Advanced
Endpoint Detection
& Response (EDR)
Our Endpoint Detection and Response platform isolates threats instantly, maintains full visibility, and automates response to keep your operations running smoothly.

Our Endpoint Detection and Response platform isolates threats instantly, maintains full visibility, and automates response to keep your operations running smoothly.

Proactive endpoint defense without impact on performance or productivity.
Detect unknowns instantly to prevent threats before they can execute.
Lightweight endpoint agent captures system activity in real time without slowing devices.
Patented Auto-Containment™ instantly isolates unknown threats, keeping users safe and productive.
Advanced analytics and threat intelligence in Xcitium quickly identify suspicious behavior.
Automatically detects threats, capture forensic details, and generate compliance-ready reports instantly.
Discover the unique features that make
Xcitium EDR the preferred choice for enterprise security.
Prevents breaches by isolating unknowns in real-time.
Threats are neutralized before they ever execute.
Advanced behavioral engine detects and stops malicious activity in real time.
Proven to protect thousands of endpoints with centralized management.
Security without disrupting workflows or performance.
Reduce breach costs, compliance risks, and operational overhead.
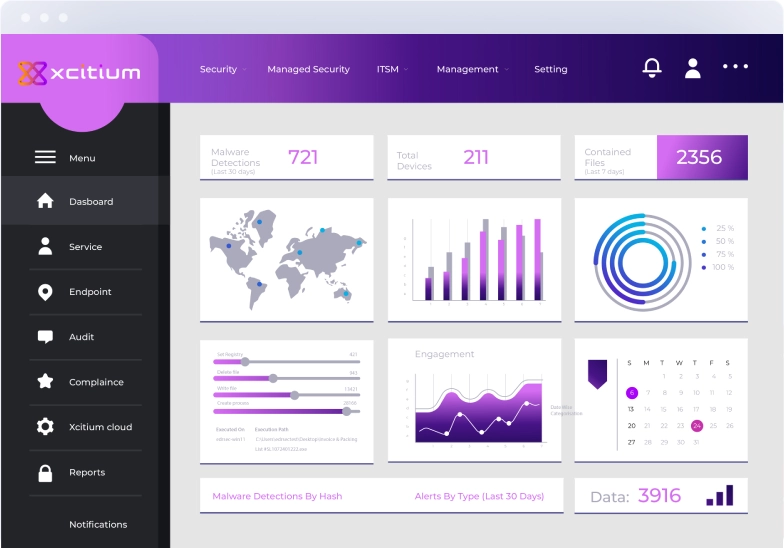
See how Xcitium EDR detects and contains threats instantly
while keeping your business running without disruption.

Comprehensive endpoint protection through intelligent detection, automation, and analysis.
Trusted by organizations worldwide
“Our paramount concern had been how we prepare for the unknown and how we ensure the protection of our endpoints. Xcitium came in and solved our concerns with the most advanced threat containment technology I have ever seen.”
IT Manager, BOLMET SA
“Before Xcitium, we were going through what seemed to be daily malware fixes and problems. Since Xcitium, we've had zero malware or spyware issues. We don't fear that unknown, zero day threat because we know the Xcitium Advanced Endpoint Protection suite can handle anything the cyber criminals try and throw at it.”
IT Manager, Christian Motorcyclists Association
“Xcitium Advanced Endpoint Protection gives us a streamlined dashboard where we can manage our endpoints, keep them secure, and perform installations and updates to our technology—with zero interruptions to our users.”
IT Analyst, City of Thousand Oaks
“We ran multiple tests and benchmarks of putting Xcitium, Symantec and other anti-virus technologies against one another to simply pick out who would perform best. When we tested the Xcitium endpoint security product, it detected viruses and malware that none of the other competing products detected.”
IT Coordinator, Community Action Committee of Pike County
Discover how Xcitium’s ZeroDwell™ Virtualization and Unified Zero Trust Platform instantly protect your endpoints before unknown threats can cause harm.
Trusted by Security Leaders Worldwide
Book your personalized demo now and see how Xcitium protects you before threats strike.
Common questions about Endpoint Detection and Response
Learn more about cybersecurity and endpoint protection
When you visit any website, it may store or retrieve information on your browser, mostly in the form of cookies. This information might be about you, your preferences or your device and is mostly used to make the site work as you expect it to. The information does not usually directly identify you, but it can give you a more personalized web experience. Because we respect your right to privacy, you can choose not to allow some types of cookies. Click on the different category headings to find out more and change our default settings. However, blocking some types of cookies may impact your experience of the site and the services we are able to offer.
Lock In 10 Free Hours of Incident Response