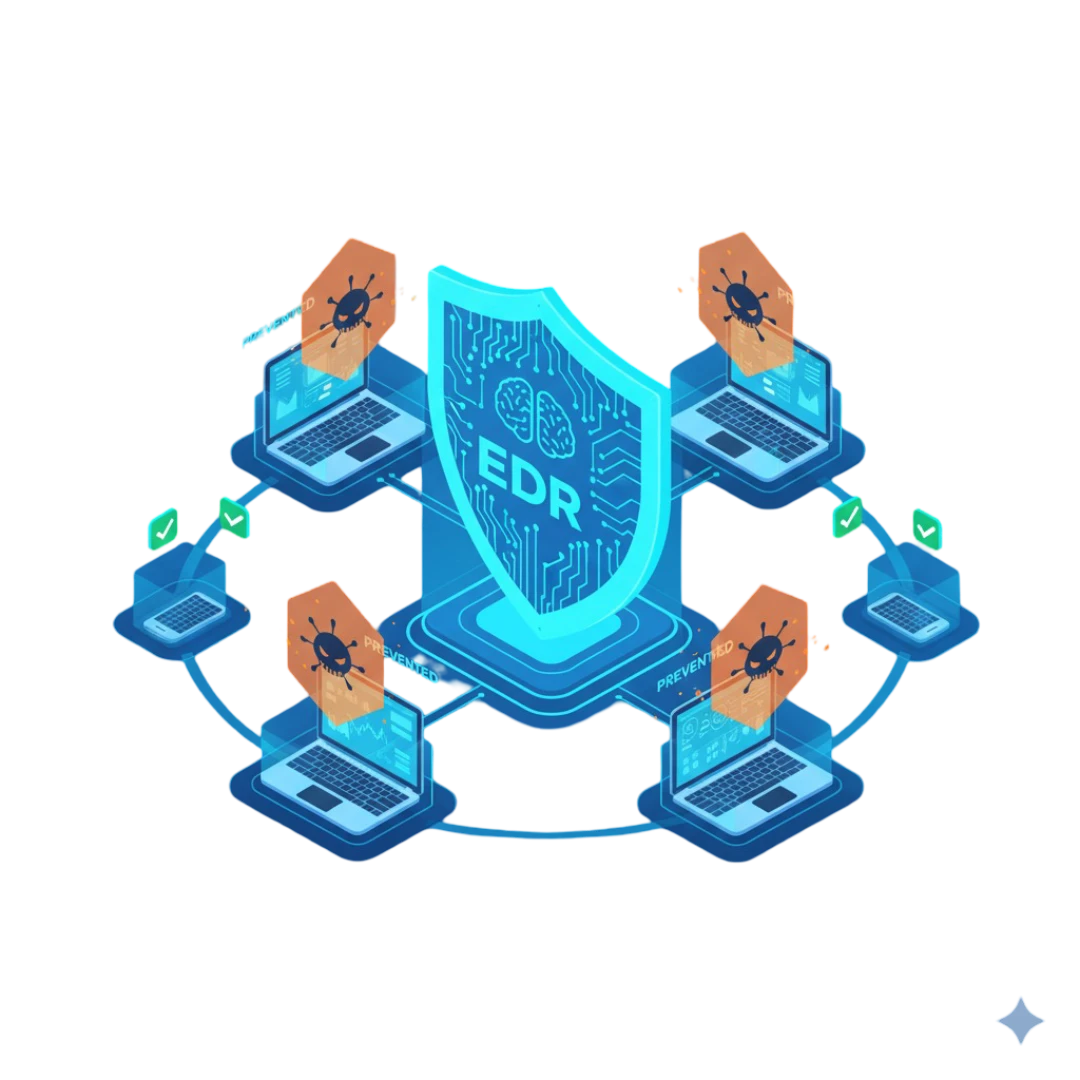
Comprehensive EDR Security Platform
Move beyond detection-centric tools. Xcitium’s EDR virtualizes unknown threats instantly, stops breaches before execution, and eliminates attacker dwell time across endpoints.

Move beyond detection-centric tools. Xcitium’s EDR virtualizes unknown threats instantly, stops breaches before execution, and eliminates attacker dwell time across endpoints.

Endpoint Detection and Response (EDR) security solutions comprehensively protect organizations from various cyber threats. By focusing on the endpoints, often the initial targets of cyberattacks, EDR systems provide multiple layers of security and deliver significant benefits. Here's a detailed look at some of the key advantages:
Real-Time Threat Detection and Response
One of the primary benefits of EDR security is its ability to provide real-time monitoring and detection of threats across all endpoint devices. Unlike traditional antivirus solutions that rely on signatures to detect known threats, EDR systems use advanced analytics, machine learning, and behavioral analysis to identify suspicious activities and potential threats. This means that even zero-day exploits and advanced persistent threats (APTs) can be detected. Once a threat is identified, EDR tools enable immediate response capabilities, such as isolating affected endpoints from the network to prevent the spread of malware or executing automated remediation processes to eliminate the threat.
Enhanced Visibility and Insight
EDR solutions offer unparalleled visibility into the endpoint environment. They continuously collect and analyze vast amounts of data from each endpoint, providing detailed insights into user activities, system processes, network communications, and file movements. This comprehensive visibility enables security teams to understand better the tactics, techniques, and procedures (TTPs) used by attackers, facilitating the early detection of complex threats that might otherwise go unnoticed. Enhanced visibility also aids in forensic investigations, allowing teams to trace the root cause of an incident and understand the full scope of a breach.
Improved Incident Response and Forensics
EDR tools streamline the incident response process by providing detailed forensic data and analysis tools. In the event of a security incident, responders can quickly access historical and real-time data from affected endpoints, enabling them to ascertain the extent of the breach, identify compromised systems, and understand how the attack was carried out. This information is crucial for effectively remediating threats, preventing future attacks, and meeting regulatory compliance requirements by demonstrating thorough investigation and response efforts.
Proactive Threat Hunting
Beyond reactive detection and response, EDR solutions empower security teams to hunt for hidden threats within their environment proactively. By leveraging the detailed data collected by EDR tools, threat hunters can search for indicators of compromise (IoCs) and investigate suspicious activities that may indicate a developing attack. This proactive approach helps organizations identify and mitigate threats before they can cause significant damage.
Reduction of Dwell Time
Dwell time, the period between the initial compromise and the threat detection is a critical metric in cybersecurity. The longer an attacker remains undetected in the network, the more damage they can inflict. EDR systems significantly reduce dwell time by detecting anomalies and threats in real time, enabling rapid containment and remediation. This minimizes the potential impact of an attack and reduces the overall risk to the organization.
Compliance and Regulatory Requirements
Many industries are subject to strict regulatory requirements that mandate the monitoring, reporting, and remedying of cybersecurity threats. EDR solutions can help organizations meet these requirements by providing detailed logs, reports, and audit trails of all endpoint activities. This documentation is essential for demonstrating compliance with regulations such as the General Data Protection Regulation (GDPR), the Health Insurance Portability and Accountability Act (HIPAA), and others.
Scalability and Integration
Modern EDR solutions are designed to scale with the growth of an organization's endpoint environment. They can easily integrate with other security tools and systems, such as Security Information and Event Management (SIEM) systems, to provide a unified approach to security. This integration enhances the overall effectiveness of the security posture by enabling a coordinated response to threats and streamlining the management of security operations.
EDR security offers many benefits, from real-time threat detection and enhanced visibility to improved incident response and regulatory compliance. By adopting EDR solutions, organizations can significantly improve their cybersecurity posture, reduce their risk of breaches, and ensure the continuous protection of their critical assets.
Selecting the right Endpoint Detection and Response (EDR) vendor is critical for organizations looking to bolster their cybersecurity posture. Here are vital factors to consider to ensure you choose the best EDR security vendor for your needs:
Detection and Response Capabilities
The heart of an EDR system lies in its ability to detect and respond to threats effectively. Assess the vendor's capabilities in identifying a wide range of threats, from malware and ransomware to sophisticated, state-sponsored attacks. Look for advanced features like behavioral analysis, anomaly detection, and AI-driven insights. The system should offer real-time response capabilities, allowing you to quickly isolate infected devices, block malicious activity, and remediate threats.
Integration with Existing Systems
Your EDR solution should seamlessly integrate with your existing security and IT infrastructure. This includes compatibility with other security solutions (firewalls, antivirus, and SIEM systems) and IT management tools. Proper integration enhances visibility across your network and streamlines response efforts. Check if the vendor supports standard integration protocols and provides APIs for custom integrations.
Scalability and Performance
Consider how well the EDR solution can scale with your organization. It should handle an increasing number of endpoints without significant performance degradation. Evaluate the impact of the EDR software on endpoint performance, ensuring it does not interrupt day-to-day operations or reduce system efficiency.
Usability and Management
The usability of the EDR platform is crucial for effective threat hunting and incident response. Look for a user-friendly interface that provides clear, actionable insights. The platform should offer comprehensive reporting and visualization tools for threat analysis and decision-making. Additionally, assess the system's management features, such as policy configuration, alert customization, and automated response actions.
Support and Training
Strong vendor support and comprehensive training are essential to successfully deploying and operating an EDR solution. Investigate the vendor's support structure, including availability, response times, and types of support offered (phone, email, online chat). Inquire about training resources and programs to ensure your team can use and maintain the EDR system effectively.
Reputation and Reliability
Research the vendor's reputation within the cybersecurity industry. Look for independent reviews, customer testimonials, and case studies. Consider the vendor's history, including how long they have been in business, financial stability, and track record for innovation and customer satisfaction.
Compliance and Legal Considerations
Ensure the EDR solution complies with relevant regulations and industry standards, such as GDPR, HIPAA, or PCI DSS. The vendor should provide features that support compliance efforts, including data encryption, access controls, and comprehensive logging and reporting capabilities.
Cost and Return on Investment
Evaluate the total cost of ownership of the EDR solution, including initial purchase costs, implementation fees, and ongoing maintenance expenses. Consider the potential return on investment, factoring in the costs associated with data breaches and cybersecurity incidents. A higher-priced solution may offer more excellent value if it significantly reduces the risk of costly security breaches.
By carefully considering these factors, organizations can choose an EDR vendor that meets their security needs and aligns with their business objectives, budget, and operational capabilities. The right EDR solution will enhance your cybersecurity defenses, enable rapid response to incidents, and provide valuable insights into threat activities on your endpoints.
Zero-day threats will enter your environment. Xcitium prevents them from executing, delivering zero infections and zero operational damage.
See Prevention in ActionWhen you visit any website, it may store or retrieve information on your browser, mostly in the form of cookies. This information might be about you, your preferences or your device and is mostly used to make the site work as you expect it to. The information does not usually directly identify you, but it can give you a more personalized web experience. Because we respect your right to privacy, you can choose not to allow some types of cookies. Click on the different category headings to find out more and change our default settings. However, blocking some types of cookies may impact your experience of the site and the services we are able to offer.
Lock In 10 Free Hours of Incident Response