicious. This refers to activities that do not appear to be malicious enough to automatically flag them but still suspicious enough to require a deeper analysis.
Endpoint responds Quick response to potential incidents
After identifying malicious incidents, IT teams usually act as fast as they could to reduce the spread of attacks and limit potential damages. But how fast can they eliminate each threat? The average time for IT teams to remediate each incident takes about more than three hours. With EDR security, resolution times decrease significantly.
The first thing the analyst usually does during incident response is to stop the attack from affecting other areas. EDR endpoint security tools can isolate endpoints, which is important to prevent a threat from spreading throughout the entire environment. Analysts often carry out this activity before investigating to buy time while they decide which course of action to take.
The investigation part can be slow if done manually by a human. But with EDR Endpoint software, security issues are fixed right away with the help of its guided investigations that offer suggested next steps, clear visual attack representations, and built-in expertise.
Endpoint Saves Time and Money
Organizations that leverage the power of EDR endpoint security can catch threats as early as they enter the system, thereby reducing the amount of time spent to re-image infected workstations. This ensures continuous productivity, business processes, and more financial gains for the company.
Takeaways
Some attackers wait patiently to evade your defenses and have better access to your network. That said, without clear visibility, you might not know if there have been intrusions that are wreaking havoc in your system. An EDR endpoint security tool can address this challenge. Call Xcitium, EDR Endpoint Solutions provider now to get the highest level of protection.
