What is Endpoint Behavior Analysis?
Endpoint Behavior Analysis is a cybersecurity approach that focuses on monitoring, detecting, and analyzing activities on an endpoint, such as a computer, server, or mobile device, to identify potential threats. Unlike traditional antivirus solutions that rely on known signatures to detect malware, Endpoint Behavior Analysis uses advanced techniques like artificial intelligence (AI),machine learning, and behavioral analytics to identify anomalies that may indicate a cyberattack. This method is particularly effective against zero-day threats, fileless malware, and advanced persistent threats (APTs),which often bypass signature-based detection.
At its core, Endpoint Behavior Analysis works by establishing a baseline of normal behavior for an endpoint. It continuously monitors system processes, network connections, file activities, and user actions to detect deviations from the expected patterns. When an unusual activity is detected—such as an unauthorized attempt to access sensitive files, a process executing a command that is out of the ordinary, or lateral movement within a network—the system generates an alert for further investigation or automatically takes preventive actions.
One of the key advantages of Endpoint Behavior Analysis is its ability to detect threats in real time. Traditional security solutions often fail to identify novel or polymorphic malware that has not yet been cataloged in a threat database. By focusing on behaviors rather than relying on predefined signatures, Endpoint Behavior Analysis can identify and respond to suspicious activities before they escalate into full-scale attacks.
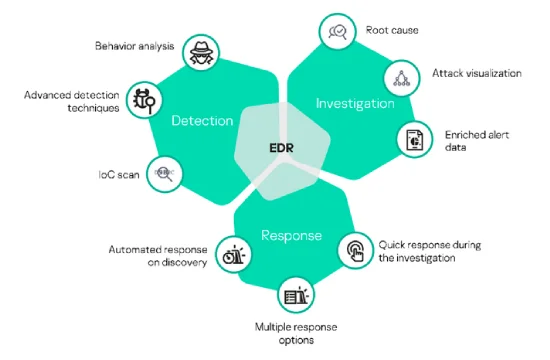
Another important aspect of Endpoint Behavior Analysis is its integration with other cybersecurity solutions. Many endpoint detection and response (EDR) and extended detection and response (XDR) platforms incorporate behavior-based analysis as a key feature to enhance their threat detection capabilities. When combined with threat intelligence, forensic analysis, and automated response mechanisms, Endpoint Behavior Analysis strengthens an organization's security posture and reduces the risk of breaches.
Organizations across various industries benefit from implementing Endpoint Behavior Analysis. In highly regulated sectors such as finance, healthcare, and government, where data breaches can have severe consequences, behavior-based security is essential for maintaining compliance and protecting sensitive information. Additionally, businesses facing growing threats from ransomware, phishing attacks, and insider threats can leverage this approach to identify potential risks before they cause damage.
Despite its benefits, Endpoint Behavior Analysis is not without challenges. False positives can occur, leading to unnecessary alerts that require manual investigation. Additionally, sophisticated attackers may attempt to mimic normal behaviors to evade detection. However, as AI and machine learning technologies continue to evolve, Endpoint Behavior Analysis is becoming more accurate and efficient, making it a critical component of modern cybersecurity strategies.
Key Features of Endpoint Behavior Analysis
Endpoint Behavior Analysis is a powerful cybersecurity technique that enhances threat detection by analyzing how endpoints interact with files, applications, and networks. It relies on a set of advanced features that help security teams detect and respond to potential threats before they can cause harm. These key features distinguish Endpoint Behavior Analysis from traditional security methods, making it an essential component of modern endpoint protection solutions.
One of the most critical features of Endpoint Behavior Analysis is real-time monitoring and detection. Unlike traditional antivirus programs that rely on signature-based detection, Endpoint Behavior Analysis continuously observes endpoint activity. This proactive approach allows security teams to identify potential threats as they emerge rather than waiting for malware definitions to be updated.
Another essential feature is anomaly detection and behavior baselining. The system first establishes a normal behavioral pattern for users, applications, and processes running on an endpoint. Once a baseline is set, it can detect deviations from expected behavior, such as unauthorized file modifications, unusual network traffic, or unexpected process executions. By identifying these anomalies, security teams can take immediate action before an attacker gains a foothold.
Machine learning and artificial intelligence (AI) integration further enhance Endpoint Behavior Analysis. These technologies help improve detection accuracy by continuously learning from previous incidents and adapting to evolving threats. AI-powered behavioral analysis can recognize patterns in large datasets, reducing false positives while ensuring that real threats are identified more effectively.
Another key feature is fileless attack detection. Traditional security tools often struggle with fileless malware, which operates entirely in memory and does not leave a trace on the disk. Endpoint Behavior Analysis identifies suspicious behavior, such as unauthorized PowerShell execution, registry modifications, or unusual script activity, allowing organizations to detect and neutralize fileless threats before they execute malicious payloads.
Endpoint Behavior Analysis also offers automated threat response and mitigation. When an anomaly is detected, the system can trigger automated responses, such as isolating the affected endpoint, blocking a suspicious process, or alerting security teams. This feature minimizes response times and prevents potential damage from spreading across the network.
Finally, integration with other security solutions enhances the effectiveness of Endpoint Behavior Analysis. Many organizations combine it with Endpoint Detection and Response (EDR),Extended Detection and Response (XDR),and Security Information and Event Management (SIEM) systems to create a comprehensive cybersecurity strategy. This seamless integration ensures that threat intelligence is shared across platforms, improving overall visibility and incident response.
By leveraging these key features, Endpoint Behavior Analysis provides organizations with a proactive, intelligent, and adaptive security approach. As cyber threats continue to evolve, the ability to detect, analyze, and respond to endpoint behaviors in real time is crucial for maintaining a strong security posture.
Benefits of Endpoint Behavior Analysis for Cybersecurity
Endpoint Behavior Analysis provides numerous benefits for cybersecurity, helping organizations detect, prevent, and respond to advanced threats more effectively. By leveraging behavioral analytics, machine learning, and real-time monitoring, this approach strengthens endpoint security and mitigates risks that traditional security solutions often miss. Below are some of the key benefits of Endpoint Behavior Analysis for cybersecurity.
One of the most significant benefits is early threat detection and prevention. Traditional security solutions primarily rely on signature-based detection, meaning they can only identify known threats. Endpoint Behavior Analysis, however, focuses on monitoring behaviors rather than static signatures. This allows security teams to detect anomalies and suspicious activities, even if the malware or attack method has never been seen before. This proactive approach helps prevent zero-day attacks, fileless malware, and advanced persistent threats (APTs) before they can cause damage.
Another major advantage is real-time monitoring and response. Endpoint Behavior Analysis continuously tracks processes, network connections, and user behaviors, immediately flagging deviations from normal patterns. When a potential threat is detected, the system can trigger automated responses, such as isolating the affected endpoint, terminating a suspicious process, or alerting security teams. This reduces response times and minimizes the impact of cyber incidents.
Improved accuracy and reduced false positives are also key benefits. Unlike traditional security tools that may generate excessive false alerts due to rigid rule-based detection, Endpoint Behavior Analysis leverages machine learning and AI to improve accuracy. Over time, the system refines its understanding of normal and abnormal behaviors, reducing unnecessary alerts while ensuring genuine threats are identified. This helps security teams focus their efforts on actual incidents rather than wasting time investigating false positives.
Endpoint Behavior Analysis also enhances protection against insider threats. Many security breaches originate from within an organization, whether due to malicious intent or human error. Since this approach monitors all endpoint activity, it can detect suspicious behaviors such as unauthorized access to sensitive data, abnormal login attempts, or the use of unapproved applications. This allows organizations to identify potential insider threats before they escalate into major security incidents.
Another key benefit is better visibility into endpoint activity. Endpoint Behavior Analysis provides security teams with detailed insights into how users, applications, and devices interact with systems. This visibility helps identify vulnerabilities, detect lateral movement within networks, and provide forensic evidence in the event of an attack.
Finally, seamless integration with existing security tools strengthens an organization’s overall cybersecurity posture. Endpoint Behavior Analysis can work alongside Endpoint Detection and Response (EDR),Extended Detection and Response (XDR),and Security Information and Event Management (SIEM) solutions. This integration ensures that security teams have a comprehensive view of threats across their entire infrastructure, improving incident response and risk management.
By implementing Endpoint Behavior Analysis, organizations gain a proactive, intelligent, and adaptive security layer that protects against evolving cyber threats. Its ability to detect advanced attacks, minimize response times, and improve security accuracy makes it a crucial component of modern cybersecurity strategies.
Endpoint Behavior Analysis vs Traditional Endpoint Security
Endpoint Behavior Analysis and traditional endpoint security solutions take different approaches to protecting devices from cyber threats. While traditional endpoint security methods such as antivirus (AV) and signature-based detection have been the standard for many years, they struggle to keep up with modern threats. Endpoint Behavior Analysis (EBA) enhances security by detecting suspicious behaviors rather than relying on known threat signatures. Understanding the differences between these two approaches can help organizations choose the best strategy to protect their endpoints.
One of the main differences between Endpoint Behavior Analysis and traditional endpoint security is detection methodology. Traditional security solutions use signature-based detection, which relies on databases of known malware signatures to identify threats. While this approach is effective for detecting well-documented threats, it fails against new, evolving, or unknown threats, such as zero-day exploits and advanced persistent threats (APTs). Endpoint Behavior Analysis, on the other hand, does not rely on predefined signatures. Instead, it continuously monitors system behavior, detecting anomalies that may indicate malicious activity, even if the threat has never been seen before.
Another key difference is proactive vs. reactive security. Traditional endpoint security tools react to known threats by blocking malware based on signature databases and heuristic analysis. However, attackers frequently modify their malware to bypass these defenses. Endpoint Behavior Analysis takes a proactive approach by identifying suspicious behaviors, such as unauthorized access attempts, unusual file modifications, or abnormal process executions. This allows security teams to respond to threats before they cause damage, reducing the likelihood of successful cyberattacks.
Protection against fileless malware is another area where Endpoint Behavior Analysis outperforms traditional security. Many modern threats, such as living-off-the-land attacks, leverage built-in system tools like PowerShell or Windows Management Instrumentation (WMI) to execute malicious activities without leaving a detectable file on disk. Traditional security solutions struggle to detect these threats because they do not involve known malicious files. Endpoint Behavior Analysis, however, monitors activity at the behavioral level and can detect unusual patterns, even if no malicious file is present.
Endpoint Behavior Analysis also provides real-time threat response and automation, whereas traditional endpoint security often relies on manual intervention. When a traditional security tool detects a potential threat, an administrator usually needs to investigate and take action. EBA solutions, however, can automatically isolate compromised endpoints, terminate suspicious processes, and generate alerts, significantly reducing response times and minimizing damage.
Additionally, false positive reduction is a major advantage of Endpoint Behavior Analysis. Traditional security solutions often produce false positives because they rely on static rules and pattern matching. Endpoint Behavior Analysis, powered by artificial intelligence (AI) and machine learning, continuously refines its understanding of normal behavior, leading to fewer false alerts and more accurate threat detection.
Integration with modern cybersecurity frameworks is another important factor. Traditional endpoint security tools operate in isolation, whereas Endpoint Behavior Analysis integrates with broader security ecosystems, including Endpoint Detection and Response (EDR),Extended Detection and Response (XDR),and Security Information and Event Management (SIEM) platforms. This allows security teams to correlate threat intelligence across multiple endpoints, improving overall visibility and incident response.
While traditional endpoint security solutions remain useful for detecting common threats, they are no longer sufficient on their own. Cybercriminals are using increasingly sophisticated techniques that evade signature-based detection. Endpoint Behavior Analysis provides a more advanced, proactive approach by continuously monitoring endpoint behaviors and identifying anomalies. By combining behavioral analysis with traditional security methods, organizations can strengthen their defenses and better protect against modern cyber threats.