A computer vulnerability is a cybersecurity term that refers to a defect in a system that can leave it open to attack. This vulnerability could also refer to any type of weakness present in a computer itself, in a set of procedures, or in anything that allows information security to be exposed to a threat.
It is possible for network personnel and computer users to protect computers from vulnerabilities by regularly updating software security patches. These patches are capable of solving flaws or security holes found in the initial release. Network personnel and computer users should also stay informed about current vulnerabilities in the software they use and look out for ways to protect against them.
Common Computer Security Vulnerabilities
The most common computer vulnerabilities include:
- Bugs
- Weak passwords
- Software that is already infected with virus
- Missing data encryption
- OS command injection
- SQL injection
- Buffer overflow
- Missing authorization
- Use of broken algorithms
- URL redirection to untrusted sites
- Path traversal
- Missing authentication for critical function
- Unrestricted upload of dangerous file types
- Dependence on untrusted inputs in a security decision
- Cross-site scripting and forgery
- Download of codes without integrity checks
Causes And Harms Of Computer Security Vulnerabilities
Computer security vulnerabilities exist because programmers fail to fully understand the inner programs. While designing and programming, programmers don’t really take into account all aspects of computer systems and this, in turn, causes computer vulnerability. Some programmers program in an unsafe and incorrect way, which worsens computer vulnerability.
The harm of computer vulnerability can be presented in several aspects, for example, the disclosure of confidential data, and widespread of Internet virus and hacker intrusion, which can cause great harm to enterprises and individual users by bringing about major economic loss. With the steady improvement of the degree of information, very severe computer security vulnerabilities can become a threat to national security in the aspects of economy, politics, and military.
Computer security vulnerability can harm five kinds of system securities that include: Reliability, confidentiality, entirety, usability, and undeniableness.
- Reliability: This refers to reducing incorrect false alarm in the operation of a computer system and enhancing the efficiency of a computer system.
- Confidentiality: This refers to protecting users’ information from disclosure and getting by unauthorized third party.
- Entirety: This system security requires that information or programs should not be forged, tampered, deleted or inserted deliberately in the process of storing, operation and communication. In other words, information or programs cannot be lost or destroyed.
- Usability: This ensures that users can enjoy the services offered by computers and information networks.
- Undeniableness: This security refers to guaranteeing information actors to be responsible for their behavior.
Use Endpoint Security To Protect All Endpoints
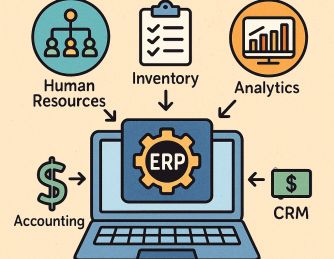
Endpoint Security also known as Endpoint Protection is a centralized approach that focuses on protecting all endpoints – desktops, laptops, servers, smartphones, and several other IoT devices – connected to the corporate IT network from cyber threats. This methodology enables effective, efficient, and easier security management. Some vendors offer Endpoint Security systems that include free firewall, antivirus, and other high defined security software.
Need Vulnerability Protection?
- Antivirus: Features multiple technology-based automatic detection, cleansing and quarantining of suspicious files to remove viruses and malware.
- Xcitium Firewall: Offers high-level security against outbound and inbound threats, manages network connections, and blocks personal data transmission by malicious software.
- Web URL Filtering: Advanced interface to create rules as needed – user-specific, sweeping, or as granular as desired.
- Host Intrusion Protection System (HIPS): Monitors vital operating system activities to guarantee protection against malware intrusion.
- Containment with auto-sandboxing: All unrecognized applications and processes are auto-sandboxed to run in a restricted environment.
- File Lookup Services (FLS): Cloud-based instant analysis of strange files that checks file reputation against Xcitium’s master whitelist and blacklists.
- Viruscope (Behavior Analysis): Behavior of all processes are monitored for potential harmful action.