Data Loss Prevention must be an integral component of any security strategy to safeguard against reputational losses from data leakage, whether credit card numbers, personally identifiable data, blueprints, source codes, etc.
The best DLP solutions protect data in transit and at rest by monitoring and filtering across networks, endpoints, cloud servers, and other sources.
Endpoint Management
Endpoint management is an indispensable component of an effective cybersecurity strategy, providing IT teams with a powerful tool to prevent cyberattacks. An endpoint management process ensures all devices on a network are up-to-date and patched, and monitored proactively for remediation purposes at scale. Furthermore, endpoint management helps strengthen an organization's security posture against potential attacks from cyber criminals, safeguarding data assets and systems against attacks by protecting all devices on its network from potential security breaches.
Maintaining visibility and control over endpoints on business networks can take time and effort. A unified Endpoint Management (UEM) console offers organizations a way to gain a holistic overview of registered endpoints on the network, including updates, patches, and issues arising. Furthermore, UEM can detect problems instantly as they arise and respond immediately, greatly increasing productivity and overall security.
One of the primary goals of endpoint management solutions for businesses is protecting personal devices used for work. With Bring Your Device (BYOD) practices becoming more widespread, employees may use personal devices to access corporate information. If compromised, such personal devices could expose an organization to privacy laws or regulations; with UEM solutions, companies can protect personal devices by creating a clear BYOD policy detailing how they will be managed within their organization and which apps and data can be accessed by employees.
Healthcare industries could also reap significant advantages from an endpoint management solution. Patient records, medical charts, and other critical information stored across numerous endpoints make the healthcare industry an easy target for hackers; using endpoint management solutions, healthcare organizations can create a consistent and secure environment without jeopardizing data integrity while giving employees sufficient access to perform their jobs efficiently.
Security should always remain at the forefront when considering endpoint management; however, user experience should be noticed. With software and hardware such as Intel vPro technology, ensuring efficient manageability and security processes that do not impede device performance or interfere with employee productivity is possible.
Network Management
Network management refers to the practice of overseeing and overseeing your company's computer network, from configuring hardware and software, monitoring performance, and troubleshooting issues all the way through to prevent downtime caused by outages. Network management is integral in keeping businesses connected and helps prevent costly downtime due to network outages.
Network administration can also play an integral part in protecting businesses against cyberattacks. By closely monitoring network traffic and usage patterns, administrators can detect anomalies that could indicate an attack on sensitive data. By taking swift action when they notice any possible breaches or issues with network performance, administrators can help mitigate their effects while keeping sensitive information safe.
Network management solutions can also identify and prevent the unlawful sharing or use of sensitive information across on-premises systems and cloud applications, including accidental or malicious transfer via email, instant messaging, file storage systems, and endpoint devices.
The best network management solutions provide a full suite of tools, including centralized network management, storage DLP, and endpoint DLP. Each feature specializes in different components of information protection while working together for maximum effect.
Network DLP solutions typically utilize content inspection and contextual analysis to detect and stop any unauthorized movement of sensitive information. For instance, such solutions might detect attempts to copy encrypted files from workstations to a file share and alert IT. From there, appropriate steps might be taken, such as notifying device owners of potential breaches or encrypting sensitive files to limit access.
Network DLP plays an essential role in upholding regulations such as HIPAA or GDPR. These solutions can detect activities that violate these standards and report on them to provide evidence of regulatory compliance.
As you evaluate network DLP solutions, note whether they are part of an all-encompassing data protection suite or function as a standalone tool. DLP should always follow an established information governance program; standalone solutions without adequate policies and procedures could produce false alerts that obstruct legitimate activities supporting business processes.

Cloud Management
Effectively managing public, private, and hybrid cloud environments requires an effective management strategy supported by tools that ensure security controls are in place and policies enforced. An ideal cloud management solution will support manual and automated processes while offering visibility across an organization's entire IT infrastructure to protect data in multi-cloud environments.
Data Loss Prevention, or DLP, is essential to an effective cybersecurity strategy. DLP software detects and monitors sensitive business data to prevent it from leaving an organization's network - either intentionally or accidentally. DLP identifies, classifies, and blocks transfers violating internal policies and compliance regulations such as GDPR, CCPA, HIPAA, PCI, and DSS.
DLP allows your organization to monitor how and where its data is utilized. DLP monitors incoming and outgoing transfer violations, looking for anomalies indicating unauthorized data movement. Furthermore, it tracks changes in cloud users and configurations to maintain compliance.
DLP uses machine learning and human-in-the-loop analytics to protect your organization's most valuable assets. It identifies and classifies sensitive information before managing it across systems and clouds - never letting any data out of one central control point.
DLP software provides another layer of protection by encrypting sensitive data at rest, protecting against accidental exposure by inexperienced end users and malicious insiders exfiltrating data through its single set of policies and workflows you set up through one centralized console.
DLP should be part of your cloud management strategy because even minor security incidents can devastate your business. A data breach could cost your customer's trust, brand reputation, and possibly its existence - not to mention regulatory fines! Integrated threat detection in DLP solutions helps prevent breaches from ever occurring by detecting suspicious activity from well-meaning insiders and malicious outsiders; advanced encryption prevents unauthorized third parties from accessing sensitive data even in the event of successful breaches.
Threat Detection
Threat detection refers to recognizing cyber-attacks that attempt to gain entry to a machine or network. Such threats could include emails containing viruses, ransomware attacks, or any other attack that steals sensitive information or disrupts operations. Solutions designed for threat detection typically analyze behavior that deviates from an established baseline to detect potential risks and notify teams as quickly as possible.
Threat detection systems allow businesses to stop attacks before they cause significant harm or disrupt business operations. A threat detection system may also help stop data exfiltration by notifying IT teams of suspicious movement, encryption, or removal from endpoints for safety from unauthorized access, deletion, and sharing.
Threat detection systems use raw log data combined with threat intelligence feeds as reference material to detect malicious activity, reducing false positives so security teams can focus their time on real threats instead.
As well as monitoring known threat patterns, some systems employ heuristics and advanced analytics to detect potentially problematic behavior. This method uses active identification of threats by analyzing machine and application behavior and traffic patterns that deviate from the norm, such as network connections or downloaded files.
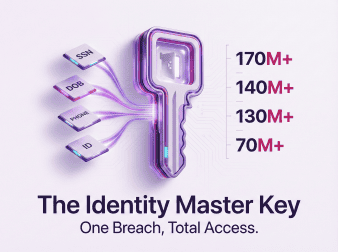
Other forms of cyberattacks target specific data points, including personally identifiable information (PII) or financial details like credit card or bank account numbers. Such information could be used for various purposes, from accessing corporate bank accounts for unlawful withdrawals to stealing identities and engaging in fraud schemes.
Cyberattacks generally target companies by breaching their security perimeter and infiltrating internal systems or networks, then installing malicious software or phishing tools to collect personal and other sensitive information for later transfer over the Internet into servers, databases, or cloud storage solutions.
An effective data loss prevention solution must include threat detection and monitoring to safeguard sensitive information and systems against cyberattacks and other security threats while providing solutions for mitigating these threats.