How Does the Principle of Least Privilege Work?
The Principle of Least Privilege (PoLP) works by ensuring that users, applications, and systems are granted only the minimum level of access necessary to perform their tasks. This approach reduces the risk of unauthorized access, data breaches, and privilege escalation attacks. In a typical IT environment, users are assigned roles and permissions based on their job functions. Instead of giving employees blanket administrative access, PoLP enforces granular permissions, limiting their access to specific systems, files, or applications required for their tasks.For example, a financial analyst may need access to budgeting software but should not have administrative control over the company’s IT infrastructure. Similarly, a software developer may require access to a testing environment but not the production servers. By restricting access, PoLP minimizes the potential damage caused by compromised credentials, insider threats, or accidental misconfigurations.
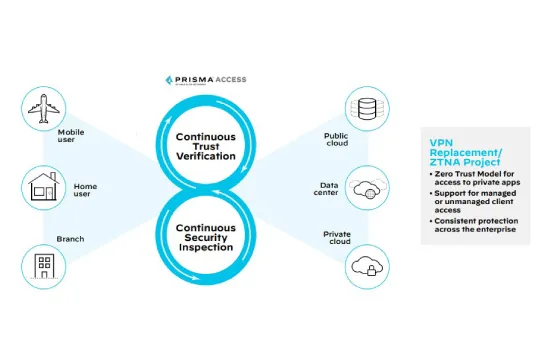
PoLP is implemented through a combination of role-based access control (RBAC),access control lists (ACLs),and identity and access management (IAM) solutions. RBAC assigns predefined permissions based on job roles, ensuring that users only have the necessary privileges for their specific responsibilities. ACLs define what actions a user or system can perform on a particular resource, restricting access based on predefined rules. IAM solutions automate and enforce PoLP policies across an organization, providing administrators with visibility and control over user access.
A key aspect of PoLP is privilege elevation and just-in-time (JIT) access. Instead of granting permanent administrative privileges, users or applications are temporarily granted elevated access only when needed and only for a limited duration. This reduces the risk of persistent access that attackers can exploit. Security teams can further enhance PoLP by implementing multi-factor authentication (MFA),monitoring user activities, and regularly auditing access rights to ensure they align with current job responsibilities.
PoLP also applies to system processes and applications. Operating systems and software should be configured to run with the least privilege necessary to perform their functions, limiting potential damage from vulnerabilities or malware exploitation. For example, web browsers and email clients should not operate with administrative privileges, as this could allow malicious code to execute with elevated permissions.
Regular reviews and adjustments are essential to maintaining PoLP. Organizations should continuously assess user roles, remove unnecessary privileges, and ensure that security policies are enforced consistently. By effectively implementing PoLP, businesses can strengthen their cybersecurity posture, protect sensitive data, and reduce the risk of security incidents.
Why Is PoLP Essential for Cybersecurity?
The Principle of Least Privilege (PoLP) is essential for cybersecurity because it minimizes security risks by restricting access to only what is necessary for users, applications, and systems. By limiting privileges, organizations reduce their attack surface, preventing cybercriminals from exploiting excessive permissions to access sensitive data or disrupt operations. Cyberattacks often succeed because users or applications have more access than they need, allowing hackers to move laterally within networks and escalate privileges. PoLP helps mitigate this risk by enforcing strict access controls.
One of the biggest cybersecurity threats is privilege escalation, where attackers exploit vulnerabilities to gain higher-level access. If a compromised user account has administrative privileges, the attacker can take full control of the system, deploy malware, or exfiltrate critical data. By implementing PoLP, organizations ensure that even if an account is compromised, the potential damage is limited. Users and applications operate with only the permissions necessary to perform their tasks, reducing the likelihood of a catastrophic breach.
PoLP also plays a crucial role in protecting against insider threats. Employees, contractors, or partners with excessive access can intentionally or accidentally cause security incidents. Limiting access to only job-related functions reduces the risk of data leaks, unauthorized changes, or fraud. Even well-intentioned employees can make mistakes, such as misconfiguring systems or clicking on phishing links. PoLP minimizes the impact of these errors by ensuring they do not have unnecessary administrative rights.
Compliance with cybersecurity regulations and frameworks such as GDPR, HIPAA, NIST, and ISO 27001 also requires enforcing PoLP. Many data protection standards mandate that organizations implement least privilege policies to safeguard sensitive information. Non-compliance can lead to hefty fines, legal consequences, and reputational damage. Implementing PoLP not only strengthens security but also ensures adherence to industry regulations.
Another advantage of PoLP is reducing the spread of malware and ransomware. Malicious software often relies on privileged access to propagate across networks and encrypt or steal data. If an infected user account has minimal privileges, the malware’s impact is contained, preventing widespread damage. This is particularly critical in environments where endpoint security must be tightly controlled.
Organizations implementing PoLP should also consider automation tools such as Identity and Access Management (IAM) and Privileged Access Management (PAM) to streamline enforcement. Continuous monitoring, access reviews, and multi-factor authentication further strengthen security. By adopting PoLP as a foundational cybersecurity practice, businesses can significantly enhance their defenses, mitigate risks, and ensure that users and systems operate securely without unnecessary privileges.
Automating PoLP with IAM and Security Tools
Automating the Principle of Least Privilege (PoLP) with Identity and Access Management (IAM) and security tools is critical for enforcing strict access controls while reducing administrative overhead. Managing access manually across an organization is time-consuming and prone to human error, which can lead to excessive permissions, security gaps, and compliance violations. By leveraging IAM solutions and security tools, businesses can streamline PoLP enforcement, ensuring users, applications, and systems only have the minimum level of access required to perform their tasks.
IAM solutions provide centralized identity management, authentication, and authorization, enabling organizations to define and enforce role-based and attribute-based access controls (RBAC and ABAC). These systems dynamically assign permissions based on job roles, project needs, or predefined policies, ensuring access privileges are automatically granted and revoked as needed. This prevents excessive permissions from accumulating over time, a common issue known as privilege creep. IAM also integrates with multi-factor authentication (MFA) and single sign-on (SSO) to add additional layers of security while maintaining user convenience.
Privileged Access Management (PAM) solutions complement IAM by securing and monitoring privileged accounts. PAM tools provide just-in-time (JIT) access provisioning, which temporarily elevates user privileges only when necessary and revokes them once the task is completed. This minimizes the risk of long-term privilege misuse and significantly reduces the attack surface for cybercriminals looking to exploit administrative accounts.
Automation further enhances PoLP enforcement by continuously monitoring access patterns, detecting anomalies, and responding to security threats in real-time. Behavioral analytics tools analyze user activity and flag suspicious behaviors, such as attempts to access restricted systems or sudden privilege escalations. Security Information and Event Management (SIEM) platforms integrate with IAM and PAM solutions to provide comprehensive visibility into access control activities and generate alerts for potential security incidents.
Cloud environments require specialized PoLP automation strategies. Cloud IAM tools, such as AWS IAM, Azure AD, and Google Cloud IAM, enforce least privilege policies across cloud services, preventing misconfigurations that could expose sensitive data. Infrastructure as Code (IaC) helps organizations define access policies in a consistent, repeatable manner, ensuring PoLP principles are applied at scale.
Automating PoLP with IAM and security tools enhances security posture, improves regulatory compliance, and reduces the administrative burden of managing access manually. By implementing automated least privilege controls, organizations can mitigate insider threats, prevent privilege escalation attacks, and ensure that users and applications operate with only the necessary permissions, strengthening overall cybersecurity resilience.