Free Software Users Gonna Need Open Source Vulnerability Management
Updated on April 1, 2024, by Xcitium

Cybersecurity leaders who have expertise in identifying vulnerabilities in every digital technology are a blessing for us. As who could have alarmed us about dangerous critical security flaws such as the Log4J Shell vulnerability?
Let’s take the matter of open-source utilities seriously because governments have also started working for better alternatives and helpful solutions to secure the Open Source Ecosystem. As per the current modern trends, the utilization of open source software has increased rapidly. Hence, many believe that what can be wrong with employing these helpful software?
Time to face the reality of how disastrous and personal space trespassing it can be for users, who don’t have a needed open source vulnerability management plan.

Everything About Open Source Vulnerability Management
There is no denying that open source software, web browsers, and web applications have been helping us in our evolution in the digital sphere. Moreover, users seem more connected with their favorite resources of digital tools.
Nowadays, it doesn’t matter if their area of interest is regarding development, business, education, trade, entertainment, and cyberspace security. Although numerous things are unclear to many of us about open source software’s utilization and IT security.
In that case, here is everything you must know about open source software: its risks, demand, and cybersecurity elements. So, suit up, scroll down, and get all the insightful points in today’s informative article.
What Is Open Source Software?
An open source software works as a free-for-all platform supporting offering services under the technological domain. Basically it allows users to acquire the related available information, gain the skills to utilize it without the vendor’s permission, and employ it for professional and personal endeavors.
In simple, open source software types are not just limited to development platforms, as more than 96% of online available software involves open source components. It doesn’t matter if your under-usage software is a development platform such as Linux and Git or if you regularly explore search engines on Chromium and Mozilla, we are surrounded by open-source software. Other renowned and most trending free software include;
- Node.js
- JavaScript
- VLC Media Player
- Open VPN
- Godot Engine
- Apache
Isn’t Using Free Software Risky In The Light Of Cybersecurity?
Being easy to acquire, flexible, and personalized is not the only meaning of open source software. Because recent vulnerability incidents have cleared various harms of this type of web software and web browsers. So yes, the risk is doubled when we go for open source software for our daily activities and digital explorations.
Cybercriminals are taking advantage of all available open-source spots. In today’s time where vulnerability exploits, system breaches, data thrift, and ransom payment demand are at their peak, users must consider expert open source vulnerability management plans. Thus, it is highly important to learn about potential red flags of using free software before finding a suitable vulnerability management service provider.
Destructive Alarms Of Utilizing Open Source Software
Common users often don’t care about the open vulnerabilities that these types of software reveal. In fact, tech professionals such as web developers, mobile app builders, embedded designers, and cybersecurity engineers have to be more careful regarding the daily utilization of these technologies. Plus, the spread of the essential message of IT security precautions is also important.
Here is our step in sharing the destructive alarms of system faults that your daily employed open source software may include.
Weak System Security Issues
A platform freely available for all users and fulfilling their customized requirements may look promising. But as per the recent witnessed incidents, users can’t expect that their daily operational open source software can be end-to-end protected. As delay in service, computer system viruses, and endpoint hijacks highlight the weak security issues of open source software.
Blindly Trust On Open Source Software
You never know when hackers can take advantage of your daily used web application or browser. Showing dependency on the features and components may allow users to ignore every visible and undetectable cybersecurity threat. In fact, this is what cybercrime-as-a-service providers want people to believe and show blind trust in vulnerable platforms.
Perceived Control Over Software
Users think that they are in overall control of their employed open source technologies. Thus, the allocation of various entries into the same interface of software without the identification process may compromise the security of the stored data and other performed practices.
Attacks On Software Ecosystem
Exploiting any open components means risking software. In the same way, open source software can be dangerous for the whole ecosystem connecting millions to billions of users. Therefore, users can’t trust an online web application, development software, or entertainment hub that can damage the whole supply chain.
Blast Of Undetectable Malware
Every year there are new types of lethal malware that are introduced on the dark web and offered through cybercrime-as-a-service (CaaS). Daily users of open source software who are part of communities of millions to billions of members can’t locate malicious activities in the employing software that is harming their own digital networks.
Vulnerable Network Without Proper Documentation
Open source software may collect information from the users during the first time use in the form of ID login and online form filling. However, many software programs are running without a license and are far away from proper legal documentation. Meaning in no time users of these vulnerable software can face endpoint exploits and data thrift situations.
Lawful Compliance Issues
This alarming point is important for freelance developers and business firms using open source technologies. Following industrial compliance is important during offering services to others. Because connected participants can face legal charges and other official inquiries regarding data theft and ransom situations occurring with any linked customers or associated agencies due to vulnerable software.
What Is Tempting Users To Employ Free Software Despite All Risks?
Current endpoint users are excited minds. Similarly, their awareness about the benefits of online tools is impressive. Likewise, they jump into software, mobile applications, and web browsers that are easy to use, free of cost, and include various customized features.
May or maybe not, many of us are very much familiar with the negative consequences of operating open source software. Hence, the utilization of open source technologies is higher than closed-source software.
Here are the most identified reasons why users (developers, business professionals, tech engineers, and digital media enthusiasts) have chosen open source software as their prime digital technologies.
Easy, Flexible & Vast Customized Options
Consumers of these software feel more creative and independent while continuing their daily operations. Open source software are everyday tools for most of the users. Whether we believe it or not, effortless features, every component guide, and personalized touch in these free software have attracted users to choose them.
Free From All Users
Yes! One of the prime user services of these online tools is that they don’t have any premium codes and components that cloud stops specific users from operating them. So, in the game of cost efficiency, these software comes above other commercial technologies.
Freedom For Utilization
It doesn’t matter from where you are employing the services of selected software, you will be provided with the same user service. Meaning without any social barrier or vendor control, developers, company employees, and other consumers can easily utilize them.
Freedom For Innovation
There are numerous technical heads who have perfectly taken advantage of these software. As these modern inventions have built thousands of success stories. The advantage of learning about the expert utilization of software, modifying the source keys, and building great projects opens the door for users to become innovative personalities
Stamp Of Approval From Fellow Users’ Communities
Free software are expanded into all domains and industries, and the positive remarks from each community are enough to influence new users of these tools. The digital world is divided into different groups. In this case, each large community has its own fan-favorite software satisfying its customized needs.
People-Centered Technology
Updates in open source technologies have shaped them into people-centric inventions. People now can relate themselves to their daily utilized applications, web browsers, and entertainment hubs. Allowing the vendors of these vulnerable technologies to come up with new open source components.
Positive Global Demand
Consumer demand is everything. The success rate of open source tools is high because of people’s demands. And these people include corporate professionals as well. Therefore, without blocking these technologies, people should be furnished with other data protection solutions.
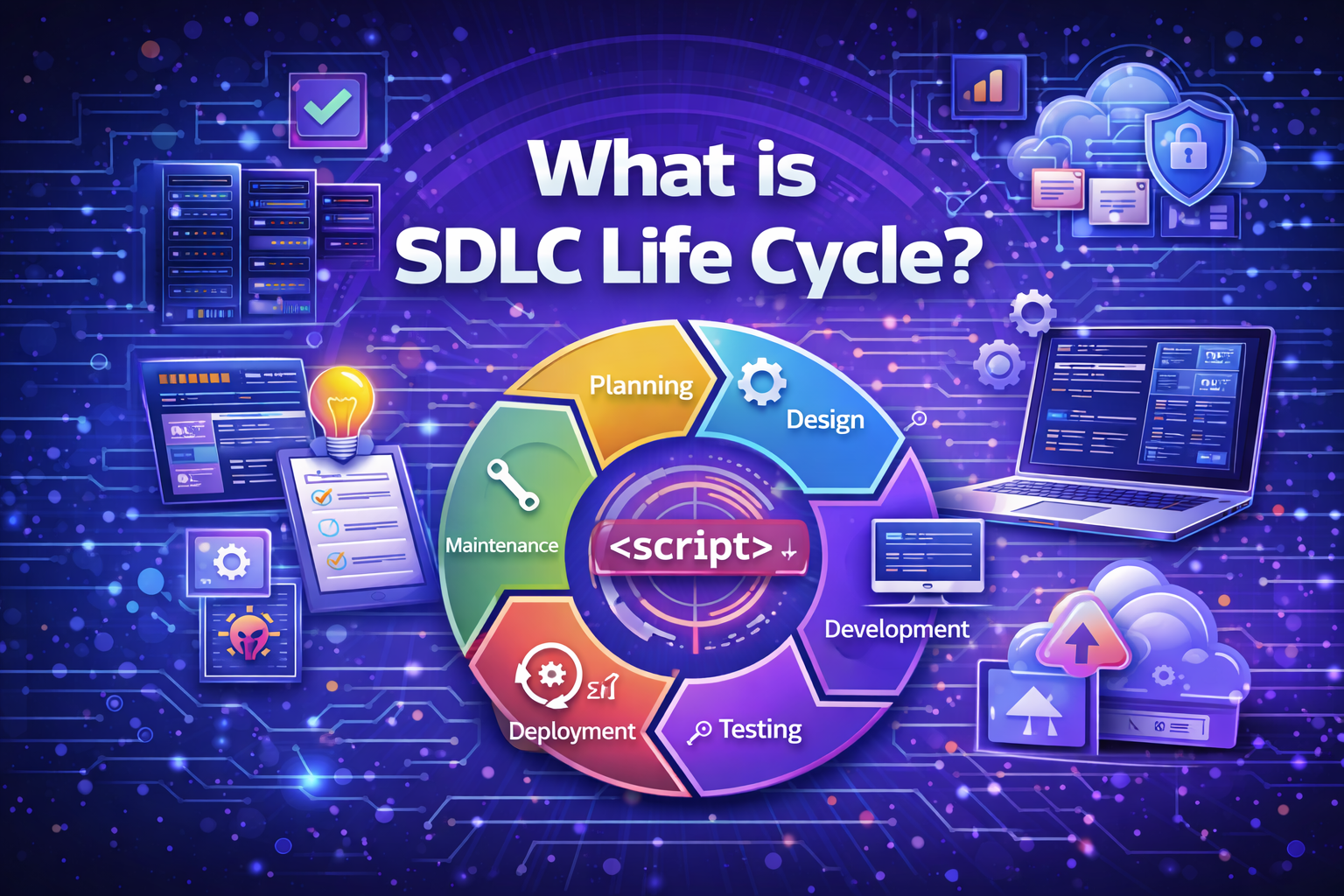
What Is Open Source Vulnerability Management?
The negative elements of open source software directly target the security of data and the personal space of users. It indicates that experienced cybersecurity firms won’t sit silently and will always come up with the best solutions for the users.
So, the service of open source vulnerability management is like a sustainable alternative for developers, business companies, government agencies, educational sectors, and other common users. In simple terms, open source vulnerability management offers weak point detection, speedy response, patch management, and other threat alerting assistance.
Open source vulnerability management service is mostly offered by managed IT and cybersecurity firms such as MSPs, MSSPs, and SOCs. By availing these services users will be able to continue their professional endeavors and personal activities without the fear of possible vulnerability exploits.
Here Is How Open Source Vulnerability Management Can Alter Every Possible Threat From Free Software
Cybersecurity and IT-managed service providers have answers for all the issues occurring due to every vulnerability exploit executed by anonymous hackers. And for fast troubleshooting of free software exploits, MSPs and MSSPs are actively offering open source vulnerability management services.
Not just the victim of all the phishing traps, system breaches, interface hijacks, data theft, and resume payments, but every user should be attentive and grab info about open source vulnerability management. Here is how this much-needed help works.
Speedy Threat Detection
The hired vulnerable management support won’t allow exploited software to cause harm. Through threat detection, users will have accurate data about the weak points and availability of malware in the system led by vulnerable free software.
Active Report Notification Of Each Threat
Allocated updated vulnerability management tools will report the detection of future threats along with a troubleshooting guide and network-protecting features. By this practice, users are informed about every possible threat along with advice on must-execute actions.
Automated Scanning Assistance With Mitigation
The automated features of vulnerability management tools scan the linked endpoints and cloud networks. Secondly, they also offer robust security assistance to each device connected with the software, as every linked gadget has to be scanned and must be protected from negative elements of vulnerable open source technology.
Unknown Open Source Vulnerability Monitoring
Not just the users but vendors of these free software can also obtain vulnerability management services from MSSPs. Round-the-clock monitoring of users’ devices and vendor’s open source technologies stop cybercriminals from performing their violating practices. In the same way, it allows both users and vendors to continue with their daily professional activities without fear of cyber breaches.
Expert Compliance Management
In order to keep up with compliance, professional employees and corporate companies will require experienced cybersecurity teams. However, hiring expert professionals of vulnerability management offering compliance handling services can save the day for those most target open source users.
Support In Continuing Professional & Personal Activities
Every security breach starts after vulnerable exploits. MSSP’s vulnerability management works like a support system for companies and professional business enterprises. It prevents every malicious activity and implements a safeguarding shield to cyberspaces.
Powerful Protection To Utilized Devices & Software
During the utilization of every software and device, the team behind vulnerability management protects every uncovered area from cyber attackers. As an unbreakable cyberspace protecting layer, the offered open source vulnerability management software avoids cyber-attacks, by instant weak point detection, accurate threat reporting, and effective troubleshooting assistance.
Xcitium Is Open To Resolve Your Open Source Vulnerability Management Issues
Business enterprises and corporate professionals have become sick of system breaches due to mediocre and vulnerable open source online programs. In this time of urgency, only the leading IT security brands like Xcitium can come for help. Because we are the only one that offers expert vulnerability management services and foremost zero-trust cybersecurity posture.