What is Hybrid Cloud Security?
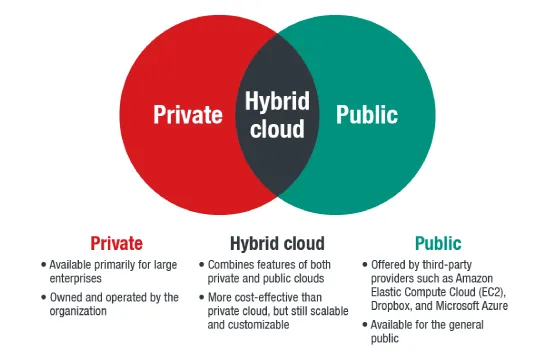
Hybrid cloud security refers to the strategies, technologies, and best practices designed to protect data, applications, and workloads operating across a hybrid cloud environment. A hybrid cloud combines on-premises infrastructure with public and private cloud services, offering organizations flexibility, scalability, and cost efficiency. However, this mixed environment also presents unique security challenges, as data and applications move between different platforms, each with its own security policies and vulnerabilities.
At its core, hybrid cloud security focuses on maintaining data integrity, preventing unauthorized access, and ensuring compliance with industry regulations. Because hybrid clouds span multiple environments, security must be consistent across all endpoints. This includes implementing access controls, encryption, identity and access management (IAM),and real-time threat detection. Without a unified security strategy, organizations risk exposure to cyber threats such as data breaches, ransomware, insider threats, and misconfigurations.
One of the key principles of hybrid cloud security is Zero Trust, which operates under the assumption that no user, device, or system should be trusted by default. This approach enforces strict authentication and authorization measures before granting access to any resources. Additionally, hybrid cloud security requires network segmentation to limit access to sensitive data, reducing the risk of lateral movement in case of a breach. Encryption plays a vital role in securing data at rest and in transit, ensuring that even if attackers gain access, the data remains protected.
Another important aspect is continuous monitoring and threat detection. With hybrid cloud environments being highly dynamic, organizations must deploy security solutions that provide real-time visibility into network traffic, user behavior, and potential vulnerabilities. Security Information and Event Management (SIEM) and Extended Detection and Response (XDR) tools help in detecting and mitigating threats before they cause significant damage.
Hybrid cloud security also involves securing workloads across different cloud providers. Many organizations use a combination of AWS, Microsoft Azure, and Google Cloud, each with its own security configurations. A robust hybrid cloud security strategy includes centralized policy management and automation to ensure consistency in security settings across all platforms.
Compliance is another major consideration, as businesses operating in regulated industries must adhere to standards such as GDPR, HIPAA, and PCI-DSS. Hybrid cloud security solutions help enforce compliance by maintaining audit logs, applying encryption, and monitoring for security policy violations.
Ultimately, hybrid cloud security enables organizations to leverage the benefits of hybrid cloud computing without compromising on security. By implementing a multi-layered defense strategy, businesses can ensure that their data and operations remain protected in an increasingly complex digital landscape.
Common Security Risks in Hybrid Cloud
Hybrid cloud environments offer organizations flexibility and scalability, but they also introduce a range of security risks due to their complexity and interconnected nature. Unlike a fully on-premises or purely cloud-based infrastructure, hybrid cloud deployments span multiple environments, each with different security policies, configurations, and potential vulnerabilities. Without a well-defined security strategy, businesses operating in a hybrid cloud model can be exposed to several common threats.
One of the primary security risks in hybrid cloud environments is misconfiguration. Cloud misconfigurations occur when security settings, permissions, or policies are improperly configured, leaving sensitive data and applications exposed to unauthorized access. This could include unsecured storage buckets, overly permissive access controls, or failure to enable encryption. Attackers often scan for such vulnerabilities to exploit weak points in an organization's infrastructure.
Data breaches are another major concern in hybrid cloud security. Since data frequently moves between on-premises and cloud environments, the risk of exposure increases if proper security controls are not in place. Weak encryption, inadequate access controls, and improper data handling can result in sensitive information being intercepted, stolen, or compromised. Cybercriminals often target hybrid cloud setups to exploit gaps in data security policies.
Insider threats pose a significant risk, as employees, contractors, or even malicious insiders with legitimate access to the hybrid cloud infrastructure can intentionally or unintentionally expose sensitive data. Without proper access control mechanisms such as role-based access control (RBAC) and least privilege policies, insider threats can lead to unauthorized data exposure, fraud, or sabotage.
Lack of visibility and monitoring across hybrid environments is another critical risk. Many organizations struggle to maintain real-time visibility into their security posture due to the complexity of managing multiple cloud providers and on-premises systems. Without centralized monitoring and threat detection tools, security teams may fail to detect unauthorized access, suspicious activity, or anomalies that could indicate a breach.
Compliance challenges also arise in hybrid cloud environments, especially for businesses subject to industry regulations such as GDPR, HIPAA, or PCI-DSS. Ensuring that security policies align across multiple platforms while maintaining compliance can be difficult. A lack of standardized security measures across cloud and on-premises environments can lead to regulatory violations and potential legal consequences.
Ransomware and cyberattacks are increasingly targeting hybrid cloud infrastructures. Attackers exploit vulnerabilities in cloud applications, insecure APIs, and weak authentication mechanisms to gain access to hybrid environments. Once inside, they can deploy ransomware, encrypt data, and demand payments, disrupting business operations and causing financial losses.
To mitigate these security risks, organizations must adopt a comprehensive hybrid cloud security strategy that includes encryption, continuous monitoring, Zero Trust policies, access controls, and automated security configurations. By proactively addressing these vulnerabilities, businesses can ensure that their hybrid cloud environments remain secure and resilient against evolving cyber threats.
Benefits of Hybrid Cloud Security
Hybrid cloud security provides organizations with a comprehensive approach to protecting data, applications, and workloads across both on-premises and cloud environments. By implementing strong security measures, businesses can take advantage of the flexibility and scalability of hybrid cloud computing without compromising data integrity, compliance, or operational resilience. A well-structured hybrid cloud security strategy offers several key benefits that enhance overall cybersecurity posture and business continuity.
One of the primary benefits of hybrid cloud security is enhanced data protection. Since hybrid cloud environments involve data moving between different infrastructures, robust security measures such as encryption, access controls, and data loss prevention (DLP) ensure that sensitive information remains secure both in transit and at rest. By encrypting data across all endpoints and enforcing strict access controls, businesses can prevent unauthorized access and minimize the risk of data breaches.
Another major advantage is increased flexibility and scalability. Hybrid cloud security enables organizations to seamlessly scale their security controls as workloads expand across multiple cloud providers and on-premises infrastructure. Security policies can be dynamically adjusted based on evolving business needs, ensuring consistent protection across all environments without slowing down operations. This flexibility is crucial for businesses undergoing digital transformation or experiencing rapid growth.
Hybrid cloud security also strengthens resilience against cyber threats. Implementing a Zero Trust architecture, which continuously verifies the legitimacy of users and devices before granting access, helps mitigate insider threats, unauthorized access, and credential-based attacks. Additionally, real-time monitoring and threat detection solutions, such as Security Information and Event Management (SIEM) and Extended Detection and Response (XDR),provide continuous visibility into security events, allowing businesses to detect and respond to threats before they escalate.
A well-executed hybrid cloud security strategy also supports regulatory compliance. Many industries must adhere to strict regulations such as GDPR, HIPAA, PCI-DSS, and CCPA, which require organizations to maintain secure data handling and storage practices. By implementing compliance-driven security policies across hybrid cloud environments, businesses can meet regulatory requirements, avoid legal penalties, and build trust with customers and stakeholders.
Another key benefit is cost efficiency. While maintaining on-premises infrastructure can be expensive, hybrid cloud security allows organizations to optimize costs by leveraging cloud-based security tools without completely discarding existing investments in on-premise security solutions. Cloud security services such as Cloud Security Posture Management (CSPM),Identity and Access Management (IAM),and Security Operations Centers (SOC) provide cost-effective solutions that reduce the need for expensive hardware and manual security operations.
Hybrid cloud security also enhances business continuity and disaster recovery. By implementing secure backup and recovery solutions, businesses can ensure that critical data and applications remain available even in the event of a cyberattack, system failure, or natural disaster. Cloud-based disaster recovery as a service (DRaaS) allows for rapid recovery and minimal downtime, ensuring seamless operations even in worst-case scenarios.
Ultimately, hybrid cloud security empowers organizations to harness the power of hybrid cloud computing while maintaining a strong cybersecurity posture. By integrating encryption, access controls, threat detection, and compliance measures into a unified security framework, businesses can achieve secure, scalable, and resilient cloud operations in an increasingly complex digital landscape.