Types of Insider Threats
Insider threats come in various forms, each presenting unique challenges for organizations. Identifying the types of insider threats is the first step toward implementing effective detection and prevention strategies. Here are the most common types:
- Malicious Insider ThreatsMalicious insiders are individuals who intentionally harm an organization by exploiting their access to systems, data, or resources. These threats often stem from personal grievances, financial incentives, or allegiance to external parties. For example, an employee might sell sensitive data to a competitor or sabotage company systems to retaliate for perceived mistreatment. Malicious insider threats are particularly dangerous because these individuals already have legitimate access, making it harder to detect their activities until significant damage is done.
- Negligent Insider ThreatsNegligent insiders pose a threat due to careless actions or failure to follow security protocols. This group includes employees who inadvertently expose sensitive information by clicking on phishing emails, using weak passwords, or losing company devices. While these individuals may not have malicious intent, their lack of awareness or disregard for security measures can lead to severe consequences. Training and awareness programs are critical in minimizing this type of threat.
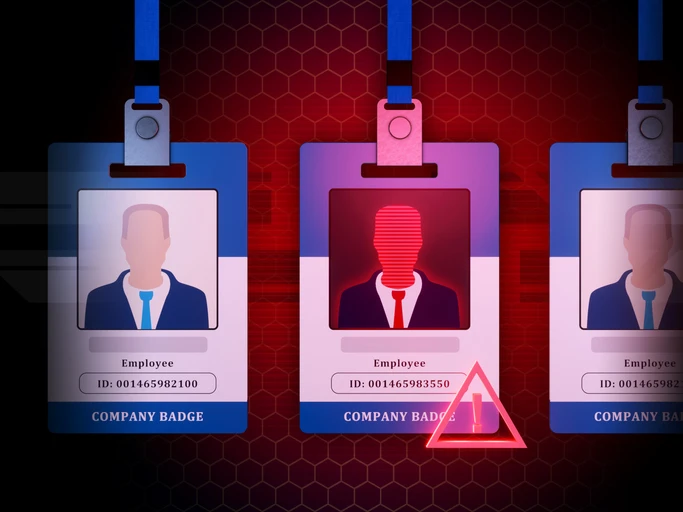
- Compromised InsidersCompromised insiders are employees whose accounts or credentials have been hijacked by external attackers. Cybercriminals often use tactics like phishing, social engineering, or malware to gain access to an employee’s account and then operate under their identity. Because the activity originates from a legitimate user account, it can be challenging to distinguish between genuine and malicious actions. Advanced detection tools and monitoring are essential to identifying unusual behavior patterns that could indicate a compromised insider.
- Third-Party Insider ThreatsOrganizations often rely on external contractors, vendors, or partners, granting them access to certain systems or data. Third-party insiders can become threats if their access is misused or if their security practices are lax. For instance, a vendor’s compromised credentials can provide a gateway for attackers to infiltrate your systems. Managing third-party access and conducting regular audits are crucial to minimizing this risk.
- Unintentional Insider ThreatsUnintentional insiders cause harm without even realizing it. For example, an employee may send sensitive data to the wrong recipient or unknowingly install malicious software. These incidents highlight the importance of secure processes and real-time detection mechanisms to prevent accidental breaches.
Common Signs of Insider Threats
Recognizing the signs of insider threats is crucial for safeguarding your organization’s sensitive data and systems. While insider threats can manifest in different ways, there are common behavioral and technical indicators that organizations should monitor. Here are the most common signs to watch for:
- Unusual Access PatternsOne of the most telling signs of an insider threat is unusual access behavior. This includes employees accessing systems or files outside of their normal job responsibilities, frequently working odd hours without justification, or repeatedly attempting to access restricted areas. For example, an accountant accessing customer databases or an IT administrator downloading large amounts of sensitive data could signal a potential issue.
- Data Hoarding or DownloadingEmployees who start collecting or downloading excessive amounts of data, especially before leaving the company, could be a red flag. This behavior is often seen in cases of data theft, where individuals plan to misuse the information for personal gain or to harm the organization. Monitoring data transfer volumes can help identify this sign early.
- Disgruntled BehaviorA change in an employee’s attitude or behavior, such as expressing dissatisfaction with the organization, colleagues, or leadership, can be an early warning sign of a potential insider threat. Disgruntled employees may feel justified in taking harmful actions, such as leaking sensitive information or sabotaging systems.
- Use of Unauthorized Devices or SoftwareInsiders who connect unauthorized devices to company networks or install unapproved software can pose a significant risk. These actions may indicate an attempt to bypass security controls, introduce malware, or exfiltrate data. Regularly monitoring and restricting device usage can mitigate this risk.
- Frequent Policy ViolationsRepeatedly ignoring or violating company policies, such as security protocols, acceptable use policies, or data handling procedures, can be a warning sign. For instance, an employee who shares login credentials or stores company data on personal devices may unintentionally or intentionally expose the organization to risks.
- Unexplained Financial ChangesInsiders involved in malicious activities, such as selling company data, may exhibit unexplained financial improvements, such as sudden increases in wealth. While not always directly indicative, financial red flags combined with other indicators warrant further investigation.
- Anomalies in Network ActivityTechnical anomalies, such as spikes in data transfer rates, frequent use of removable media, or accessing systems from unusual locations, can indicate insider threats. For example, an employee accessing the network from multiple geographic locations in a short period might suggest compromised credentials.
- Sudden Changes in Work HabitsEmployees who suddenly become secretive, start isolating themselves, or consistently refuse to collaborate on projects may be signaling a potential issue. Similarly, a high-performing employee who suddenly becomes disengaged or starts making uncharacteristic mistakes may require closer attention.
- Failed Login AttemptsRepeated login failures by an employee attempting to access restricted systems can indicate malicious intent or compromised credentials. Monitoring and investigating these attempts is key to addressing potential threats before they escalate.
Why Insider Threats Are Increasing in Modern Workplaces
The rise in insider threats is a growing concern for organizations across industries. Various factors, ranging from technological advancements to changes in workplace dynamics, have contributed to the increased prevalence of these threats. Here are the key reasons why insider threats are becoming more common in modern workplaces:
- Increased Remote Work and Hybrid ModelsThe shift to remote and hybrid work environments has expanded the attack surface for insider threats. Employees working from home may use unsecured devices or networks, making it easier for cybercriminals to compromise their accounts. Additionally, the lack of direct oversight in remote settings can lead to lax adherence to security protocols, increasing the likelihood of accidental or intentional breaches.
- Growing Use of Cloud-Based SystemsOrganizations are increasingly relying on cloud platforms to store and manage data. While these systems offer convenience and scalability, they also make sensitive information more accessible to insiders with malicious intent. The ease of data sharing and downloading in cloud environments makes it harder to control and monitor access.
- Rapid Employee TurnoverHigh employee turnover rates in today’s job market contribute to the insider threat landscape. Departing employees may take proprietary information or sensitive data with them, either out of negligence or with malicious intent. Organizations with weak offboarding processes are particularly vulnerable to such incidents.
- Advanced Social Engineering TacticsCybercriminals have become adept at using social engineering tactics to target employees and turn them into unintentional insiders. Phishing emails, fake IT support calls, and other schemes trick employees into divulging sensitive information or granting unauthorized access. These tactics are increasingly sophisticated and difficult to detect.
- Lack of Employee Awareness and TrainingMany employees are unaware of the role they play in organizational security. Insufficient training on identifying and avoiding potential threats leaves employees vulnerable to manipulation or accidental breaches. A lack of understanding about security policies can also lead to unintentional data leaks.
- Proliferation of Bring Your Own Device (BYOD) PoliciesThe widespread adoption of BYOD policies allows employees to use personal devices for work. While this increases convenience and flexibility, it also creates security challenges. Personal devices may not adhere to organizational security standards, making them easier targets for compromise.
- Economic and Financial StressEconomic uncertainty and financial pressures can motivate employees to engage in malicious activities. For instance, employees may sell sensitive data to competitors or hackers for financial gain. The stress caused by layoffs, pay cuts, or other financial hardships can increase the likelihood of insider threats.
- Increased Access to Sensitive InformationModern workplaces rely on interconnected systems that give employees access to a wide range of data and applications. While this access improves productivity, it also means that a single compromised account can have far-reaching consequences. Organizations that fail to enforce the principle of least privilege risk exposing sensitive data to unnecessary insider access.
- Sophisticated Insider Threat ActorsInsiders acting maliciously today are more sophisticated than ever. They often understand organizational systems and security measures intimately, allowing them to bypass traditional defenses. Some may even collaborate with external threat actors, amplifying the scope and impact of their actions.
- Inadequate Monitoring and Detection ToolsMany organizations lack the tools needed to effectively monitor for insider threats. Legacy systems and insufficient investments in security technology make it harder to detect unusual behavior or identify compromised accounts, allowing insider threats to go unnoticed for longer periods.